For the previous seven years, a malware-based proxy service often called “Faceless” has offered anonymity to numerous cybercriminals. For lower than a greenback per day, Faceless prospects can route their malicious visitors via tens of 1000’s of compromised techniques marketed on the service. On this submit we’ll look at clues left behind over the previous decade by the proprietor of Faceless, together with some which will assist put a face to the identify.
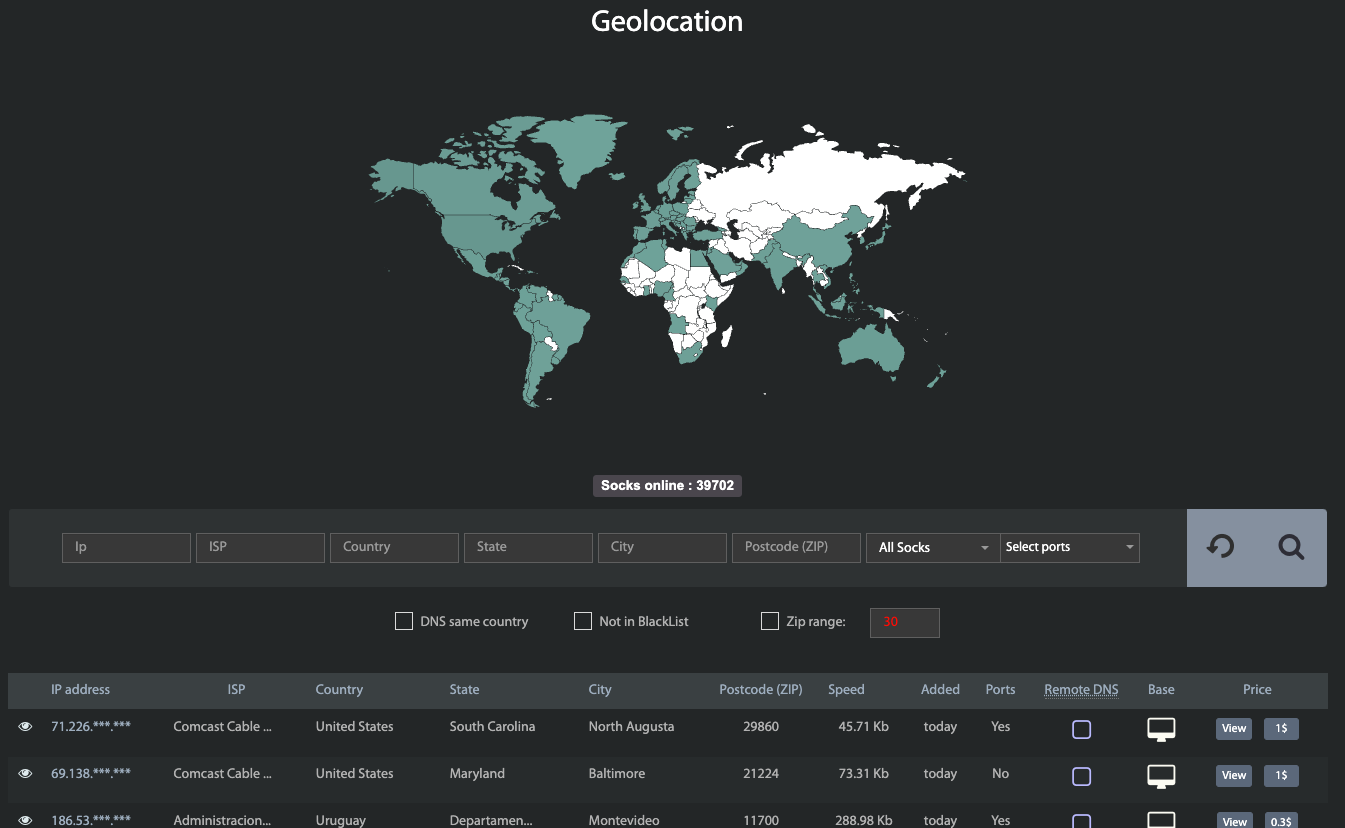
The proxy lookup web page contained in the malware-based anonymity service Faceless. Picture: spur.us.
Riley Kilmer is co-founder of Spur.us, an organization that tracks 1000’s of VPN and proxy networks, and helps prospects establish visitors coming via these anonymity companies. Kilmer mentioned Faceless has emerged as one of many underground’s most dependable malware-based proxy companies, primarily as a result of its proxy community has historically included a fantastic many compromised “Web of Issues” units — reminiscent of media sharing servers — which are seldom included on malware or spam block lists.
Kilmer mentioned when Spur first began wanting into Faceless, they seen nearly each Web handle that Faceless marketed for hire additionally confirmed up within the IoT search engine Shodan.io as a media sharing gadget on an area community that was one way or the other uncovered to the Web.
“We might reliably lookup the [fingerprint] for these media sharing units in Shodan and discover those self same techniques on the market on Faceless,” Kilmer mentioned.
In January 2023, the Faceless service web site mentioned it was prepared to pay for details about beforehand undocumented safety vulnerabilities in IoT units. These with IoT zero-days might count on cost if their exploit concerned not less than 5,000 techniques that could possibly be recognized via Shodan.
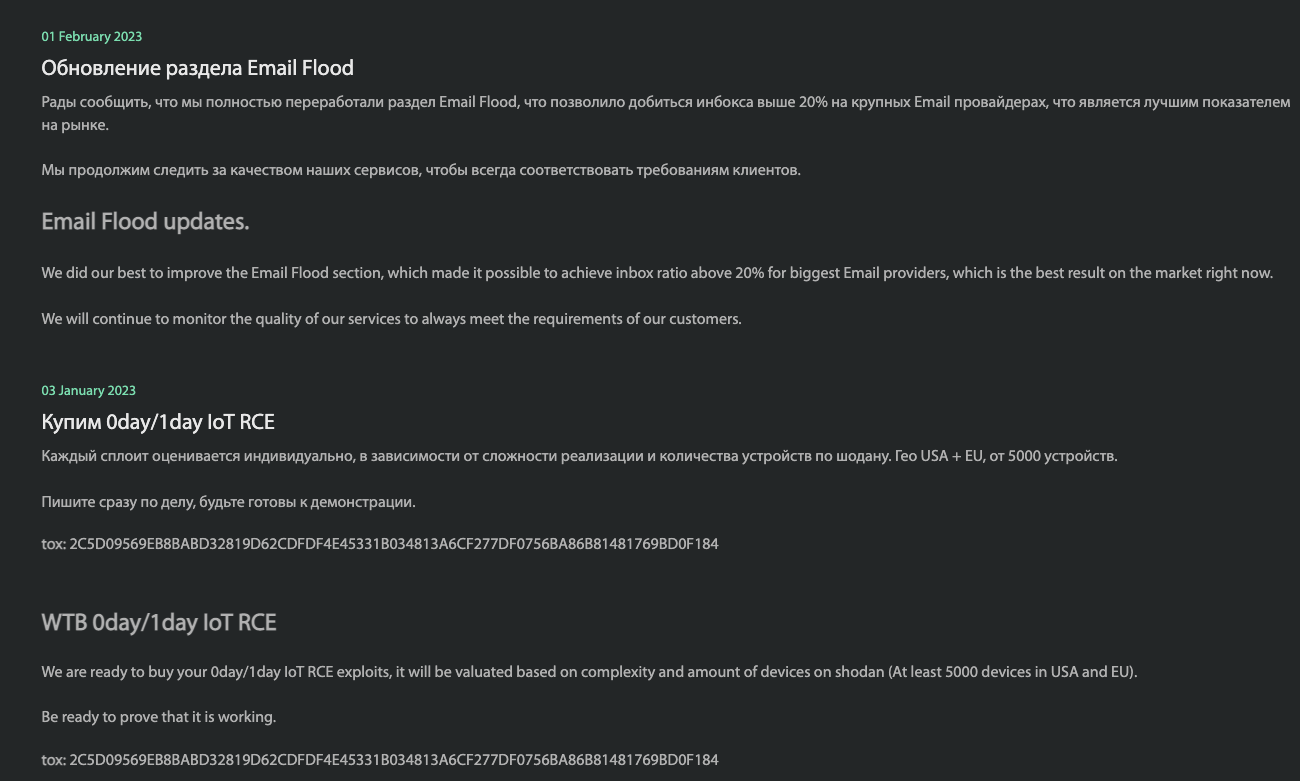
Notices posted for Faceless customers, promoting an e mail flooding service and soliciting zero-day vulnerabilities in Web of Issues units.
Lately, Faceless has proven ambitions past simply promoting entry to poorly-secured IoT units. In February, Faceless re-launched a service that lets customers drop an e mail bomb on somebody — inflicting the goal’s inbox to be crammed with tens of 1000’s of junk messages.
And in March 2023, Faceless began advertising and marketing a service for wanting up Social Safety Numbers (SSNs) that claims to supply entry to “the biggest SSN database available on the market with a really excessive hit price.”
Kilmer mentioned Faceless needs to turn into a one-stop-fraud-shop for cybercriminals who’re in search of stolen or synthetic identities from which to transact on-line, and a brief proxy that’s geographically near the id being offered. Faceless at present sells this bundled product for $9 — $8 for the id and $1 for the proxy.
“They’re attempting to be this one-stop store for anonymity and personas,” Kilmer mentioned. “The service mainly says ‘right here’s an SSN and proxy connection that ought to correspond to that consumer’s location and make sense to totally different web sites.’”
MRMURZA
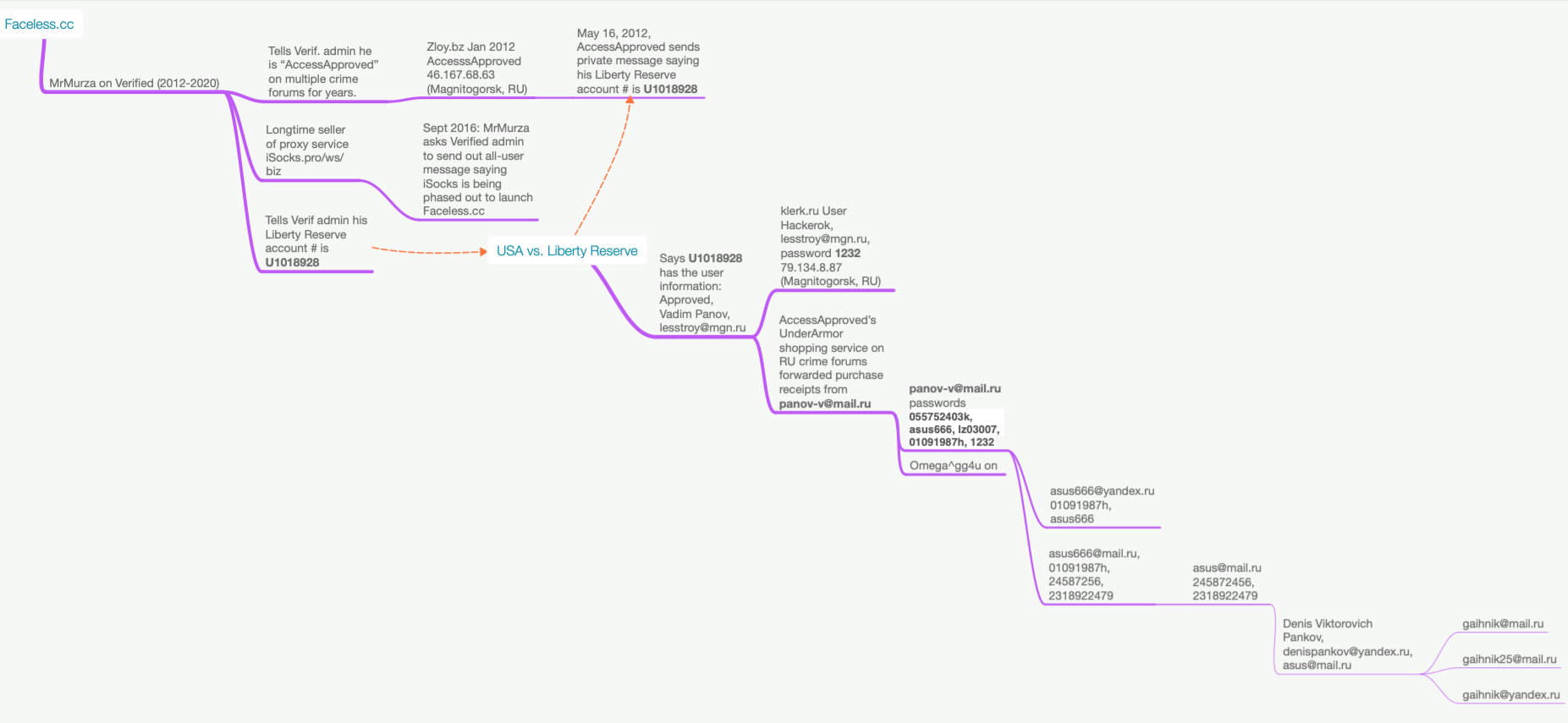
Faceless is a mission from MrMurza, a very talkative member of greater than a dozen Russian-language cybercrime boards over the previous decade. In keeping with cyber intelligence agency Flashpoint, MrMurza has been energetic within the Russian underground since not less than September 2012. Flashpoint mentioned MrMurza seems to be extensively concerned in botnet exercise and “drops” — fraudulent financial institution accounts created utilizing stolen id knowledge which are typically utilized in cash laundering and cash-out schemes.
Faceless grew out of a preferred anonymity service known as iSocks, which was launched in 2014 and marketed on a number of Russian crime boards as a proxy service that prospects might use to route their malicious Internet visitors via compromised computer systems.
Flashpoint says that within the months earlier than iSocks went on-line, MrMurza posted on the Russian language crime discussion board Verified asking for a critical companion to help in opening a proxy service, noting that they had a botnet that was powered by malware that collected proxies with a 70 p.c an infection price.
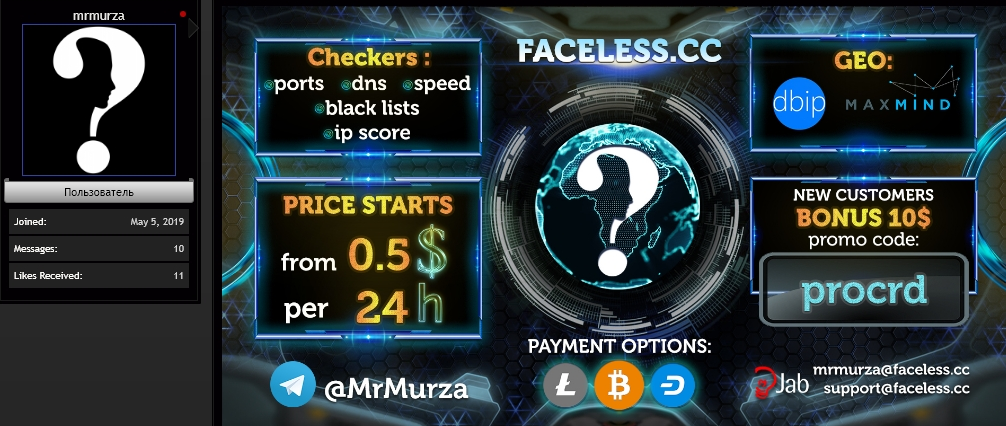
MrMurza’s Faceless marketed on the Russian-language cybercrime discussion board ProCrd. Picture: Darkbeast/Ke-la.com.
In September 2016, MrMurza despatched a message to all iSocks customers saying the service would quickly be phased out in favor of Faceless, and that current iSocks customers might register at Faceless totally free in the event that they did so rapidly — earlier than Faceless started charging new customers registration charges between $50 and $100.
Verified and different Russian language crime boards the place MrMurza had a presence have been hacked through the years, with contact particulars and personal messages leaked on-line. In a 2014 personal message to the administrator of Verified explaining his bona fides, MrMurza mentioned he obtained years of optimistic suggestions as a vendor of stolen Italian bank cards and a vendor of drops companies.
MrMurza advised the Verified admin that he used the nickname AccessApproved on a number of different boards through the years. MrMurza additionally advised the admin that his account quantity on the now-defunct digital foreign money Liberty Reserve was U1018928.
In keeping with cyber intelligence agency Intel 471, the consumer AccessApproved joined the Russian crime discussion board Zloy in Jan. 2012, from an Web handle in Magnitogorsk, RU. In a 2012 personal message the place AccessApproved was arguing with one other cybercriminal over a deal gone unhealthy, AccessApproved requested to be paid on the Liberty Reserve handle U1018928.
In 2013, U.S. federal investigators seized Liberty Reserve and charged its founders with facilitating billions of {dollars} in cash laundering tied to cybercrime. The Liberty Reserve case was prosecuted out of the Southern District of New York, which in 2016 revealed a list of account information (PDF) tied to 1000’s of Liberty Reserve addresses the federal government asserts had been concerned in cash laundering.
That doc signifies the Liberty Reserve account claimed by MrMurza/AccessApproved — U1018928 — was assigned in 2011 to a “Vadim Panov” who used the e-mail handle [email protected].
PANOV
Constella Intelligence, a menace intelligence agency that tracks breached databases, says [email protected] was used for an account “Hackerok” on the accounting service klerk.ru that was created from an Web handle in Magnitogorsk. The password chosen by this consumer was “1232.”
Along with promoting entry to hacked computer systems and financial institution accounts, each MrMurza and AccessApproved ran aspect hustles on the crime boards promoting clothes from in style retailers that refused to ship on to Russia.
On one cybercrime discussion board the place AccessApproved had clothes prospects, denizens of the discussion board created a prolonged dialogue thread to assist customers establish incoming emails related to numerous reshipping companies marketed inside their group. Reshippers are inclined to depend on a lot of individuals in the US and Europe serving to to ahead packages abroad, however in lots of instances the notifications about purchases and transport particulars can be forwarded to reshipping service prospects from a constant e mail account.
That thread mentioned AccessApproved’s clothes reshipping service forwarded affirmation emails from the handle [email protected]. This handle is related to accounts on two Russian cybercrime boards registered from Magnitogorsk in 2010 utilizing the deal with “Omega^gg4u.”
This Omega^gg4u id offered software program that may quickly test the validity of enormous batches of stolen bank cards. Apparently, each Omega^gg4u and AccessApproved additionally had one other area of interest: Reselling closely managed substances — reminiscent of human development hormone and anabolic steroids — from chemical suppliers in China.
A search in Constella on the handle [email protected] and lots of variations on that handle reveals these accounts cycled via the identical passwords, together with 055752403k, asus666, 01091987h, and the comparatively weak password 1232 (recall that 1232 was picked by whoever registered the [email protected] account at Klerk.ru).
Constella says the e-mail handle [email protected] relied on the passwords asus666 and 01091987h. The 01091987h password additionally was utilized by [email protected], which additionally favored the password 24587256.
Constella additional stories that whoever owned the a lot shorter handle [email protected] additionally used the password 24587256. As well as, it discovered the password 2318922479 was tied to each [email protected] and [email protected].
The e-mail addresses [email protected], [email protected], and [email protected] had been all used to register Vkontakte social media accounts for a Denis ***@VIP*** Pankov. There are a variety of different Vkontakte accounts registered to [email protected] and lots of variations of this handle underneath a special identify. However none of these different profiles seem tied to real-life identities.
PANKOV
Constella’s knowledge reveals the e-mail addresses [email protected] and [email protected] used the fairly distinctive password denis250485, which was additionally utilized by the e-mail handle [email protected] and nearly a dozen variations at different Russian-language e mail suppliers.
Russian car registration information from 2016 present the e-mail handle [email protected] belongs to Denis Viktorovich Pankov, born on April 25, 1985. That explains the “250485” portion of Pankov’s favored password. The registration information additional point out that in 2016 Pankov’s car was registered in a suburb of Moscow.
Russian incorporation information present that [email protected] is tied to IP Pankov Denis Viktorovich, a now-defunct transportation firm within the Volograd Oblast, a area in southern Russia that shares a protracted border with western Kazazkhstan.
Newer information for IP Pankov Denis Viktorovich present a microenterprise with this identify in Omsk that described its essential exercise as “retail sale by mail or through the Web.” Russian company information point out this entity was liquidated in 2021.
A reverse password search on “denis250485” through Constella reveals this password was utilized by greater than 75 e mail addresses, most of that are some variation of [email protected] — reminiscent of [email protected], or [email protected].
In 2012, somebody posted solutions to a questionnaire on behalf of Denis Viktorovich Pankov to a Russian-language dialogue discussion board on Chinese language crested canine breeds. The message mentioned Pankov was in search of a pet of a selected breed and was a resident of Krasnogorsk, a metropolis that’s adjoining to the northwestern boundary of Moscow.
The message mentioned Pankov was a then 27-year-old supervisor in an promoting firm, and could possibly be reached on the e mail handle [email protected].
GAIHNIK
Constella Intelligence reveals [email protected] registered on the now-defunct e mail advertising and marketing service Good Responder from an handle in Gagarin, which is about 115 miles west of Moscow.
Again in 2015, the consumer Gaihnik25 was banned from the net sport World of Tanks for violating the sport’s phrases that prohibit “bot farming,” or the automated use of enormous numbers of participant accounts to win some benefit that’s often associated to cashing out sport accounts or stock.
For the previous few years, somebody utilizing the nickname Gaihnik25 has been posting messages to the Russian-language hacking discussion board Gerki[.]pw, on dialogue threads relating to software program designed to “brute power” or mass-check on-line accounts for weak or compromised passwords.
A brand new member of the Russian hacking discussion board Nohide[.]Area utilizing the deal with Gaihnik has been commenting lately about proxy companies, credential checking software program, and the sale of hacked mailing lists. Gaihnik’s first submit on the discussion board involved personal software program for checking World of Tanks accounts.
The handle [email protected] reveals how so many e mail addresses tied to Pankov had been additionally related to apparently deceptive identities on Vkontakte and elsewhere. Constella discovered this handle was tied to a Vkontakte account for a Dmitriy Zakarov.
Microsoft’s Bing search engine says [email protected] belongs to 37-year-old Denis Pankov, but clicking the Mail.ru profile for that consumer brings up a profile for a a lot older man by the identify Gavril Zakarov. Nevertheless, if you log in to a Mail.ru account and think about that profile, it reveals that many of the account’s profile pictures are of a a lot youthful man.
Lots of those self same pictures present up in an online dating profile at dating.ru for the user Gaihnik, a.ok.a “Denchik,” who says he’s a 37-year-old Taurus from Gagarin who enjoys going for walks in nature, staying up late, and being on the Web.
Mr. Pankov didn’t reply to a number of requests for remark despatched to the entire e mail addresses talked about on this story. Nevertheless, a few of these addresses produced detailed error responses; Mail.ru reported that the customers [email protected], [email protected], and [email protected] had been terminated, and that [email protected] is now disabled.
Messages despatched to many different e mail addresses related through passwords to Pankov and utilizing some variation of asus####@mail.ru additionally returned comparable account termination messages.