The fee card large MasterCard simply fastened a obvious error in its area identify server settings that would have allowed anybody to intercept or divert Web visitors for the corporate by registering an unused area identify. The misconfiguration endured for almost 5 years till a safety researcher spent $300 to register the area and stop it from being grabbed by cybercriminals.
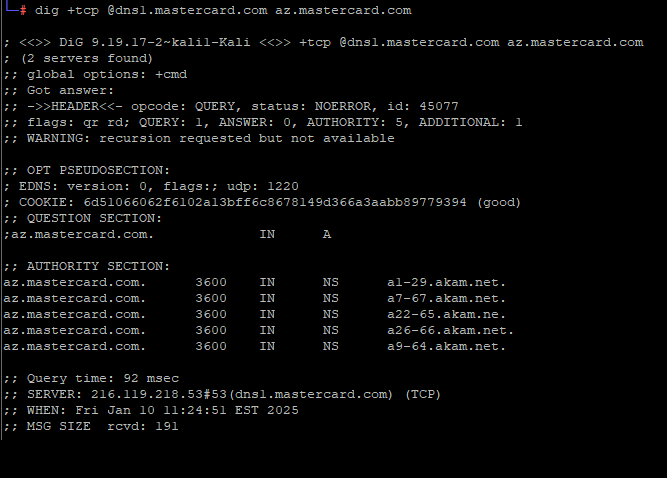
A DNS lookup on the area az.mastercard.com on Jan. 14, 2025 exhibits the mistyped area identify a22-65.akam.ne.
From June 30, 2020 till January 14, 2025, one of many core Web servers that MasterCard makes use of to direct visitors for parts of the mastercard.com community was misnamed. MasterCard.com depends on 5 shared Area Identify System (DNS) servers on the Web infrastructure supplier Akamai [DNS acts as a kind of Internet phone book, by translating website names to numeric Internet addresses that are easier for computers to manage].
All the Akamai DNS server names that MasterCard makes use of are supposed to finish in “akam.web” however considered one of them was misconfigured to depend on the area “akam.ne.”
This tiny however probably vital typo was found just lately by Philippe Caturegli, founding father of the safety consultancy Seralys. Caturegli stated he guessed that no person had but registered the area akam.ne, which is underneath the purview of the top-level area authority for the West Africa nation of Niger.
Caturegli stated it took $300 and almost three months of ready to safe the area with the registry in Niger. After enabling a DNS server on akam.ne, he seen tons of of hundreds of DNS requests hitting his server every day from places across the globe. Apparently, MasterCard wasn’t the one group that had fat-fingered a DNS entry to incorporate “akam.ne,” however they had been by far the biggest.
Had he enabled an e-mail server on his new area akam.ne, Caturegli probably would have obtained wayward emails directed towards mastercard.com or different affected domains. If he’d abused his entry, he in all probability may have obtained website encryption certificates (SSL/TLS certs) that had been approved to just accept and relay internet visitors for affected web sites. He might even have been capable of passively receive Microsoft Windows authentication credentials from worker computer systems at affected firms.
However the researcher stated he didn’t try to do any of that. As an alternative, he alerted MasterCard that the area was theirs in the event that they needed it, copying this creator on his notifications. A number of hours later, MasterCard acknowledged the error, however stated there was by no means any actual risk to the safety of its operations.
“We have now seemed into the matter and there was not a threat to our techniques,” a MasterCard spokesperson wrote. “This typo has now been corrected.”
In the meantime, Caturegli obtained a request submitted via Bugcrowd, a program that provides monetary rewards and recognition to safety researchers who discover flaws and work privately with the affected vendor to repair them. The message urged his public disclosure of the MasterCard DNS error by way of a post on LinkedIn (after he’d secured the akam.ne area) was not aligned with moral safety practices, and handed on a request from MasterCard to have the submit eliminated.
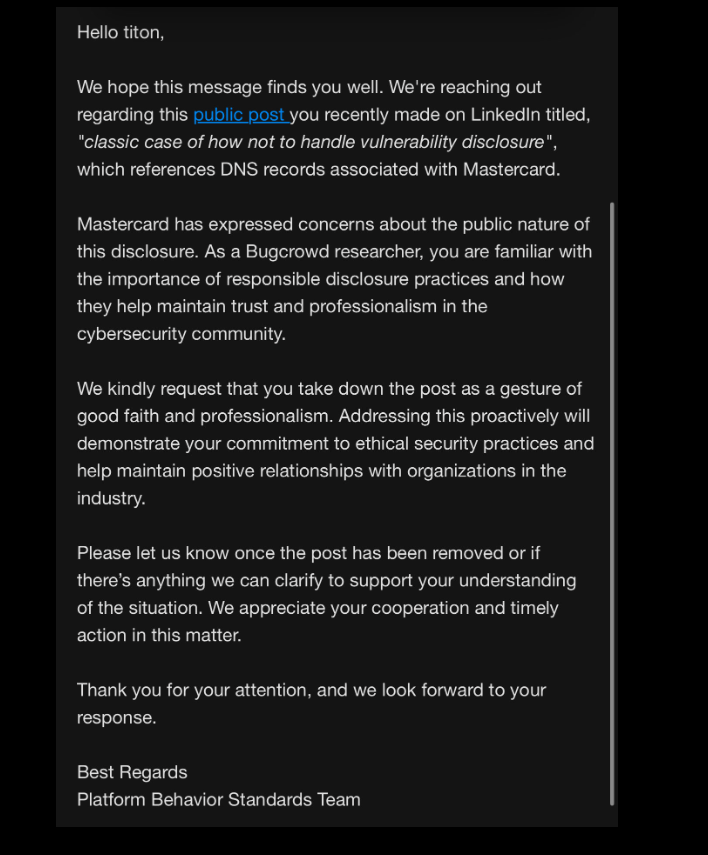
MasterCard’s request to Caturegli, a.ok.a. “Titon” on infosec.alternate.
Caturegli stated whereas he does have an account on Bugcrowd, he has by no means submitted something via the Bugcrowd program, and that he reported this subject on to MasterCard.
“I didn’t disclose this subject via Bugcrowd,” Caturegli wrote in reply. “Earlier than making any public disclosure, I ensured that the affected area was registered to stop exploitation, mitigating any threat to MasterCard or its clients. This motion, which we took at our personal expense, demonstrates our dedication to moral safety practices and accountable disclosure.”
Most organizations have no less than two authoritative area identify servers, however some deal with so many DNS requests that they should unfold the load over extra DNS server domains. In MasterCard’s case, that quantity is 5, so it stands to motive that if an attacker managed to grab management over simply a kind of domains they might solely have the ability to see about one-fifth of the general DNS requests coming in.
However Caturegli stated the fact is that many Web customers are relying no less than to some extent on public visitors forwarders or DNS resolvers like Cloudflare and Google.
“So all we’d like is for considered one of these resolvers to question our identify server and cache the outcome,” Caturegli stated. By setting their DNS server data with an extended TTL or “Time To Reside” — a setting that may alter the lifespan of information packets on a community — an attacker’s poisoned directions for the goal area will be propagated by giant cloud suppliers.
“With an extended TTL, we might reroute a LOT extra than simply 1/5 of the visitors,” he stated.
The researcher stated he’d hoped that the bank card large would possibly thank him, or no less than provide to cowl the price of shopping for the area.
“We clearly disagree with this evaluation,” Caturegli wrote in a follow-up post on LinkedIn concerning MasterCard’s public assertion. “However we’ll allow you to choose— listed below are among the DNS lookups we recorded earlier than reporting the problem.”
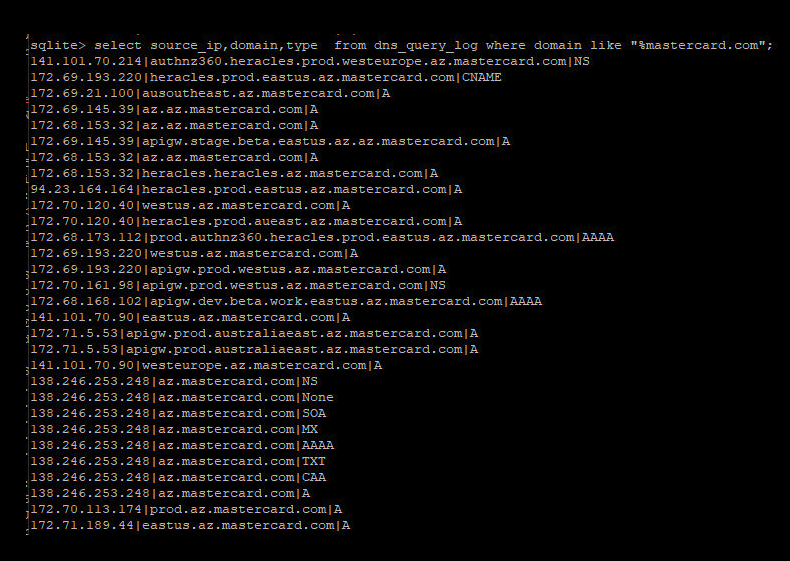
Caturegli posted this screenshot of MasterCard domains that had been probably in danger from the misconfigured area.
Because the screenshot above exhibits, the misconfigured DNS server Caturegli discovered concerned the MasterCard subdomain az.mastercard.com. It isn’t clear precisely how this subdomain is utilized by MasterCard, nonetheless their naming conventions counsel the domains correspond to manufacturing servers at Microsoft’s Azure cloud service. Caturegli stated the domains all resolve to Web addresses at Microsoft.
“Don’t be like Mastercard,” Caturegli concluded in his LinkedIn submit. “Don’t dismiss threat, and don’t let your advertising and marketing group deal with safety disclosures.”
One ultimate observe: The area akam.ne has been registered beforehand — in December 2016 by somebody utilizing the e-mail handle [email protected]. The Russian search large Yandex reviews this consumer account belongs to an “Ivan I.” from Moscow. Passive DNS data from DomainTools.com present that between 2016 and 2018 the area was linked to an Web server in Germany, and that the area was left to run out in 2018.
That is attention-grabbing given a comment on Caturegli’s LinkedIn post from an ex-Cloudflare employee who linked to a report he co-authored on an identical typo area apparently registered in 2017 for organizations that will have mistyped their AWS DNS server as “awsdns-06.ne” as an alternative of “awsdns-06.web.” DomainTools reviews that this typo area additionally was registered to a Yandex consumer ([email protected]), and was hosted on the identical German ISP — Group Web (AS61969).













