A 26-year-old man in Ontario, Canada has been arrested for allegedly stealing information from and extorting greater than 160 corporations that used the cloud information service Snowflake.

Picture: https://www.pomerium.com/weblog/the-real-lessons-from-the-snowflake-breach
On October 30, Canadian authorities arrested Alexander Moucka, a.ok.a. Connor Riley Moucka of Kitchener, Ontario, on a provisional arrest warrant from the USA. Bloomberg first reported Moucka’s alleged ties to the Snowflake hacks on Monday.
On the finish of 2023, malicious hackers realized that many giant corporations had uploaded big volumes of delicate buyer information to Snowflake accounts that had been protected with little greater than a username and password (no multi-factor authentication required). After scouring darknet markets for stolen Snowflake account credentials, the hackers started raiding the info storage repositories utilized by among the world’s largest companies.
Amongst these was AT&T, which disclosed in July that cybercriminals had stolen private data and cellphone and textual content message data for roughly 110 million folks — almost all of its prospects. Wired.com reported in July that AT&T paid a hacker $370,000 to delete stolen cellphone data.
A report on the extortion assaults from the incident response agency Mandiant notes that Snowflake sufferer corporations had been privately approached by the hackers, who demanded a ransom in trade for a promise to not promote or leak the stolen information. All advised, greater than 160 Snowflake prospects had been relieved of information, together with TicketMaster, Lending Tree, Advance Auto Elements and Neiman Marcus.
Moucka is alleged to have used the hacker handles Judische and Waifu, amongst many others. These monikers correspond to a prolific cybercriminal whose exploits had been the topic of a recent story published here concerning the overlap between Western, English-speaking cybercriminals and extremist teams that harass and extort minors into harming themselves or others.
On Might 2, 2024, Judische claimed on the fraud-focused Telegram channel Star Chat that they’d hacked Santander Financial institution, one of many first identified Snowflake victims. Judische would repeat that declare in Star Chat on Might 13 — the day earlier than Santander publicly disclosed a knowledge breach — and would periodically blurt out the names of different Snowflake victims earlier than their information even went up on the market on the cybercrime boards.
404 Media reports that at a courtroom listening to in Ontario this morning, Moucka referred to as in from a jail cellphone and mentioned he was searching for authorized assist to rent an lawyer.
KrebsOnSecurity has realized that Moucka is presently named in a number of indictments issued by U.S. prosecutors and federal regulation enforcement businesses. Nonetheless, it’s unclear which particular expenses the indictments comprise, as all of these circumstances stay below seal.
TELECOM DOMINOES
Mandiant has attributed the Snowflake compromises to a bunch it calls “UNC5537,” with members primarily based in North America and Turkey. Sources near the investigation inform KrebsOnSecurity the UNC5537 member in Turkey is John Erin Binns, an elusive American man indicted by the U.S. Division of Justice (DOJ) for a 2021 breach at T-Mobile that uncovered the non-public data of not less than 76.6 million prospects.
In a press release on Moucka’s arrest, Mandiant mentioned UNC5537 aka Alexander ‘Connor’ Moucka has confirmed to be probably the most consequential risk actors of 2024.
“In April 2024, UNC5537 launched a marketing campaign, systematically compromising misconfigured SaaS cases throughout over 100 organizations,” wrote Austin Larsen, Mandiant’s senior risk analyst. “The operation, which left organizations reeling from important information loss and extortion makes an attempt, highlighted the alarming scale of hurt a person could cause utilizing off-the-shelf instruments.”
Sources concerned within the investigation mentioned UNC5537 has centered on hacking into telecommunications corporations around the globe. These sources advised KrebsOnSecurity that Binns and Judische are suspected of stealing data from India’s largest state-run telecommunications firm Bharat Sanchar Nigam Ltd (BNSL), and that the duo even bragged about having the ability to intercept or divert cellphone calls and textual content messages for a big portion of the inhabitants of India.
Judische seems to have outsourced the sale of databases from sufferer corporations who refuse to pay, delegating a few of that work to a cybercriminal who makes use of the nickname Kiberphant0m on a number of boards. In late Might 2024, Kiberphant0m started promoting the sale of tons of of gigabytes of information stolen from BSNL.
“Info is price a number of million {dollars} however I’m promoting for fairly low-cost,” Kiberphant0m wrote of the BSNL information in a submit on the English-language cybercrime neighborhood Breach Boards. “Negotiate a deal in Telegram.”

Additionally in Might 2024, Kiberphant0m took to the Russian-language hacking discussion board XSS to promote greater than 250 gigabytes of information stolen from an unnamed cellular telecom supplier in Asia, together with a database of all lively prospects and software program permitting the sending of textual content messages to all prospects.
On September 3, 2024, Kiberphant0m posted a gross sales thread on XSS titled “Promoting American Telecom Entry (100B+ Income).” Kiberphant0m’s asking value of $200,000 was apparently too excessive as a result of they reposted the gross sales thread on Breach Boards a month later, with a headline that extra clearly defined the info was stolen from Verizon‘s “push-to-talk” (PTT) prospects — primarily U.S. authorities businesses and first responders.
404Media reported recently that the breach doesn’t seem to affect the primary shopper Verizon community. Moderately, the hackers broke into a 3rd get together supplier and stole information on Verizon’s PTT methods, that are a separate product marketed in direction of public sector businesses, enterprises, and small companies to speak internally.
INTERVIEW WITH JUDISCHE
Investigators say Moucka shared a house in Kitchener with different tenants, however not his household. His mom was born in Chechnya, and he speaks Russian along with French and English. Moucka’s father died of a drug overdose at age 26, when the defendant was roughly 5 years previous.
An individual claiming to be Judische started speaking with this writer greater than three months in the past on Sign after KrebsOnSecurity began asking round about hacker nicknames beforehand utilized by Judische over time.
Judische admitted to stealing and ransoming information from Snowflake prospects, however he mentioned he’s not taken with promoting the knowledge, and that others have accomplished this with among the information units he stole.
“I’m probably not somebody that sells information except it’s crypto [databases] or bank cards as a result of they’re the one factor I can discover consumers for that really have cash for the info,” Judische advised KrebsOnSecurity. “The remaining is simply ransom.”
Judische has despatched this reporter dozens of unsolicited and sometimes profane messages from a number of totally different Sign accounts, all of which claimed to be an nameless tipster sharing totally different figuring out particulars for Judische. This seems to have been an elaborate effort by Judische to “detrace” his actions on-line and muddy the waters about his id.
Judische regularly claimed he had unparalleled “opsec” or operational safety, a time period that refers back to the capacity to compartmentalize and obfuscate one’s tracks on-line. In an effort to indicate he was one step forward of investigators, Judische shared data indicating somebody had given him a Mandiant researcher’s evaluation of who and the place they thought he was. Mandiant says these had been dialogue factors shared with choose reporters upfront of the researcher’s current discuss on the LabsCon security conference.
However in a dialog with KrebsOnSecurity on October 26, Judische acknowledged it was probably that the authorities had been closing in on him, and mentioned he would critically reply sure questions on his private life.
“They’re coming after me for positive,” he mentioned.
In a number of earlier conversations, Judische referenced affected by an unspecified character dysfunction, and when pressed mentioned he has a situation referred to as “schizotypal character dysfunction” (STPD).
In accordance with the Cleveland Clinic, schizotypal character dysfunction is marked by a constant sample of intense discomfort with relationships and social interactions: “Folks with STPD have uncommon ideas, speech and behaviors, which often hinder their capacity to type and preserve relationships.”
Judische mentioned he was prescribed medicine for his psychological points, however that he doesn’t take his meds. Which could clarify why he by no means leaves his house.
“I by no means go exterior,” Judische allowed. “I’ve by no means had a good friend or true relationship not on-line nor in particular person. I see folks as autos to realize my ends irrespective of how pleasant I could appear on the floor, which you’ll see by how briskly I discard people who find themselves loyal or [that] I’ve identified a very long time.”
Judische later admitted he doesn’t have an official STPD analysis from a doctor, however mentioned he is aware of that he reveals all of the indicators of somebody with this situation.
“I can’t really get recognized with that both,” Judische shared. “Most international locations put you on lists and limit you from sure issues if in case you have it.”
Requested whether or not he has all the time lived at his present residence, Judische replied that he needed to depart his hometown for his personal security.
“I can’t dwell safely the place I’m from with out getting robbed or arrested,” he mentioned, with out providing extra particulars.
A supply aware of the investigation mentioned Moucka beforehand lived in Quebec, which he allegedly fled after being charged with harassing others on the social community Discord.
Judische claims to have made not less than $4 million in his Snowflake extortions. Judische mentioned he and others regularly focused enterprise course of outsourcing (BPO) corporations, staffing companies that deal with customer support for a variety of organizations. In addition they went after managed service suppliers (MSPs) that oversee IT assist and safety for a number of corporations, he claimed.
“Snowflake isn’t even the largest BPO/MSP multi-company dataset on our networks, however what’s been exfiltrated from them is effectively over 100TB,” Judische bragged. “Solely ones that don’t pay get disclosed (except they disclose it themselves). Loads of them don’t even do their SEC submitting and simply pay us to fuck off.”
INTEL SECRETS
The opposite half of UNC5537 — 24-year-old John Erin Binns — was arrested in Turkey in late Might 2024, and presently resides in a Turkish jail. Nonetheless, it’s unclear if Binns faces any speedy risk of extradition to the USA, the place he’s presently wished on legal hacking expenses tied to the 2021 breach at T-Cell.
An individual aware of the investigation mentioned Binns’s software for Turkish citizenship was inexplicably permitted after his incarceration, resulting in hypothesis that Binns might have purchased his manner out of a sticky authorized scenario.
Beneath the Turkish structure, a Turkish citizen can’t be extradited to a international state. Turkey has been criticized for its “golden passport” program, which supplies citizenship and sanctuary for anybody keen to pay a number of hundred thousand {dollars}.

That is a picture of a passport that Binns shared in certainly one of many unsolicited emails to KrebsOnSecurity since 2021. Binns by no means defined why he despatched this in Feb. 2023.
Binns’s alleged hacker alter egos — “IRDev” and “IntelSecrets” — had been directly feared and revered on a number of cybercrime-focused Telegram communities, as a result of he was identified to own a robust weapon: A large botnet. From reviewing the Telegram channels Binns frequented, we are able to see that others in these communities — together with Judische — closely relied on Binns and his botnet for quite a lot of cybercriminal functions.
The IntelSecrets nickname corresponds to a person who has claimed accountability for modifying the supply code for the Mirai “Internet of Things” botnet to create a variant generally known as “Satori,” and supplying it to others who used it for legal acquire and were later caught and prosecuted.
Since 2020, Binns has filed a flood of lawsuits naming varied federal regulation enforcement officers and businesses — together with the FBI, the CIA, and the U.S. Special Operations Command (PDF), demanding that the federal government flip over data collected about him and searching for restitution for his alleged kidnapping by the hands of the CIA.
Binns claims he was kidnapped in Turkey and subjected to numerous types of psychological and bodily torture. In accordance with Binns, the U.S. Central Intelligence Company (CIA) falsely advised their counterparts in Turkey that he was a supporter or member of the Islamic State (ISIS), a declare he says led to his detention and torture by the Turkish authorities.
Nonetheless, in a 2020 lawsuit he filed towards the CIA, Binns himself acknowledged having visited a beforehand ISIS-controlled space of Syria previous to shifting to Turkey in 2017.
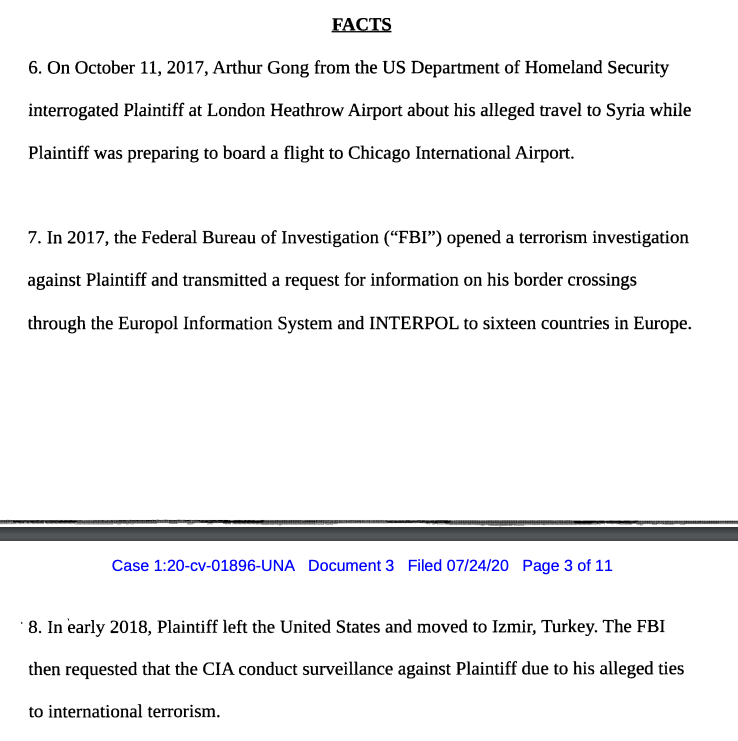
A section of a lawsuit Binns filed in 2020 towards the CIA, wherein he alleges U.S. put him on a terror watch listing after he traveled to Syria in 2017.
Sources aware of the investigation advised KrebsOnSecurity that Binns was so paranoid about attainable surveillance on him by American and Turkish intelligence businesses that his erratic habits and on-line communications really introduced concerning the very authorities snooping that he feared.
In a number of on-line chats in late 2023 on Discord, IRDev lamented being lured right into a regulation enforcement sting operation after making an attempt to purchase a rocket launcher on-line. An individual near the investigation confirmed that at the start of 2023, IRDev started making earnest inquiries about the right way to buy a Stinger, an American-made moveable weapon that operates as an infrared surface-to-air missile.
Sources advised KrebsOnSecurity Binns’ repeated efforts to buy the projectile earned him a number of visits from the Turkish authorities, who had been justifiably curious why he stored searching for to amass such a robust weapon.
WAIFU
A cautious examine of Judische’s postings on Telegram and Discord since 2019 exhibits this person is extra extensively identified below the nickname “Waifu,” a moniker that corresponds to one of many extra completed “SIM swappers” within the English-language cybercrime neighborhood over time.
SIM swapping entails phishing, tricking or bribing cell phone firm staff for credentials wanted to redirect a goal’s cell phone quantity to a tool the attackers management — permitting thieves to intercept incoming textual content messages and cellphone calls.
A number of SIM-swapping channels on Telegram preserve a regularly up to date leaderboard of the 100 richest SIM-swappers, in addition to the hacker handles related to particular cybercrime teams (Waifu is ranked #24). That listing has lengthy included Waifu on a roster of hackers for a bunch that referred to as itself “Beige.”
The time period “Beige Group” got here up in reporting on two tales revealed right here in 2020. The primary was in an August 2020 piece called Voice Phishers Targeting Corporate VPNs, which warned that the COVID-19 epidemic had introduced a wave of focused voice phishing assaults that attempted to trick work-at-home staff into offering entry to their employers’ networks. Frequent targets of the Beige group included staff at quite a few high U.S. banks, ISPs, and cell phone suppliers.
The second time Beige Group was talked about by sources was in reporting on a breach at the domain registrar GoDaddy. In November 2020, intruders regarded as related to the Beige Group tricked a GoDaddy worker into putting in malicious software program, and with that entry they had been in a position to redirect the online and electronic mail site visitors for a number of cryptocurrency buying and selling platforms. Different frequent targets of the Beige group included staff at quite a few high U.S. banks, ISPs, and cell phone suppliers.
Judische’s varied Telegram identities have lengthy claimed involvement within the 2020 GoDaddy breach, and he didn’t deny his alleged position when requested immediately. Judische mentioned he prefers voice phishing or “vishing” assaults that consequence within the goal putting in data-stealing malware, versus tricking the person into coming into their username, password and one-time code.
“Most of my ops contain malware [because] credential entry burns too quick,” Judische defined.
CRACKDOWN ON HARM GROUPS?
The Telegram channels that the Judische/Waifu accounts frequented over time present this person divided their time between posting in channels devoted to monetary cybercrime, and harassing and stalking others in hurt communities like Leak Society and Courtroom.
Each of those Telegram communities are identified for victimizing kids by means of coordinated on-line campaigns of extortion, doxing, swatting and harassment. Folks affiliated with hurt teams like Courtroom and Leak Society will usually recruit new members by lurking on gaming platforms, social media websites and cellular functions which are in style with younger folks, together with Discord, Minecraft, Roblox, Steam, Telegram, and Twitch.
“This kind of offence often begins with a direct message by means of gaming platforms and might transfer to extra personal chatrooms on different digital platforms, sometimes one with video enabled options, the place the dialog shortly turns into sexualized or violent,” warns a recent alert from the Royal Canadian Mounted Police (RCMP) concerning the rise of sextortion teams on social media channels.
“One of many ways being utilized by these actors is sextortion, nonetheless, they aren’t utilizing it to extract cash or for sexual gratification,” the RCMP continued. “As a substitute they use it to additional manipulate and management victims to provide extra dangerous and violent content material as a part of their ideological targets and radicalization pathway.”
A few of the largest such identified teams embody people who go by the names 764, CVLT, Kaskar, 7997, 8884, 2992, 6996, 555, Slit City, 545, 404, NMK, 303, and H3ll.
On the varied cybercrime-oriented channels Judische frequented, he usually lied about his or others’ involvement in varied breaches. However Judische additionally at instances shared nuggets of fact about his previous, notably when discussing the early historical past and membership of particular Telegram- and Discord-based cybercrime and hurt teams.
Judische claimed in a number of chats, together with on Leak Society and Courtroom, that they had been an early member of the Atomwaffen Division (AWD), a white supremacy group whose members are suspected of getting dedicated a number of murders within the U.S. since 2017.
In 2019, KrebsOnSecurity uncovered how a loose-knit group of neo-Nazis, a few of whom had been affiliated with AWD, had doxed and/or swatted nearly three dozen journalists at a range of media publications. Swatting entails speaking a false police report of a bomb risk or hostage scenario and tricking authorities into sending a closely armed police response to a focused deal with.
Judsiche additionally advised a fellow denizen of Courtroom that years in the past he was lively in an older hurt neighborhood referred to as “RapeLash,” a very vile Discord server identified for attracting Atomwaffen members. A 2018 retrospective on RapeLash posted to the now defunct neo-Nazi discussion board Fascist Forge explains that RapeLash was awash in gory, violent pictures and baby pornography.
A Fascist Forge member named “Huddy” recalled that RapeLash was the third incarnation of an extremist neighborhood also referred to as “FashWave,” brief for Fascist Wave.
“I’ve no actual information of what occurred with the middleman section generally known as ‘FashWave 2.0,’ however FashWave 3.0 homes a number of identified Satanists and different degenerates linked with AWD, certainly one of which bought arrested on possession of kid pornography expenses, final I heard,” Huddy shared.
In June 2024, a Mandiant worker told Bloomberg that UNC5537 members have made loss of life threats towards cybersecurity specialists investigating the hackers, and that in a single case the group used synthetic intelligence to create pretend nude photographs of a researcher to harass them.
Allison Nixon is chief analysis officer with the New York-based cybersecurity agency Unit 221B. Nixon is amongst a number of researchers who’ve confronted harassment and particular threats of bodily violence from Judische.
Nixon mentioned Judische is more likely to argue in courtroom that his self-described psychological dysfunction(s) ought to one way or the other excuse his lengthy profession in cybercrime and in harming others.
“They ran a misinformation marketing campaign in a sloppy try and cowl up the hacking marketing campaign,” Nixon mentioned of Judische. “Coverups are an acknowledgment of guilt, which can undermine a psychological sickness protection in courtroom. We anticipate that violent hackers from the [cybercrime community] will expertise more and more harsh sentences because the crackdown continues.”
5:34 p.m. ET: Up to date story to incorporate a clarification from Mandiant.