The Australian Cyber Safety Centre (ACSC) has issued an alert relating to a essential vulnerability in Fortinet’s FortiOS and FortiProxy merchandise. This Fortinet vulnerability has been actively exploited within the wild, posing vital dangers to organizations that depend on these merchandise.
Technical customers in Australian companies, organizations, and authorities entities are suggested to take quick motion to safe their methods.
Fortinet Vulnerability: What Occurred?
Fortinet recognized a essential vulnerability in particular variations of FortiOS and FortiProxy. This vulnerability permits unauthenticated distant attackers to achieve “super-admin” privileges by exploiting an alternate path or channel vulnerability (CWE-288). Stories affirm energetic exploitation, with risk actors performing numerous post-exploitation actions.
Fortinet has supplied detailed indicators of compromise (IOCs) and IP addresses related to the risk actors. These may help organizations determine and examine suspicious actions.
Publish-Exploitation Actions Noticed:
Threat actors exploiting this vulnerability have been noticed performing the next actions:
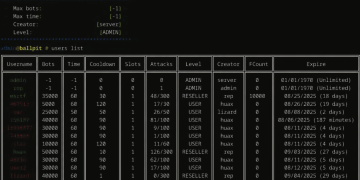
- Creating Admin Accounts: Attackers create admin accounts on units with random usernames.
- Including Native Customers: Risk actors create native consumer accounts with random names and combine them into current SSL VPN consumer teams.
- Adjusting Machine Configurations: Adjustments to settings reminiscent of firewall insurance policies have been famous.
- Establishing VPN Tunnels: Attackers log into SSL VPNs utilizing compromised accounts to create tunnels into inside networks.
Affected Variations
The next Fortinet merchandise and variations are impacted:
- FortiOS:
- Version 7.0 – From 7.0.0 to 7.0.16
- Solution: Upgrade to 7.0.17 or later.
- FortiProxy:
- Version 7.0 – From 7.0.0 to 7.0.19
- Solution: Upgrade to 7.0.20 or later.
- Version 7.2 – From 7.2.0 to 7.2.12
- Solution: Upgrade to 7.2.13 or later.
Non-Affected Versions:
FortiOS 7.4, FortiOS 7.6, FortiProxy 7.4, and FortiProxy 7.6 are not impacted by this vulnerability.
Mitigation Steps
The ACSC urges organizations to take the next steps to guard their methods:
- Improve to Safe Variations:
- Instantly improve affected methods to the newest variations as per Fortinet’s suggestions.
- Use Fortinet’s upgrade tool to find out the suitable improve path.
- Examine for Potential Compromise:
- Overview Fortinet’s revealed IOCs to determine any indicators of compromise in your atmosphere.
- Conduct detailed investigations for uncommon exercise in linked networks and units.
- Monitor Community Exercise:
- Proactively monitor for suspicious habits, reminiscent of surprising consumer accounts or modifications to firewall insurance policies.
- Observe Fortinet’s Revealed Recommendation:
- Confer with Fortinet’s vulnerability notification for added technical particulars and steering.
Technical Background
The Fortinet vulnerability exploits an authentication bypass utilizing an alternate path or channel vulnerability (CWE-288). This flaw permits attackers to craft particular requests focusing on the Node.js WebSocket module to achieve super-admin privileges.
The exploitation of this vulnerability can result in unauthorized entry, the flexibility to change gadget configurations, and the potential for additional lateral movement inside the community.
Why This Issues
The essential nature of this vulnerability can’t be overstated. Risk actors gaining super-admin privileges can have devastating penalties for organizations, together with data breaches, unauthorized system entry, and lack of operational integrity.
Fortinet merchandise are extensively used for securing enterprise and authorities networks. Guaranteeing these methods are up to date and uncompromised is important to sustaining a safe community infrastructure.
Subsequent Steps for Organisations
- Act Instantly: Improve susceptible units and examine for any indicators of compromise.
- Use the Fortinet Improve Device: Simplify the improve course of by leveraging Fortinet’s official instrument.
- Keep Up to date: Preserve observe of the newest advisories from each Fortinet and the ACSC.
- Improve Security Measures: Guarantee sturdy community monitoring, apply vital patches promptly, and encourage employees to make use of sturdy authentication practices.
When you suspect your methods have been compromised, report the problem instantly to the ACSC or your cybersecurity group.
Defending your methods from this Fortinet vulnerability is essential to safeguarding your group’s knowledge and operations. Take motion now to make sure your community stays safe.
Associated