
Picture: Shutterstock, iHaMoo.
Adam Griffin continues to be in disbelief over how rapidly he was robbed of practically $500,000 in cryptocurrencies. A scammer referred to as utilizing an actual Google cellphone quantity to warn his Gmail account was being hacked, despatched e-mail safety alerts straight from google.com, and finally seized management over the account by convincing him to click on “sure” to a Google immediate on his cellular gadget.
Griffin is a battalion chief firefighter within the Seattle space, and on Could 6 he obtained a name from somebody claiming they had been from Google help saying his account was being accessed from Germany. A Google search on the cellphone quantity calling him — (650) 203-0000 — revealed it was an official quantity for Google Assistant, an AI-based service that may interact in two-way conversations.
On the similar time, he obtained an e-mail that got here from a google.com e-mail tackle, warning his Google account was compromised. The message included a “Google Help Case ID quantity” and details about the Google consultant supposedly speaking to him on the cellphone, stating the rep’s title as “Ashton” — the identical title given by the caller.
Griffin didn’t be taught this till a lot later, however the e-mail he obtained had an actual google.com tackle as a result of it was despatched through Google Forms, a service out there to all Google Docs customers that makes it straightforward to ship surveys, quizzes and different communications.
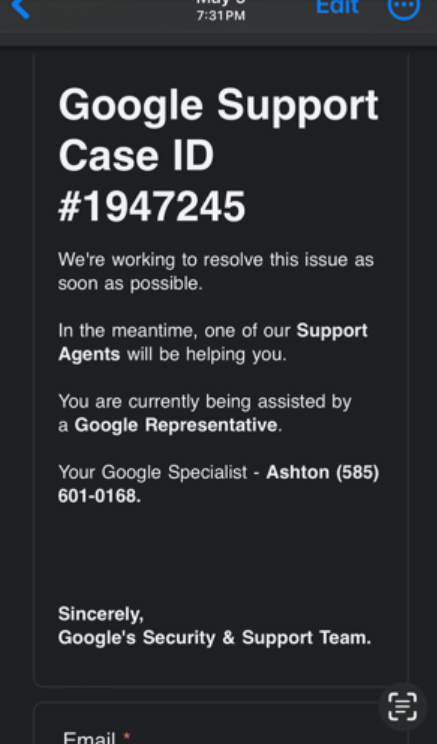
A phony safety alert Griffin obtained previous to his bitcoin heist, through Google Kinds.
In line with tripwire.com’s Graham Cluely, phishers will use Google Kinds to create a safety alert message, after which change the shape’s settings to routinely ship a duplicate of the finished type to any e-mail tackle entered into the shape. The attacker then sends an invite to finish the shape to themselves, to not their meant sufferer.
“So, the attacker receives the invitation to fill out the shape – and once they full it, they enter their meant sufferer’s e-mail tackle into the shape, not their very own,” Cluely wrote in a December 2023 post. “The attackers are making the most of the truth that the emails are being despatched out straight by Google Kinds (from the google.com area). It’s a longtime authentic area that helps to make the e-mail look extra authentic and is much less prone to be intercepted en route by email-filtering options.”
The faux Google consultant was well mannered, affected person, skilled and reassuring. Ashton advised Griffin he was going to obtain a notification that might enable him to regain management of the account from the hackers. Certain sufficient, a Google immediate immediately appeared on his cellphone asking, “Is it you making an attempt to get well your account?”
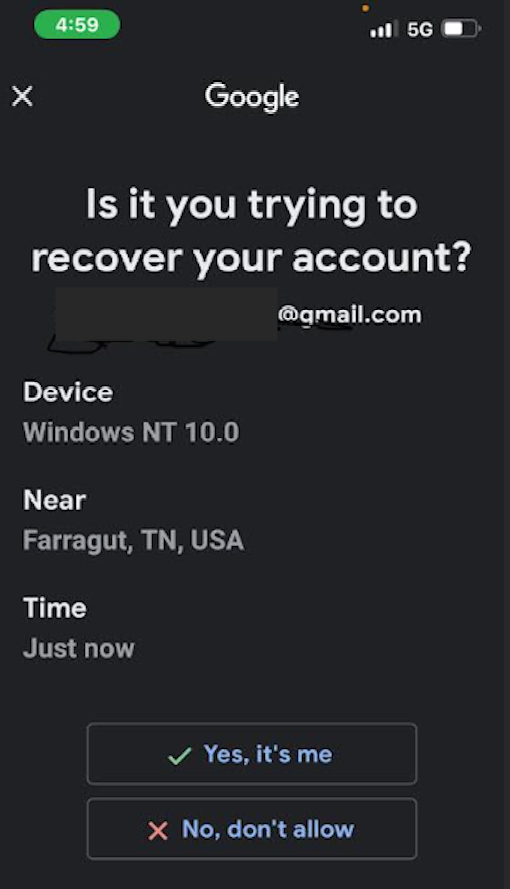
Adam Griffin clicked “sure,” to an account restoration notification just like this one on Could 6.
Griffin stated that after receiving the pop-up immediate from Google on his cellphone, he felt extra comfortable that he actually was speaking to somebody at Google. In actuality, the thieves brought on the alert to seem on his cellphone merely by stepping by Google’s account restoration course of for Griffin’s Gmail tackle.
“As quickly as I clicked sure, I gave them entry to my Gmail, which was synched to Google Images,” Griffin stated.
Sadly for Griffin, years in the past he used Google Images to retailer a picture of the key seed phrase that was defending his cryptocurrency pockets. Armed with that phrase, the phishers may drain all of his funds.
“From there they had been in a position to switch roughly $450,000 out of my Exodus pockets,” Griffin recalled.
Griffin stated simply minutes after freely giving entry to his Gmail account he obtained a name from somebody claiming to be with Coinbase, who likewise advised him somebody in Germany was making an attempt to take over his account.
Griffin stated a follow-up investigation revealed the attackers had used his Gmail account to achieve entry to his Coinbase account from a VPN connection in California, offering the multi-factor code from his Google Authenticator app. Unbeknownst to him on the time, Google Authenticator by default additionally makes the identical codes out there in a single’s Google account on-line.
However when the thieves tried to maneuver $100,000 value of cryptocurrency out of his account, Coinbase despatched an e-mail stating that the account had been locked, and that he must submit extra verification paperwork earlier than he may do something with it.
GRAND THEFT AUTOMATED
Simply days after Griffin was robbed, a scammer impersonating Google managed to phish 45 bitcoins — roughly $4,725,000 at immediately’s worth — from Tony, a 42-year-old skilled from northern California. Tony agreed to talk about his harrowing expertise given that his final title not be used.
Tony acquired into bitcoin again in 2013 and has been investing in it ever since. On the night of Could 15, 2024, Tony was placing his three- and one-year-old boys to mattress when he obtained a message from Google about an account safety concern, adopted by a cellphone name from a “Daniel Alexander” at Google who stated his account was compromised by hackers.
Tony stated he had simply signed up for Google’s Gemini AI (a man-made intelligence platform previously often known as “Bard”), and mistakenly believed the decision was a part of that service. Daniel advised Tony his account was being accessed by somebody in Frankfurt, Germany, and that he may evict the hacker and get well entry to the account by clicking “sure” to the immediate that Google was going to ship to his cellphone.
The Google immediate arrived seconds later. And to his eternal remorse, Tony clicked the “Sure, it’s me” button.
Then got here one other name, this one allegedly from safety personnel at Trezor, an organization that makes encrypted {hardware} gadgets made to retailer cryptocurrency seed phrases securely offline. The caller stated somebody had submitted a request to Trezor to shut his account, they usually forwarded Tony a message despatched from his Gmail account that included his title, Social Safety quantity, date of start, tackle, cellphone quantity and e-mail tackle.
Tony stated he started to consider then that his Trezor account really was compromised. The caller satisfied him to “get well” his account by getting into his cryptocurrency seed phrase at a phishing web site (verify-trezor[.]io) that mimicked the official Trezor web site.
“At this level I am going into combat or flight mode,” Tony recalled. “I’ve acquired my children crying, my spouse is like what the heck is occurring? My mind went haywire. I put my seed phrase right into a phishing web site, and that was it.”
Nearly instantly, all the funds he was planning to avoid wasting for retirement and for his youngsters’s faculty fund had been drained from his account.
“I made errors as a result of being so busy and never pondering appropriately,” Tony advised KrebsOnSecurity. “I had gotten so far-off from the safety protocols in bitcoin as life had modified a lot since having children.”
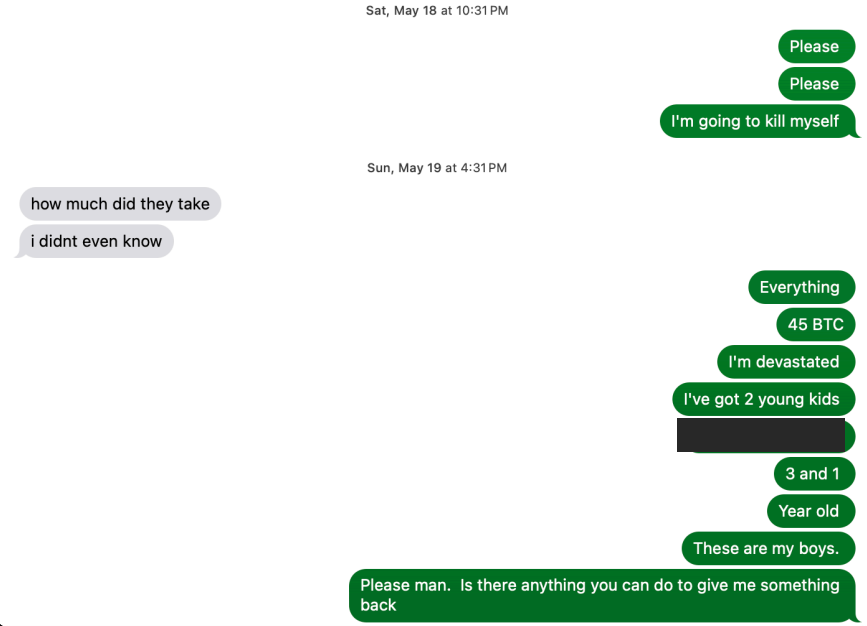
Tony shared this textual content message trade of him pleading along with his tormentors after being robbed of 45 bitcoins.
Tony stated the theft left him traumatized and offended for months.
“All I used to be occupied with was defending my boys and it ended up costing me every part,” he stated. “For sure I’m devastated and have needed to do critical remedy to get by it.”
MISERY LOVES COMPANY
Tony advised KrebsOnSecurity that within the weeks following the theft of his 45 bitcoins, he grew to become so consumed with rage and disgrace that he was significantly considering suicide. Then sooner or later, whereas scouring the Web for indicators that others could have been phished by Daniel, he encountered Griffin posting on Reddit in regards to the cellphone quantity concerned in his latest bitcoin theft.
Griffin stated the 2 of them had been initially suspicious of one another — exchanging cautious messages for a few week — however he determined Tony was telling the reality after contacting the FBI agent that Tony stated was working his case. Evaluating notes, they found the faux Google safety alerts they obtained simply previous to their particular person bitcoin thefts referenced the identical phony “Google Help Case ID” quantity.
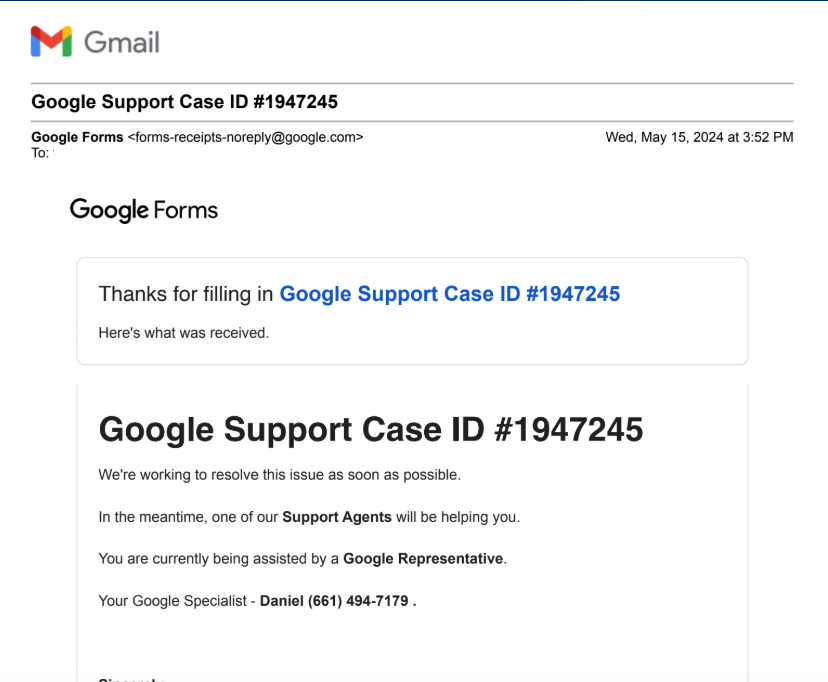
Adam Griffin and Tony stated they obtained the identical Google Help Case ID quantity upfront of their thefts. Each had been despatched through Google Kinds, which sends straight from the google.com area title.
Extra importantly, Tony acknowledged the voice of “Daniel from Google” when it was featured in an interview by Junseth, a podcaster who covers cryptocurrency scams. The identical voice that had coaxed Tony out of his appreciable cryptocurrency holdings simply days earlier additionally had tried to phish Junseth, who performed alongside for a number of minutes earlier than revealing he knew it was a rip-off.
Daniel advised Junseth he was a youngster and labored with different rip-off callers who had all met years in the past on the sport Minecraft, and that he just lately loved a run of back-to-back Gmail account compromises that led to crypto theft paydays.
“Nobody will get arrested,” Daniel enthused to Junseth within the Could 7 podcast, which rapidly went viral on social media. “It’s nearly like there’s no penalties. I’ve small authorized facet hustles, like companies and shit that I can funnel every part by. When you had been to see me in actual life, I appear to be a daily baby going to high school with my backpack and shit, you’d by no means count on this child is stealing all this shit.”
Daniel defined that they usually use an automatic bot that initiates calls to targets warning that their account is experiencing suspicious exercise, and that they need to press “1” to talk with a consultant. This course of, he defined, basically self-selects people who find themselves extra prone to be vulnerable to their social engineering schemes. [It is possible — but not certain — that this bot Daniel referenced explains the incoming call to Griffin from Google Assistant that precipitated his bitcoin heist].
Daniel advised Junseth he and his co-conspirators had simply scored a $1.2 million theft that was nonetheless pending on the bitcoin funding platform SwanBitcoin. In response, Junseth tagged SwanBitcoin in a post about his podcast on Twitter/X, and the CEO of Swan rapidly replied that they caught the $1.2 million transaction that morning.
Apparently, Daniel didn’t recognize having his voice broadcast to the world (or his $1.2 million bitcoin heist disrupted) as a result of based on Junseth somebody submitted a baseless copyright infringement claim about it to Soundcloud, which was internet hosting the recording.

The criticism alleged the recording included a copyrighted tune, however that wasn’t true: Junseth later posted a uncooked model of the recording to Telegram, and it clearly had no music within the background. Nonetheless, Soundcloud eliminated the audio file.
“All these firms are very afraid of copyright,” Junseth defined in a Could 2024 interview with the podcast whatbitcoindid.com, which options a number of the highlights from his recorded name with Daniel.
“It’s fascinating as a result of copyright infringement actually is an act that you simply’re claiming in opposition to the writer, however for some purpose these firms have taken a really exhausting line in opposition to it, so for those who even declare there’s copyrighted materials in it they simply take it down after which they go away it to you to show that you simply’re harmless,” Junseth stated. “In Soundcloud’s occasion, a part of declaring your innocence is it’s important to give them your property tackle and every part else, and it says proper on there, ‘this will probably be offered to the particular person making the copyright declare.’”
AFTERMATH
When Junseth requested how potential victims may shield themselves, Daniel defined that if the goal doesn’t have their Google Authenticator synced to their Google cloud account, the scammers can’t simply pivot into the sufferer’s accounts at cryptocurrency exchanges, as they did with Griffin.
By default, Google Authenticator syncs all one-time codes with a Gmail consumer’s account, which means if somebody good points entry to your Google account, they will then entry all the one-time codes handed out by your Google Authenticator app.
To alter this setting, open Authenticator in your cellular gadget, choose your profile image, after which select “Use with out an Account” from the menu. When you disable this, it’s a good suggestion to maintain a printed copy of one-time backup codes, and to retailer these in a safe place.
You may additionally want to obtain Google Authenticator to a different cellular gadget that you simply management. In any other case, for those who flip off cloud synching and lose that sole cellular gadget along with your Google Authenticator app, it might be tough or unimaginable to get well entry to your account for those who in some way get locked out.
Griffin advised KrebsOnSecurity he had no thought it was really easy for thieves to take over his account, and to abuse so many alternative Google providers within the course of.
“I do know I undoubtedly made errors, however I additionally know Google may do rather a lot higher job defending folks,” he stated.
In response to questions from KrebsOnSecurity, Google stated it could verify that this was a slim phishing marketing campaign, reaching a “very small group of individuals.”
“We’re conscious of this slim and focused assault, and have hardened our defenses to dam restoration makes an attempt from this actor,” the corporate stated in a written assertion, which emphasised that the actual Google won’t ever name you.
“Whereas a lot of these social engineering campaigns are consistently evolving, we’re constantly working to harden our methods with new instruments and technical improvements, in addition to sharing updated guidance with our customers to remain forward of attackers,” the assertion reads.
Each Griffin and Tony say they proceed to obtain “account safety” calls from folks pretending to work for Google or one of many cryptocurrency platforms.
“It’s such as you get placed on some type of checklist, after which these lists get recycled time and again,” Tony stated.
Griffin stated that for a number of months after his ordeal, he accepted nearly each cryptocurrency rip-off name that got here his approach, enjoying alongside within the useless hope of in some way tricking the caller into revealing particulars about who they’re in actual life. However he stopped after his taunting brought on one of many scammers to start out threatening him personally.
“I in all probability shouldn’t have, however I recorded two 30-minute conversations with these guys,” Griffin stated, acknowledging that possibly it wasn’t such an amazing thought to antagonize cybercriminals who clearly already knew every part about him. “One man I talked to about his private life, after which his buddy referred to as me up and stated he was going to dox me and do all this different dangerous stuff. My FBI contact later advised me to not discuss to those guys anymore.”
Sound recommendation. So is hanging up each time anybody calls you a few safety downside with considered one of your accounts. Even security-conscious folks are inclined to underestimate the complicated and shifting menace from phone-based phishing scams, however they achieve this at their peril.
When unsure: Hang up, look up, and call back. In case your response to a lot of these calls entails something apart from hanging up, researching the proper cellphone quantity, and contacting the entity that claims to be calling, you could be setting your self up for a expensive and humbling studying expertise.
Perceive that your e-mail credentials are more than likely the key to unlocking your entire digital identity. Make sure to use an extended, distinctive passphrase on your e-mail tackle, and by no means decide a passphrase that you’ve ever used anyplace else (not even a variation on an outdated password).
Lastly, it’s additionally a good suggestion to reap the benefits of the strongest multi-factor authentication strategies provided. For Gmail/Google accounts, that features the use of passkeys or physical security keys, that are closely phishing resistant. For Google customers holding measurable sums of cryptocurrency, probably the most safe possibility is Google’s free Advanced Protection program, which incorporates extra in depth account security measures but additionally comes with some serious convenience trade-offs.















