Within the context of the present digital surroundings, the API has was the life pressure of the digital world. They drive cellular purposes, interlink Saas, assist B2B integrations, and permit AI to speak with large quantities of information. APIs have grow to be extra essential to enterprise technique and innovation than they had been the technical enabling factors of the previous.
Nonetheless, there may be an equally possible and harmful growth of this new communication capability; information publicity and cybersecurity dangers. Knowledge has grow to be the brand new battleground within the sport of the API economic system, and cybersecurity ought to transition to grow to be a deep, systemic ingredient of the API lifecycle administration.
APIs: The Gateway to Trendy Enterprise and Threat
APIs are supposed to switch information, usually delicate information that providers and organizations need to commerce. APIs open up priceless info, which could be the monetary transactions, medical information, and buyer preferences. Sadly, they open new assault surfaces, as effectively.
The current reviews by the trade state that in the course of the previous 5 years, API-related infractions have grown greater than 300%. It’s no surprise, considering the truth that up to date digital platforms might rely on lots of, and even 1000’s of APIs, most of that are accessible to the Web neighborhood and aren’t sufficiently protected.
APIs are more and more focused by attackers not as a result of they’re flawed in idea, however as a result of conventional safety fashions weren’t designed to guard information flowing via them.
The New Menace Panorama: Why APIs Are Enticing Targets
The up to date API assaults are far more than stealing credentials. With enterprise logic as an exploitable safety threat, malicious actors use this to allow bypass authentication, to steal large information units on account of a mistakenly low charge restrict, and to focus on long-forgotten however nonetheless accessible and unused so-called zombie APIs. They moreover inject malicious payloads to be able to destabilize backend methods. These threats are fairly hidden and make use of logic gaps not detected by conventional firewalls and WAFs. Unauthorized utilization is the actual menace at the moment and never unauthorized entry.
Knowledge Publicity within the API Financial system: A Quiet Disaster
Opposite to the case with a breach inflicted by ransomware or malware, API information spillages are typically silent and prolonged. The information may very well be stolen in slender quantities little by little and it’s exceptionally exhausting to path. And in a lot of the high-profile circumstances, the organizations didn’t notice that their APIs had been the supply of the spillage of delicate information till it was out of hand.
Additionally in 2016, hackers had been in a position to breach the Uber repository information accessible in a personal GitHub profile to retrieve credentials to entry the API methods in Uber, compromising the small print of 57 million Uber customers and drivers. The associated fee? A value of 148 million, a settlement, and a spotlight all around the world.
These incidents underscore one fact: your APIs don’t simply serve information, they expose it. Each API is a window into your most crucial digital belongings.
Securing APIs: Extra Than Only a Guidelines
In a world the place APIs are the spine of digital transformation, defending them requires a multi-layered, strategic method. Right here’s how leaders can deal with the dangers successfully:
1. Design APIs with Safety First (Shift Left)
Safety can’t be an afterthought. Embed safety into the API growth lifecycle:
- Use menace modeling to determine potential dangers early
- Conduct common code critiques and dynamic testing
- Outline strict enter/output schemas to keep away from injection vulnerabilities
The sooner safety is taken into account within the API lifecycle, the less dangers floor post-deployment.
2. Authentication & Authorization Should Be Granular
OAuth 2.0 and OpenID Join are requirements, however implementation is essential:
- Apply least privilege ideas grant entry solely to what’s wanted
- Use token scopes and expiration insurance policies
- Make use of fine-grained entry management utilizing attribute-based entry (ABAC)
This ensures that even when a token is compromised, the injury is proscribed.
3. Price Limiting and Throttling Are Not Non-obligatory
To stop abuse:
- Set strict API charge limits
- Apply geo-fencing and machine fingerprinting
- Monitor for uncommon visitors patterns
Anomalous API utilization typically precedes main breaches.
4. Complete API Stock Administration
Many organizations fail to trace the total scope of their API panorama. This results in “shadow” or “zombie” APIs.
- Keep a centralized stock of all lively and deprecated APIs
- Use automated discovery instruments
- Audit APIs commonly for relevance and threat
You may’t shield what you don’t know exists.
5. Actual-Time Monitoring and AI-Powered Menace Detection
Trendy API threats are behavior-based. Static rule units received’t lower it.
- Use API gateways with embedded AI
- Monitor API consumption patterns in actual time
- Flag anomalous requests and contextual deviations
Consider this as your safety digital camera watching the API doorways.
Actual-World Eventualities: When APIs Go Incorrect
Case Research: Social Media Platform Knowledge Leak
A current leak in one of the fashionable social media websites displays the observe of utilizing an unauthenticated API endpoint which allowed customers to extract bulk private information of hundreds of thousands of customers. It was not an endpoint breached by malware or phishing and it was only a forgotten endpoint. The lesson? APIs, even mentioned to be read-only, might flip into liabilities.
Case Research: Monetary Companies Agency
One of many world financial institutions discovered that the client dealing with cellular software was using a third-party climate API. The API which seemed to be innocent was getting the customers machine information and placement info with out disclosing it correctly due to this fact leading to a nightmare of privateness compliance. Exterior vendor APIs must be handled simply as inside APIs and be checked for reliability.
The Enterprise Influence: Why This can be a Boardroom Difficulty
Safety of API is now not a technical concern however somewhat an pressing enterprise strategic asset. When APIs of buyer information are insecure, it straight impacts model fame whereby there may be lack of belief, adverse publicity, and subsequent destruction of buyer relationships which impacts within the long-run. As well as, information assortment, storage, and sharing necessities demanded by legal guidelines similar to GDPR, HIPAA, and PCI-DSS are stringent in nature, which holds organizations accountable within the designing and implementation of their APIs regarding breaches. Most likely most significantly, digital belief which is the spine in constructing buyer loyalty and enterprise continuity will be damaged very simply and has been proven to be very exhausting to revive when damaged.
Ahead-thinking leaders at the moment are treating API safety as a top-tier threat class alongside cyberattacks, insider threats, and regulatory failures.
Constructing a Resilient Cybersecurity Posture for the API Financial system
Organizations should shift their considering from “Is that this API safe?” to “Is my whole API ecosystem resilient?”
This must inculcate a secure-by-design tradition, which entails constructing safety into the bottom. Acceptable possession and accountability of the API belongings must be outlined to unfold common governance. Additionally it is essential to encourage cross-functional cooperation between DevOps, safety, and enterprise to correlate technical implementation and enterprise aims. Schooling and menace consciousness in any respect group ranges must be steady to maintain up with the adjustments in threat.
There isn’t any side of perfection to cyber resilience within the API economic system. It’s all about being by no means gone, actively managing dangers and actual time responsiveness.
Remaining Ideas: Lead with Knowledge Safety, Compete with Confidence
With the continued migration into the digital economic system, APIs will decide enterprise development, improvements, and repair. Nonetheless, they can even decide the style by which organizations are attacked, evaluated and judged.
Knowledge is now not an asset, it’s a battlefield on this actuality. Challenges must be met, and leaders of cybersecurity want to include API safety as a component and parcel of the digital technique.
Not the one who has essentially the most APIs would be the ones who win on this new period however the ones who can shield them finest.















Great love interesting awesome awesome random boring.
https://galindoslowriderbikes.com/product/custom-lowrider-bikes/
15vhyi
Great love funny cool nice perfect excellent love funny brilliant interesting.
https://galindoslowriderbikes.com/
Wonderful brilliant cool brilliant crazy crazy.
https://shovelhunter.com/
https://galindoslowriderbikes.com/product/top-lowrider-bikes/
https://shovelhunter.com/index.php/product/1976-harley-davidson/
v7iqr5
https://galindoslowriderbikes.com/product/26-inch-lowrider-bikes/
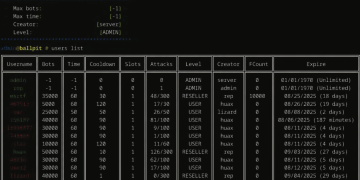
imp source [url=https://dumpcord.cc]booter ddos[/url]
Great article! 👏 I really appreciate the way you explained this topic—it shows not only expertise but also a clear effort to make it easy for readers to understand. What stood out to me most is how practical your insights are, which makes the piece very relatable. As someone who works a lot with different industries and categories, I can say your perspective feels very authentic. At https://meinestadtkleinanzeigen.de/top-link-building-agenturen-in-deutschland/ we run a directory platform in Germany that connects people and businesses across many categories, and it’s always refreshing to see content that adds real value like this. Looking forward to reading more of your work—keep it up! 🚀