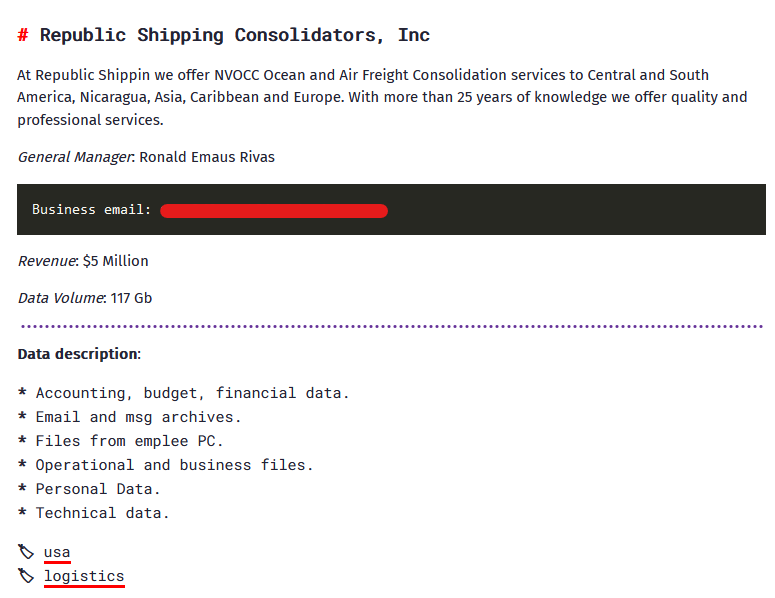
Republic Transport Consolidators, a distinguished logistics firm, finds itself entangled within the internet of a cyberattack orchestrated by the infamous BianLian ransomware group. The group has claimed the Republic Transport Consolidators cyberattack on its darkish internet channel and overtly added it to its information leak web site, exposing a staggering 117 GB of delicate data.
The compromised information spans a large spectrum, together with accounting information, finances particulars, monetary information, electronic mail and message archives, recordsdata extracted from worker PCs, operational and business-related paperwork, private data, and technical information.
The severity of this Republic Transport Consolidators data breach raises issues not just for the corporate but additionally for the people and entities related to the compromised information.
Republic Transport Consolidators Cyberattack Decoded
The group’s message on the info leak web site outlines the extent of their infiltration, emphasizing the monetary particulars with a reported income of US$5 million.
The Cyber Express sought a response from Republic Shipping Consolidators concerning this alleged cyberattack, however as of now, no official assertion has been issued, leaving the Republic Transport Consolidators information breach claims unverified.
Apparently, regardless of the reported cyberattack, the web site for Republic Transport Consolidators stays operational with out instant indicators of compromise. This means that the hackers might need focused the backend of the web site, doubtlessly gaining unauthorized entry to databases, reasonably than attacking the entrance finish.
BianLian ransomware group, recognized for its malicious actions since June 2022, operates as a developer, deployer, and information extortion cybercriminal group. Their targets lengthen past U.S. crucial infrastructure sectors to incorporate Australian crucial infrastructure, skilled providers, and property growth.
The BianLian Ransomware Group Modus Operandi
The modus operandi of the BianLian group entails having access to sufferer methods via legitimate Distant Desktop Protocol (RDP) credentials. They make use of open-source tools and command-line scripting for discovery and credential harvesting, adopted by the exfiltration of sufferer information via numerous means, akin to File Switch Protocol (FTP), Rclone, or Mega.
Notably, the group shifted from a double-extortion mannequin to primarily exfiltration-based extortion round January 2023. Within the occasion of a sufferer refusing to pay the ransom, the BianLian ransomware group resorts to threatening the discharge of exfiltrated information on a Tor network-based leak web site.
The Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Safety Company (CISA), and Australian Cyber Safety Centre (ACSC) collectively encourage crucial infrastructure organizations and small- to medium-sized enterprises to implement recommended mitigations to cut back the chance and affect of BianLian and different ransomware incidents.
BianLian group’s techniques embrace issuing a novel Tox ID for every sufferer group and pressuring victims via numerous means, akin to printing ransom notes to compromised community printers and making threatening phone calls to staff related to sufferer corporations.
Media Disclaimer: This report relies on inside and exterior analysis obtained via numerous means. The knowledge offered is for reference functions solely, and customers bear full duty for his or her reliance on it. The Cyber Express assumes no legal responsibility for the accuracy or penalties of utilizing this data.
Associated
















