The Nim programming language has develop into more and more enticing to malware builders because of its sturdy compiler and its capacity to work simply with different languages. Nim’s compiler can compile Nim to JavaScript, C, C++, and Goal-C, and cross-compile for main working programs comparable to Home windows, Linux, macOS, Android, and iOS. Moreover, Nim helps importing features and symbols from the languages talked about above, and importing from dynamically linked libraries for Home windows and shared libraries for Linux. Nim wrapper modules are additionally accessible, comparable to Winim, that make interplay with the working system painless. All these capabilities permit simple integration of Nim into growth pipelines utilizing these languages and increase the event of latest instruments, each benign and malicious.
It’s no shock, then, that ESET Analysis has seen an ongoing use of malware developed in Nim within the wild. Way back to 2019, Sednit was spotted utilizing a malicious downloader written in Nim. One other infamous group enjoying the Nim recreation, and the impetus for growing Nimfilt, is the Mustang Panda APT group. ESET Analysis recorded Mustang Panda using Nim in its toolset for the primary time in a marketing campaign in opposition to a governmental group in Slovakia in August 2023. The malicious DLL detected – and used as a part of the group’s traditional trident Korplug loader – was written in Nim.
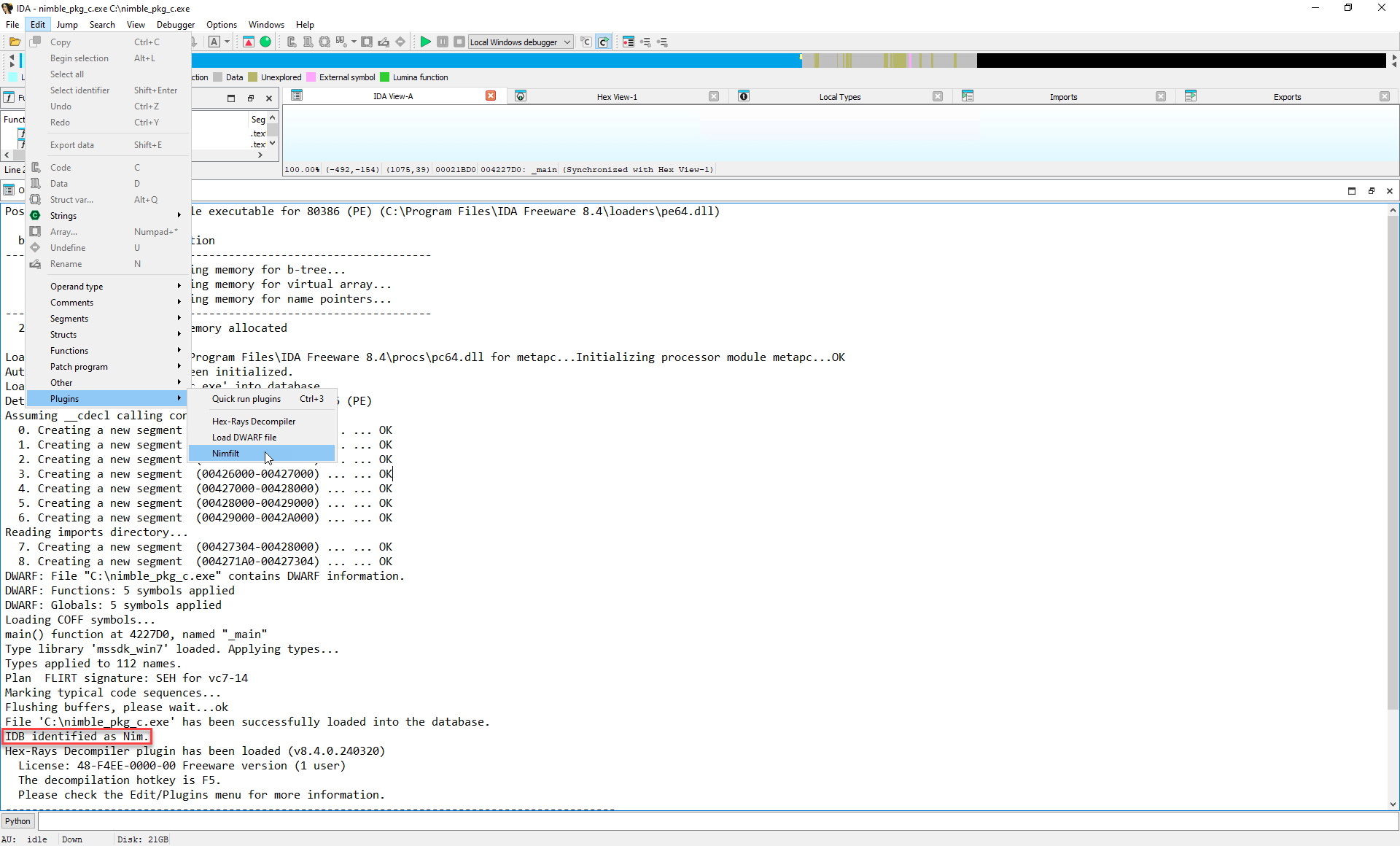
For researchers tasked with reverse engineering such binaries, Nimfilt is a robust device to hurry up evaluation. Whereas Nimfilt could be run as a Python script each on the command line (with a subset of its performance) and in Hex-Rays’ IDA program, will probably be introduced right here primarily as a Python plugin for IDA.
Initializing Nimfilt in IDA
When IDA is first opened, it hundreds and initializes any plugins within the IDA plugins listing. In the course of the initialization of Nimfilt, the plugin makes use of primary heuristics to find out whether or not the disassembled binary was compiled with the Nim compiler. If one of many following checks is handed, Nimfilt determines that this compiler was used:
- The binary comprises each of the next strings:
- The binary comprises any of the next well-known Nim perform names:
- NimMain
- NimMainInner
- NimMainModule
- The binary comprises at the very least two of the next error message strings:
- @worth out of vary
- @division by zero
- @over- or underflow
- @index out of bounds
YARA guidelines are offered together with Nimfilt that make comparable checks to find out whether or not an ELF or PE file has been compiled with Nim. Collectively, these checks are much more sturdy than the method taken by different instruments, comparable to Detect It Easy, which at the moment solely checks the .rdata part of PE recordsdata for the string io.nim or deadly.nim.
As the ultimate initialization step, if Nimfilt’s AUTO_RUN flag is about to true, the plugin runs instantly. In any other case, Nimfilt could be run as regular from IDA’s plugins menu, as proven in Determine 1.
Demangling with Nimfilt
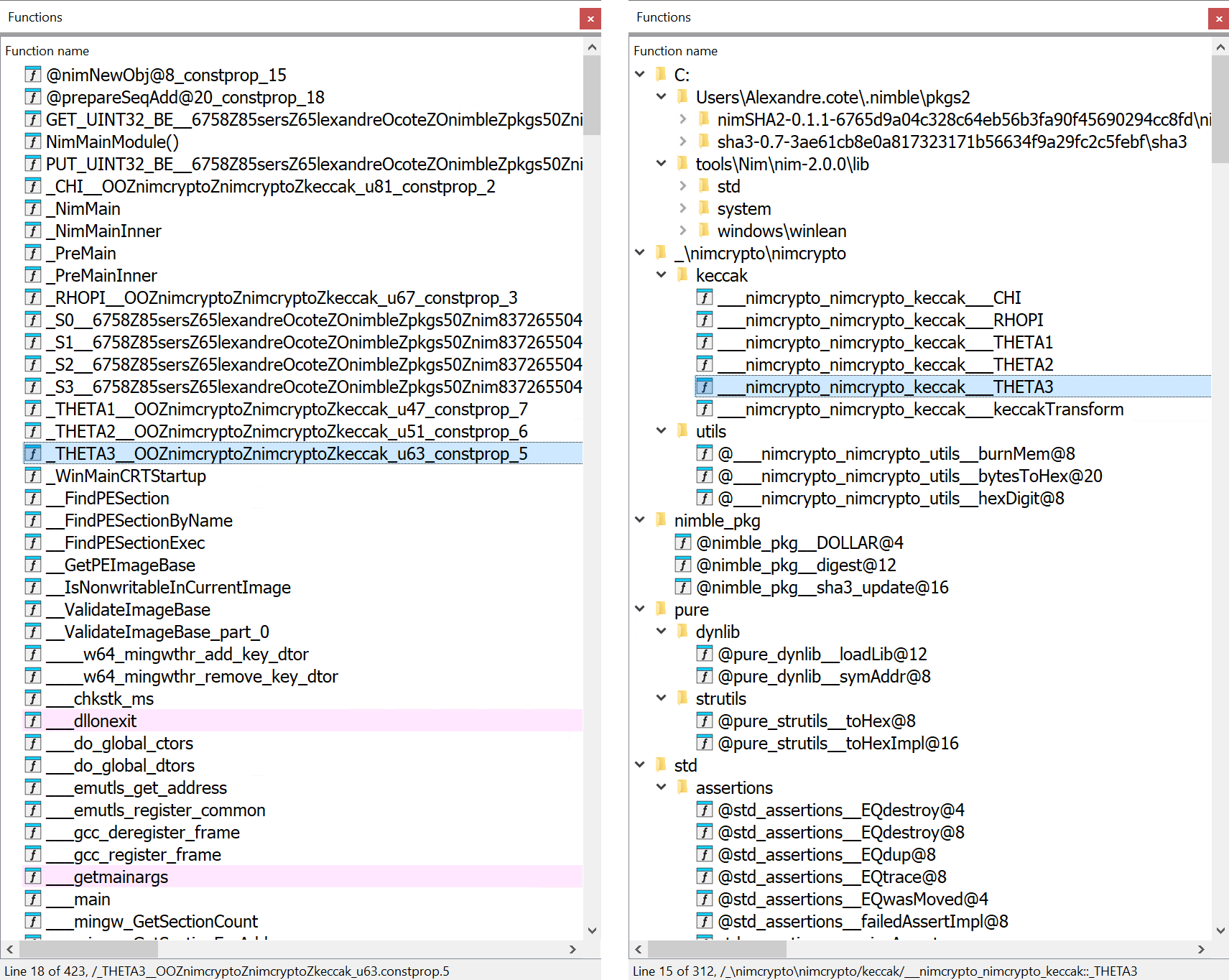
Nim makes use of a customized identify mangling scheme that Nimfilt can decode. Throughout a run, Nimfilt iterates by means of every perform identify within the binary, checking whether or not the identify is a Nim bundle or perform identify. Found names are renamed to their demangled types.
Apparently, these names can leak details about the developer’s setting, in a lot the identical method as PDB paths. That is because of the Nim compiler including the file path to the identify throughout mangling – Nimfilt reveals the trail upon demangling.
For instance, perform names from third-party packages are saved as absolute paths throughout the mangling course of. Determine 2 exhibits a perform identify that’s saved as an absolute path revealing the model and checksum of the nimSHA2 bundle used, together with the developer’s set up path for nimble – Nim’s default bundle supervisor.
python nimfilt.py GET_UINT32_BE__6758Z85sersZ85serOnameZOnimbleZpkgs50Znim837265504548O49O494554555453d57a4852c515056c5452eb5354b51fa5748f5253545748505752cc56fdZnim83726550_u68
C:/Customers/Consumer.identify/.nimble/pkgs2/nimSHA2-0.1.1-6765d9a04c328c64eb56b3fa90f45690294cc8fd/nimSHA2::GET_UINT32_BE u68
Determine 2. Demangling the identify of a perform from a third-party bundle
In distinction, Determine 3 exhibits the identify of a perform from a regular Nim bundle saved as a relative path (that’s, relative to the Nim set up path).
python nimfilt.py toHex__pureZstrutils_u2067
pure/strutils::toHex u2067
Determine 3. Demangling the identify of a perform from a regular Nim bundle
Nevertheless, names should not all the time mangled in the identical method. Determine 4 exhibits that the identical perform identify above from the nimSHA2 bundle is saved on Linux as a relative path.
python nimfilt.py GET_UINT32_BE__OOZOOZOOZhomeZalexZOnimbleZpkgs50Znim837265504548O49O494554555453d57a4852c515056c5452eb5354b51fa5748f5253545748505752cc56fdZnim83726550_u49
Determine 4. Demangling the identify of a perform from a third-party bundle on Linux
Package deal initialization features are mangled in a totally completely different method: the bundle identify is saved as a file path (together with the file extension) positioned earlier than the perform identify and an escaping scheme is used to characterize sure characters like ahead slashes, hyphens, and dots. Upon demangling, Nimfilt cleans up the bundle identify by eradicating the .nim file extension, as proven in Determine 5.
python nimfilt.py atmdotdotatsdotdotatsdotnimbleatspkgsatswinimminus3dot9dot1atswinimatsincatswinbasedotnim_DatInit000
Determine 5. Demangling the identify of an initialization perform from a third-party bundle
Determine 6 exhibits how names of initialization features from native packages are saved as absolute paths.
python nimfilt.py atmCatcatstoolsatsNimatsnimminus2dot0dot0atslibatssystemdotnim_Init000
C:/instruments/Nim/nim-2.0.0/lib/system::Init000
Determine 6. Demangling the identify of an initialization perform from a local bundle
In IDA, Nimfilt’s identify demangling course of is adopted by the creation of directories within the Capabilities window to prepare features in response to their bundle identify or path, as proven in Determine 7.
Making use of structs to Nim strings
The final motion carried out throughout a run of Nimfilt is making use of C-style structs to Nim strings. Simply as strings in another programming languages are objects moderately than null-terminated sequences of bytes, so are strings in Nim. Determine 8 exhibits how the string ABCDEF seems in IDA earlier than and after operating Nimfilt. Notice that in disassembled type, a Nim-compiled binary makes use of the prefix _TM as part of the non permanent identify of some variables; these are sometimes Nim strings.
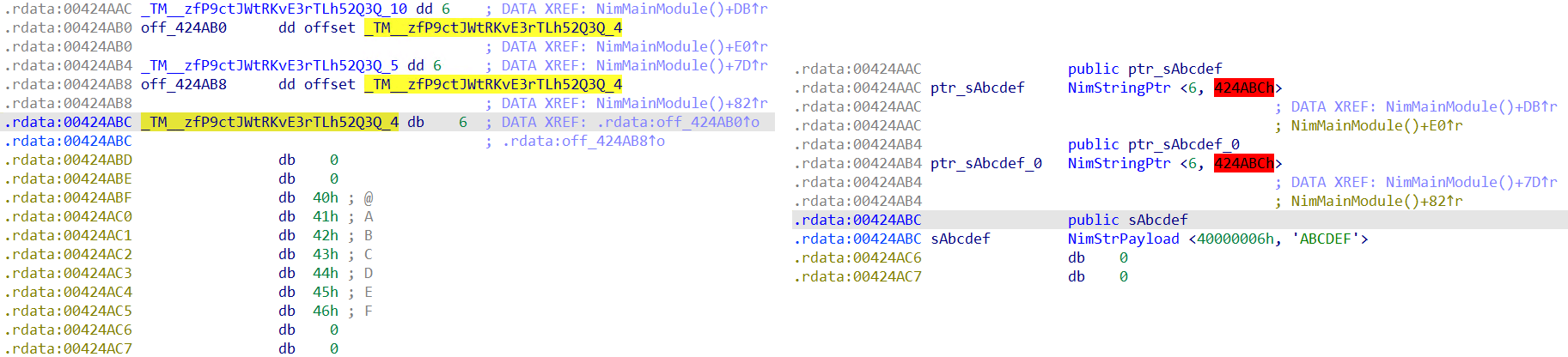
Nimfilt iterates by means of every tackle within the .rdata or .rodata section, and in some other read-only knowledge section, searching for Nim strings. Structs are utilized to any found strings; the struct comprises a size subject and a pointer to the payload consisting of the characters within the string.
Wrap-up
On its option to being compiled as an executable, Nim supply code is usually translated to C or C++; nonetheless, this course of doesn’t totally take away all traces of Nim. By taking a journey by means of the Nim compiler supply code, now we have unraveled among the paths taken within the compilation course of and have been thus capable of construct Nimfilt as a Python device, and IDA plugin, to help on this untangling.
Briefly, whether or not or not you’re new to Nim, turning to Nimfilt will make your reverse engineering work with Nim-compiled binaries nearly immediately simpler and extra targeted. In no way, nonetheless, is Nimfilt’s growth at a standstill; we’re engaged on extra options to deal with double mangling, and enhance the formatting of demangled names and the grouping of bundle names.
Nimfilt’s supply code and documentation can be found in a repository hosted on ESET’s GitHub group at https://github.com/eset/nimfilt.