In December 2023, KrebsOnSecurity revealed the real-life id of Rescator, the nickname utilized by a Russian cybercriminal who offered greater than 100 million cost playing cards stolen from Goal and Residence Depot between 2013 and 2014. Moscow resident Mikhail Shefel, who confirmed utilizing the Rescator id in a latest interview, additionally admitted reaching out as a result of he’s broke and in search of publicity for a number of new cash making schemes.
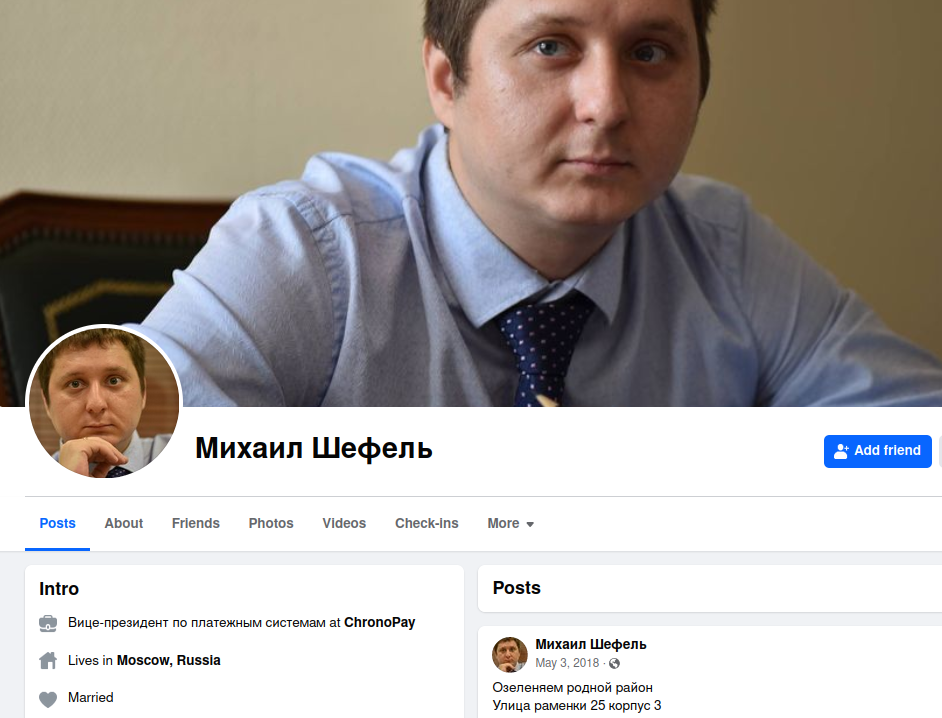
Mikhail “Mike” Shefel’s former Fb profile. Shefel has since legally modified his final title to Lenin.
Mr. Shefel, who just lately modified his authorized surname to Lenin, was the star of final yr’s story, Ten Years Later, New Clues in the Target Breach. That investigation detailed how the 38-year-old Shefel adopted the nickname Rescator whereas working as vice chairman of funds at ChronoPay, a Russian monetary firm that paid spammers to promote faux antivirus scams, male enhancement medication and knockoff prescribed drugs.
Mr. Shefel didn’t reply to requests for remark upfront of that December 2023 profile. Nor did he reply to reporting right here in January 2024 that he ran an IT firm with a 34-year-old Russian man named Aleksandr Ermakov, who was sanctioned by authorities in Australia, the U.Ok. and U.S. for stealing data on nearly 10 million customers of the Australian health insurance giant Medibank.
However not lengthy after KrebsOnSecurity reported in April that Shefel/Rescator additionally was behind the theft of Social Security and tax information from a majority of South Carolina residents in 2012, Mr. Shefel started contacting this writer with the pretense of setting the document straight on his alleged felony hacking actions.
In a sequence of reside video chats and textual content messages, Mr. Shefel confirmed he certainly glided by the Rescator id for a number of years, and that he did function a slew of internet sites between 2013 and 2015 that offered cost card knowledge stolen from Goal, Residence Depot and numerous different nationwide retail chains.
Shefel claims the true mastermind behind the Goal and different retail breaches was Dmitri Golubov, an notorious Ukrainian hacker often known as the co-founder of Carderplanet, among the many earliest Russian-language cybercrime boards targeted on cost card fraud. Mr. Golubov couldn’t be reached for remark, and Shefel says he not has the laptop computer containing proof to assist that declare.
Shefel asserts he and his workforce had been answerable for creating the card-stealing malware that Golubov’s hackers put in on Goal and Residence Depot cost terminals, and that on the time he was technical director of a long-running Russian cybercrime neighborhood known as Lampeduza.
“My nickname was MikeMike, and I labored with Dmitri Golubov and made applied sciences for him,” Shefel mentioned. “I’m additionally godfather of his second son.”

Dmitri Golubov, circa 2005. Picture: U.S. Postal Investigative Service.
Every week after breaking the story in regards to the 2013 knowledge breach at Goal, KrebsOnSecurity revealed Who’s Selling Cards from Target?, which recognized a Ukrainian man who glided by the nickname Helkern as Rescator’s authentic id. However Shefel claims Helkern was subordinate to Golubov, and that he was answerable for introducing the 2 males greater than a decade in the past.
“Helkern was my buddy, I [set up a] assembly with Golubov and him in 2013,” Shefel mentioned. “That was in Odessa, Ukraine. I used to be typically in that metropolis, and [it’s where] I met my second spouse.”
Shefel claims he made a number of hundred thousand {dollars} promoting playing cards stolen by Golubov’s Ukraine-based hacking crew, however that not lengthy after Russia annexed Crimea in 2014 Golubov lower him out of the enterprise and changed Shefel’s malware coding workforce with programmers in Ukraine.
Golubov was arrested in Ukraine in 2005 as a part of a joint investigation with a number of U.S. federal regulation enforcement businesses, however his political connections within the nation ensured his case went nowhere. Golubov later earned immunity from prosecution by turning into an elected politician and founding the Internet Party of Ukraine, which known as without spending a dime web for all, the creation of country-wide “hacker faculties” and the “computerization of all the financial system.”
Mr. Shefel says he stopped promoting stolen cost playing cards after being pushed out of the enterprise, and invested his earnings in a now-defunct Russian search engine known as tf[.]org. He additionally apparently ran a business called click2dad[.]net that paid individuals to click on on advertisements for Russian authorities employment alternatives.
When these enterprises fizzled out, Shefel reverted to promoting malware coding providers for rent beneath the nickname “Getsend“; this declare checks out, as Getsend for a few years marketed the identical Telegram deal with that Shefel utilized in our latest chats and video calls.
Shefel acknowledged that his outreach was motivated by a need to publicize a number of new enterprise ventures. None of these shall be talked about right here as a result of Shefel is already utilizing my December 2023 profile of him to promote what seems to be a pyramid scheme, and to remind others throughout the Russian hacker neighborhood of his expertise and accomplishments.
Shefel says he’s now flat broke, and that he at present has little to indicate for a storied hacking profession. The Moscow native mentioned he just lately heard from his ex-wife, who had learn final yr’s story about him and was abruptly questioning the place he’d hidden all of his earnings.
Extra urgently, Shefel wants cash to remain out of jail. In February, he and Ermakov had been arrested on expenses of working a short-lived ransomware associates program in 2021 known as Sugar (a.ok.a. Sugar Locker), which focused single computer systems and end-users as an alternative of companies. Shefel is because of face these expenses in a Moscow courtroom on Friday, Nov. 15, 2024. Ermakov was just lately discovered responsible and given two years probation.
Shefel claims his Sugar ransomware associates program was a bust, and by no means generated any income. Russia is thought for not prosecuting felony hackers inside its borders who scrupulously keep away from attacking Russian companies and shoppers. When requested why he now faces prosecution over Sugar, Shefel mentioned he’s sure the investigation was instigated by Pyotr “Peter” Vrublevsky — the son of his former boss at ChronoPay.
ChronoPay founder and CEO Pavel Vrublevsky was the important thing topic of my 2014 ebook Spam Nation, which described his position as head of one in all Russia’s most infamous felony spam operations.
Vrublevsky Sr. just lately declared chapter, and is at present in jail on fraud expenses. Russian authorities allege Vrublevsky operated a number of fraudulent SMS-based cost schemes. In addition they accused Vrublevsky of facilitating cash laundering for Hydra, the biggest Russian darknet market on the time. Hydra trafficked in unlawful medication and monetary providers, together with cryptocurrency tumbling for cash laundering, alternate providers between cryptocurrency and Russian rubles, and the sale of falsified paperwork and hacking providers.
Nevertheless, in 2022 KrebsOnSecurity reported on a more likely reason for Vrublevsky’s latest criminal charges: He’d been extensively documenting the nicknames, actual names and felony exploits of Russian hackers who labored with the safety of corrupt officers within the Russian Federal Safety Service (FSB), and working a Telegram channel that threatened to show alleged nefarious dealings by Russian monetary executives.
Shefel believes Vrublevsky’s son Peter paid corrupt cops to levy felony expenses in opposition to him after reporting the youth to Moscow police, allegedly for strolling round in public with a loaded firearm. Shefel says the Russian authorities advised the youthful Vrublevsky that he had lodged the firearms grievance.
In July 2024, the Russian information outlet Izvestia revealed a lengthy investigation into Peter Vrublevsky, alleging that the youthful son took up his father’s mantle and was answerable for promoting Sprut, a Russian-language narcotics bazaar that sprang to life after the Hydra darknet market was shut down by international law enforcement agencies in 2022.

Izvestia stories that Peter Vrublevsky was the promoting mastermind behind this 3D advert marketing campaign and others selling the Russian on-line narcotics bazaar Sprut.
Izvestia stories that Peter Vrublevsky is at present dwelling in Switzerland, the place he reportedly fled in 2022 after being “arrested in absentia” in Russia on expenses of working a violent group that may very well be employed through Telegram to conduct a spread of bodily assaults in actual life, together with firebombings and muggings.
Shefel claims his former accomplice Golubov was concerned within the improvement and dissemination of early ransomware strains, together with Cryptolocker, and that Golubov stays lively within the cybercrime neighborhood.
In the meantime, Mr. Shefel portrays himself as somebody who’s barely scraping by with the few odd coding jobs that come his manner every month. Extremely, the day after our preliminary interview through Telegram, Shefel proposed going into enterprise collectively.
By the use of instance, he recommended perhaps an organization centered round recovering misplaced passwords for cryptocurrency accounts, or maybe a sequence of on-line retail shops that offered low cost Chinese language items at a steep markup in the US.
“Hello, how are you?” he inquired. “Possibly we are able to open enterprise?”














