Ukraine has turn into the battleground for a cyber onslaught, with the NoName ransomware assault claiming duty for a collection of assaults on varied entities.
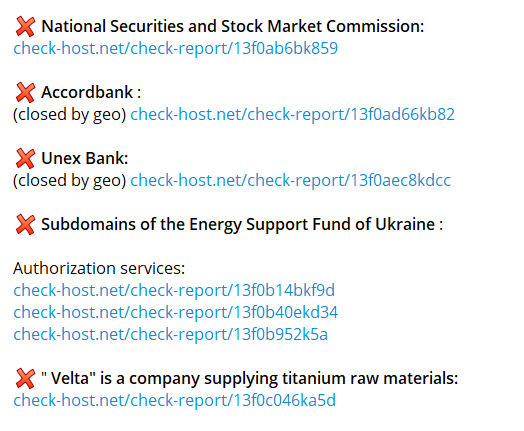
The NoName ransomware assault has particularly focused outstanding organizations in Ukraine, as revealed by the menace actor on their darkish internet portal. The listing contains the Nationwide Securities and Inventory Market Fee, Accordbank, Unex Financial institution, Vitality Neighborhood, and VELTA.
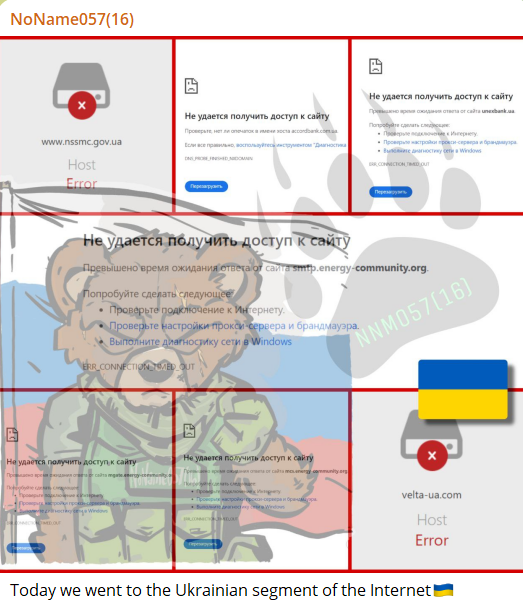
The dark web message from the menace actor reads, “Right this moment we went to the Ukrainian phase of the web,” indicating a brazen intrusion into the nation.
NoName Ransomware Assault
The NoName ransomware group additional substantiated their claims by posting hyperlinks to check-host.web stories for every focused entity. Nonetheless, the authenticity of those NoName ransomware cyberattack claims stays unverified at the moment.
The Cyber Express has reached out to the affected organizations for affirmation, but no official statements or responses have been acquired as of the time of writing.
Including to the complexity of the scenario, the entities listed on the menace actor’s portal look like operational and present no fast indicators of the alleged cyberattack. This uncertainty heightens the problem of verifying the legitimacy of the NoName ransomware cyberattacks on Ukraine.
NoName057(16), the pro-Russian hacker group behind the cyber onslaught, has a historical past of concentrating on Ukrainian, American, and European web sites belonging to authorities companies, media, and personal firms. Described as an unorganized but free pro-Russian activist group, NoName057(16) seeks consideration in Western nations via its disruptive cyber activities.
The rise of NoName Ransomware Group
The group first emerged in March 2022, orchestrating Distributed Denial of Service (DDoS) attacks on Ukrainian information and media web sites, resembling Zaxid and Fakty UA. Their motivations are rooted in silencing voices perceived as anti-Russian, reflecting the broader geopolitical tensions within the area.
Working via Telegram channels, NoName057(16) makes use of GitHub to host its DDoS software web site and related repositories. The group has developed a DDoS software named DDOSIA, designed to execute denial-of-service assaults by inundating goal websites with repeated network requests.
Inside the international hacking collective panorama, NoName057(16) is a comparatively new entrant with a definite deal with disrupting Ukrainian digital infrastructure. Their prominence rose after a collection of cyberattacks on authorities web sites on the eve of the 2023 G20 Summit in India, marking a pivotal second of their operations.
Media Disclaimer: This report relies on inner and exterior analysis obtained via varied means. The knowledge supplied is for reference functions solely, and customers bear full duty for his or her reliance on it. The Cyber Express assumes no legal responsibility for the accuracy or penalties of utilizing this data.
Associated
















