Google’s Risk Analyst Group has confirmed that Iran-backed hackers have used their cyber capabilities to undercut public help for the Israel-Hamas battle within the US and Israel.
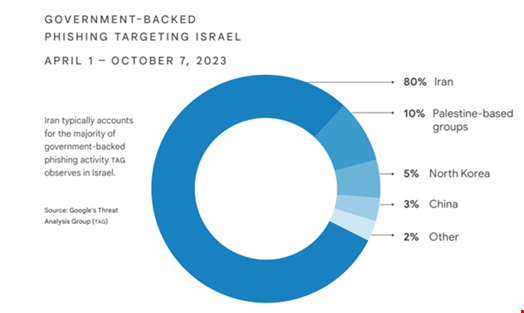
In Software of First Resort: Israel-Hamas Warfare in Cyber, a joint menace intelligence report revealed on February 14, Google’s Risk Analyst Group (TAG) and Mandiant discovered that Iranian adversaries accounted for 80% of all government-backed phishing exercise that focused customers based mostly in Israel within the six months main as much as Hamas’s assault.
The Iran-backed teams noticed to be energetic through the analyzed interval are acquainted to the Google researchers, Mandiant Intelligence’s VP, Sandra Joyce, stated throughout a press convention.
A few of these embody APT32 (aka Charming Kitten, Mint Sandstrom), Dusty Cave (aka Imperial Kitten, Crimson Sandstorm) and Dune (aka Banished Kitten, STORM-0842).
In 2023, these menace teams aggressively focused US and Israeli entities, typically with blended outcomes.
Google researchers discovered that Iranian adversaries constantly tried to emphasise and infrequently exaggerate the influence of these assaults.
“On multiple event, for targets that weren’t exceptionally impactful, menace actors tried to provide you with one thing that appeared as one thing greater than it truly was,” Joyce defined.
Centered Efforts to Undercut Public Help for the Israel-Hamas Warfare
After the October 7 assault Hamas performed in opposition to Israel, Iran-backed menace teams’ techniques shifted to focus much more on Israel, and the tempo of assaults elevated considerably.
“From October 2023, we now have seen a centered effort to undercut public help for the struggle,” the report reads.
A few of these teams’ cyber exercise following the Hamas assault included:
- Damaging assaults in opposition to key Israeli organizations
- Hack-and-leak operations, together with exaggerated claims of assaults in opposition to important infrastructure in Israel and the US
- Data operations (IO) to demoralize Israeli residents, erode belief in important organizations and switch international public opinion in opposition to Israel
- Phishing campaigns directed towards customers based mostly in Israel and the US to gather intelligence on important decision-makers

Other than this Iranian exercise uptick, the times following the October 7 assault was not related to a basic spike in adversary cyber exercise, Google researchers discovered.
“We noticed nothing like what we noticed throughout and after the 2022 Russian invasion of Ukraine,” Joyce stated.
Cyber Espionage Campaigns Ongoing
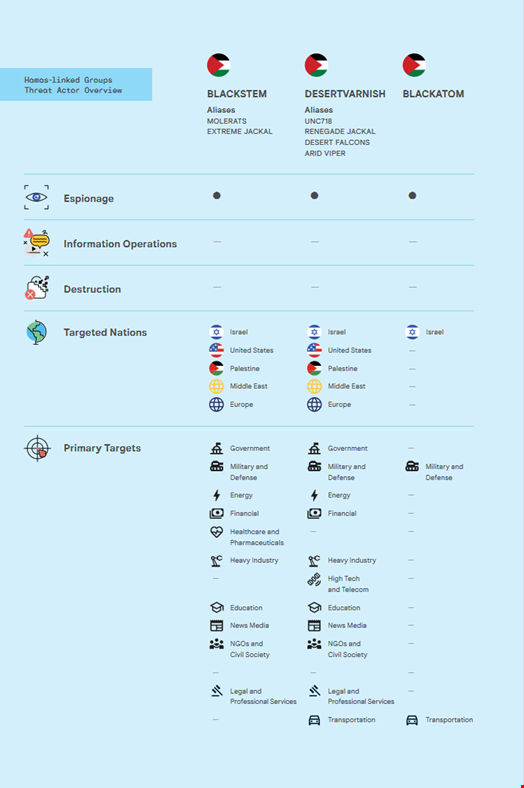
For years, pro-Hamas hackers have been noticed conducting a mixture of intra-Palestine focusing on, in addition to common focusing on of Israel, the US, Europe and nations neighboring Israel and Palestine.
Google TAG and Mandiant discovered that a few of these Hamas-linked teams, reminiscent of Blackstem (aka Molerats, Excessive Jackal) and Desert Varnish (aka Desert Falcons, Arid Viper, Renegade Jackal) have additionally been conducting cyber espionage campaigns all through 2023 to gather intelligence from targets inside the Palestinian Territories and Israel previous to the October 7 assault.
They’ve been utilizing “simple-but-effective” methods, techniques and procedures (TTPs), added the researchers.
These TTPs embody mass phishing campaigns focusing on customers in Palestine and its regional neighbors in addition to persistent efforts to focus on Israeli entities utilizing quite a lot of customized and open-source cyber capabilities, together with Android malware and spy ware.
One marketing campaign, performed by Blackatom in September 2023, confirmed indicators of extra superior capabilities, together with elaborate social engineering tailor-made to software program engineers and customized malware developed for Home windows, Mac, and Linux.
Nonetheless, the researchers assessed that Hamas didn’t use cyber operations to tactically help the October 7 assault.
Unattributed Predatory Sparrow Focused Iran
Lastly, Google’s researchers discovered that in at the very least one occasion in 2023, Iranian important infrastructure was disrupted by an actor claiming to be responding to the battle.
The menace group, calling themselves “Gonjeshke Darande” (Predatory Sparrow) claimed it had taken a majority of gasoline stations in Iran offline, attacking their infrastructure and fee programs.
Though Iran has attributed this exercise to Israel, Google researchers stated they don’t have adequate proof to guage these claims or give any attribution at this level.
John Hultquist, Mandiant Intelligence’s chief analyst, commented: “There have been discussions concerning the degree of sources essential to conduct this and former assaults attributed to Predatory Sparrow, which might result in pondering it’s a talented adversary, however I might watch out not to attract any conclusions.”
Google’s Cyber Risk Predictions for 2024
Primarily based on their observations, Google’s researchers supplied some forward-looking assessments concerning these menace actors for 2024. These embody:
- Iran-linked teams are more likely to proceed to conduct damaging cyber-attacks, significantly within the occasion of any perceived escalation to the battle, to incorporate kinetic exercise in opposition to Iranian proxy teams in numerous nations, reminiscent of Lebanon and Yemen.
- Hack-and-leak operations and data operations will stay key parts in these efforts to telegraph intent and functionality all through the struggle, each to Iran’s adversaries and to different audiences that they search to affect.
- Whereas the outlook for future cyber operations by Hamas-linked actors is unsure within the close to time period, we anticipate Hamas cyber exercise will finally resume, with a concentrate on espionage for intelligence gathering on intra-Palestine affairs, Israel, the US, Europe, and different regional gamers within the Center East.















