You’ve in all probability by no means heard of “16Shop,” however there’s a superb likelihood somebody utilizing it has tried to phish you.

A 16Shop phishing web page spoofing Apple and focusing on Japanese customers. Picture: Akamai.com.
The worldwide police group INTERPOL said final week it had shuttered the infamous 16Shop, a well-liked phishing-as-a-service platform launched in 2017 that made it easy for even full novices to conduct complicated and convincing phishing scams. INTERPOL stated authorities in Indonesia arrested the 21-year-old proprietor and one in all his alleged facilitators, and {that a} third suspect was apprehended in Japan.
The INTERPOL assertion says the platform offered hacking instruments to compromise greater than 70,000 customers in 43 nations. Given how lengthy 16Shop has been round and what number of paying prospects it loved through the years, that quantity is nearly definitely extremely conservative.
Additionally, the sale of “hacking instruments” doesn’t fairly seize what 16Shop was all about: It was a totally automated phishing platform that gave its 1000’s of shoppers a collection of brand-specific phishing kits to make use of, and offered the domains wanted to host the phishing pages and obtain any stolen credentials.
Safety specialists investigating 16Shop discovered the service used an utility programming interface (API) to handle its customers, an innovation that allowed its proprietors to close off entry to prospects who did not pay a month-to-month charge, or for these making an attempt to repeat or pirate the phishing package.
16Shop additionally localized phishing pages in a number of languages, and the service would show related phishing content material relying on the sufferer’s geolocation.

Numerous 16Shop lures for Apple customers in numerous languages. Picture: Akamai.
For instance, in 2019 McAfee discovered that for targets in Japan, the 16Shop package would additionally acquire Internet ID and Card Password, whereas US victims might be requested for his or her Social Safety Quantity.
“Relying on location, 16Shop may even acquire ID numbers (together with Civil ID, Nationwide ID, and Citizen ID), passport numbers, social insurance coverage numbers, kind codes, and credit score limits,” McAfee wrote.
As well as, 16Shop employed numerous methods to assist its customers’ phishing pages keep off the radar of safety companies, together with a neighborhood “blacklist” of Web addresses tied to safety firms, and a characteristic that allowed customers to dam complete Web tackle ranges from accessing phishing pages.
The INTERPOL announcement doesn’t title any of the suspects arrested in reference to the 16Shop investigation. Nevertheless, plenty of safety companies — together with Akamai, McAfee and ZeroFox, beforehand related the service to a younger Indonesian man named Riswanda Noor Saputra, who offered 16Shop underneath the hacker deal with “Devilscream.”
In keeping with the Indonesian safety weblog Cyberthreat.id, Saputra admitted being the administrator of 16Shop, however instructed the publication he handed the challenge off to others by early 2020.
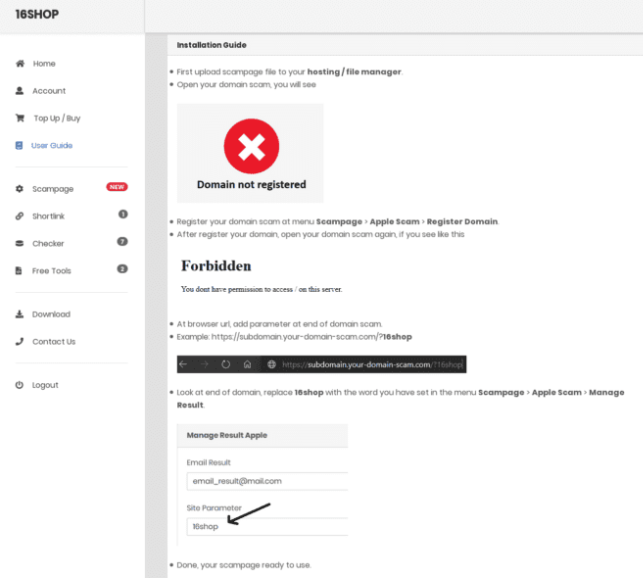
16Shop documentation instructing operators on how you can deploy the package. Picture: ZeroFox.
Nonetheless, Cyberthreat reported that Devilscream was arrested by Indonesian police in late 2021 as a part of a collaboration between INTERPOL and the U.S. Federal Bureau of Investigation (FBI). Nonetheless, researchers who tracked 16Shop since its inception say Devilscream was not the original proprietor of the phishing platform, and he might not be the final.
RIZKY BUSINESS
It’s not unusual for cybercriminals to accidentally infect their own machines with password-stealing malware, and that’s precisely what appears to have occurred with one of many newer directors of 16Shop.
Constella Intelligence, an information breach and risk actor analysis platform, now permits customers to cross-reference common cybercrime web sites and denizens of those boards with inadvertent malware infections by information-stealing trojans. A search in Constella on 16Shop’s area title exhibits that in mid-2022, a key administrator of the phishing service contaminated their Microsoft Home windows desktop pc with the Redline information stealer trojan — apparently by downloading a cracked (and secretly backdoored) copy of Adobe Photoshop.
Redline infections steal gobs of information from the sufferer machine, together with a listing of latest downloads, saved passwords and authentication cookies, in addition to browser bookmarks and auto-fill knowledge. These information point out the 16Shop admin used the nicknames “Rudi” and “Rizki/Rizky,” and maintained several Fb profiles underneath these monikers.
It seems this consumer’s full title (or a minimum of a part of it) is Rizky Mauluna Sidik, and they’re from Bandung in West Java, Indonesia. One in every of this consumer’s Fb pages says Rizky is the chief govt officer and founding father of an entity referred to as BandungXploiter, whose Facebook page signifies it’s a group centered primarily on hacking and defacing web sites.
A LinkedIn profile for Rizky says he’s a backend Internet developer in Bandung who earned a bachelor’s diploma in data know-how in 2020. Mr. Rizky didn’t reply to requests for remark.
















