The homepage of Stark Industries Options.
Two weeks earlier than Russia invaded Ukraine in February 2022, a big, mysterious new Web internet hosting agency referred to as Stark Industries Options materialized and rapidly turned the epicenter of large distributed denial-of-service (DDoS) assaults on authorities and industrial targets in Ukraine and Europe. An investigation into Stark Industries reveals it’s getting used as a world proxy community that conceals the true supply of cyberattacks and disinformation campaigns towards enemies of Russia.
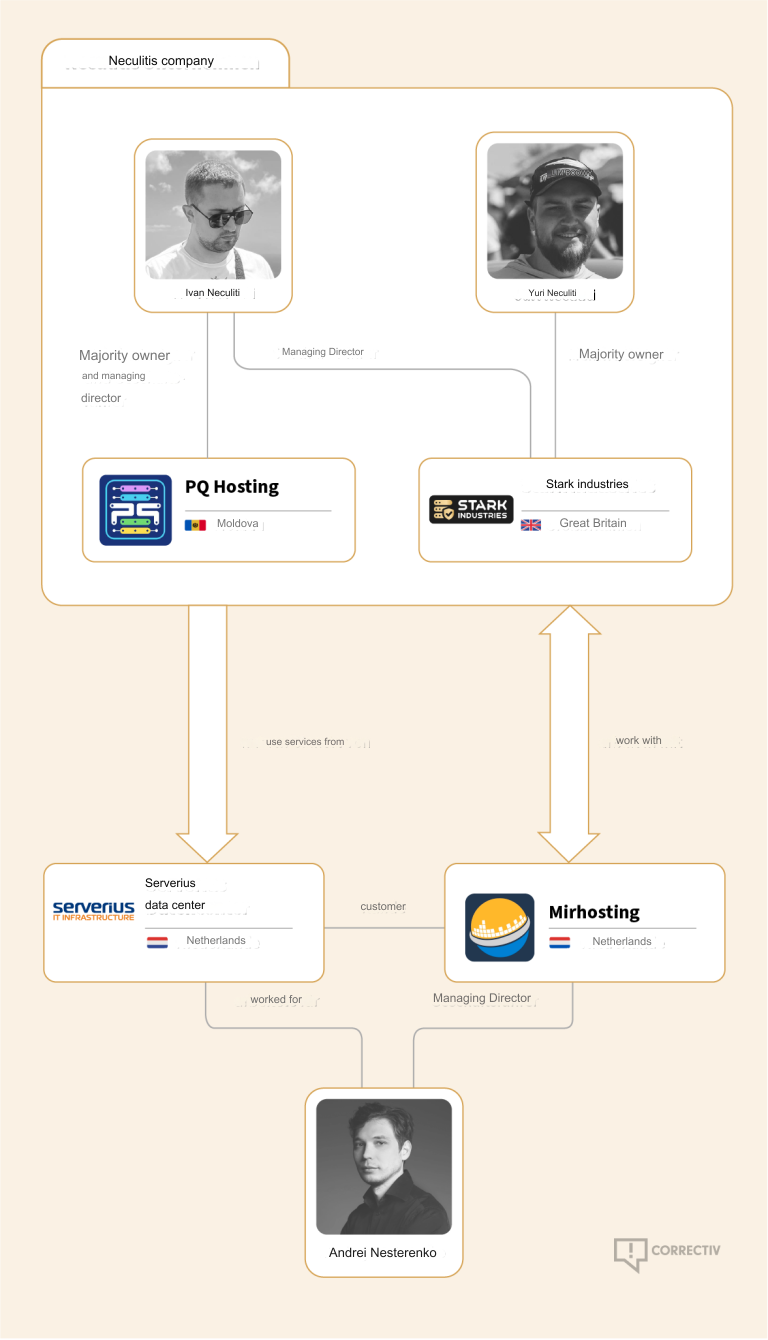
No less than a dozen patriotic Russian hacking teams have been launching DDoS assaults for the reason that begin of the battle at quite a lot of targets seen versus Moscow. However by all accounts, few assaults from these gangs have come near the quantity of firepower wielded by a pro-Russia group calling itself “NoName057(16).”
This graphic comes from a current report from Arbor NETSCOUT about DDoS assaults from Russian hacktivist teams.
As detailed by researchers at Radware, NoName has successfully gamified DDoS assaults, recruiting hacktivists by way of its Telegram channel and providing to pay individuals who agree to put in a bit of software program referred to as DDoSia. That program permits NoName to commandeer the host computer systems and their Web connections in coordinated DDoS campaigns, and DDoSia customers with essentially the most assaults can win money prizes.
The NoName DDoS group promoting on Telegram. Picture: SentinelOne.com.
A report from the safety agency Group Cymru discovered the DDoS assault infrastructure utilized in NoName campaigns is assigned to 2 interlinked internet hosting suppliers: MIRhosting and Stark Industries. MIRhosting is a internet hosting supplier based in The Netherlands in 2004. However Stark Industries Solutions Ltd was integrated on February 10, 2022, simply two weeks earlier than the Russian invasion of Ukraine.
PROXY WARS
Safety specialists say that not lengthy after the battle began, Stark started internet hosting dozens of proxy companies and free digital non-public networking (VPN) companies, that are designed to assist customers protect their Web utilization and placement from prying eyes.
Proxy suppliers enable customers to route their Web and Internet looking visitors by way of another person’s laptop. From a web site’s perspective, the visitors from a proxy community person seems to originate from the rented IP handle, not from the proxy service buyer.
These companies can be utilized in a respectable method for a number of enterprise functions — comparable to worth comparisons or gross sales intelligence — however they’re additionally massively abused for hiding cybercrime exercise as a result of they’ll make it tough to hint malicious visitors to its authentic supply.
What’s extra, many proxy companies don’t disclose how they receive entry to the proxies they’re renting out, and in lots of instances the entry is obtained by way of the dissemination of malicious software program that turns the contaminated system in a visitors relay — normally unbeknownst to the respectable proprietor of the Web connection. Different proxy companies will enable customers to make cash by renting out their Web connection to anybody.
Spur.us is an organization that tracks VPNs and proxy companies worldwide. Spur finds that Stark Industries (AS44477) presently is residence to a minimum of 74 VPN companies, and 40 completely different proxy companies. As we’ll see within the closing part of this story, simply a type of proxy networks has over one million Web addresses obtainable for lease throughout the globe.
Raymond Dijkxhoorn operates a internet hosting agency in The Netherlands referred to as Prolocation. He additionally co-runs SURBL, an anti-abuse service that flags domains and Web handle ranges which can be strongly related to spam and cybercrime exercise, together with DDoS.
Dijkxhoorn mentioned final 12 months SURBL heard from a number of individuals who mentioned they operated VPN companies whose internet sources had been included in SURBL’s block lists.
“We had individuals doing delistings at SURBL for domains that had been suspended by the registrars,” Dijkhoorn informed KrebsOnSecurity. “And a minimum of two of them defined that Stark supplied them free VPN companies that they had been reselling.”
Dijkxhoorn added that Stark Industries additionally sponsored activist teams from Ukraine.
“How beneficial would it not be for Russia to know the actual IPs from Ukraine’s tech warriors?” he noticed.
CLOUDY WITH A CHANCE OF BULLETS
Richard Hummel is risk intelligence lead at Arbor NETSCOUT. Hummel mentioned when he considers the worst of all of the internet hosting suppliers on the market immediately, Stark Industries is persistently close to or on the high of that record.
“The reason being we’ve had a minimum of a dozen service suppliers come to us saying, ‘There’s this community on the market inundating us with visitors,’” Hummel mentioned. “And it wasn’t even DDoS assaults. [The systems] on Stark had been simply scanning these suppliers so quick it was crashing a few of their companies.”
Hummel mentioned NoName will sometimes launch their assaults utilizing a mixture of sources from rented from main, respectable cloud companies, and people from so-called “bulletproof” internet hosting suppliers like Stark. Bulletproof suppliers are so named after they earn or domesticate a popularity for ignoring any abuse complaints or police reviews about exercise on their networks.
Combining bulletproof suppliers with respectable cloud internet hosting, Hummel mentioned, doubtless makes NoName’s DDoS campaigns extra resilient as a result of many community operators will hesitate to be too aggressive in blocking Web addresses related to the foremost cloud companies.
“What we sometimes see here’s a distribution of cloud internet hosting suppliers and bulletproof internet hosting suppliers in DDoS assaults,” he mentioned. “They’re utilizing public cloud internet hosting suppliers as a result of loads of instances that’s your first layer of community protection, and since [many companies are wary of] over-blocking entry to respectable cloud sources.”
However even when the cloud supplier detects abuse coming from the client, the supplier might be not going to close the client down instantly, Hummel mentioned.
“There’s normally a grace interval, and even when that’s solely an hour or two, you possibly can nonetheless launch numerous assaults in that point,” he mentioned. “After which they only hold coming again and opening new cloud accounts.”
MERCENARIES TEAM
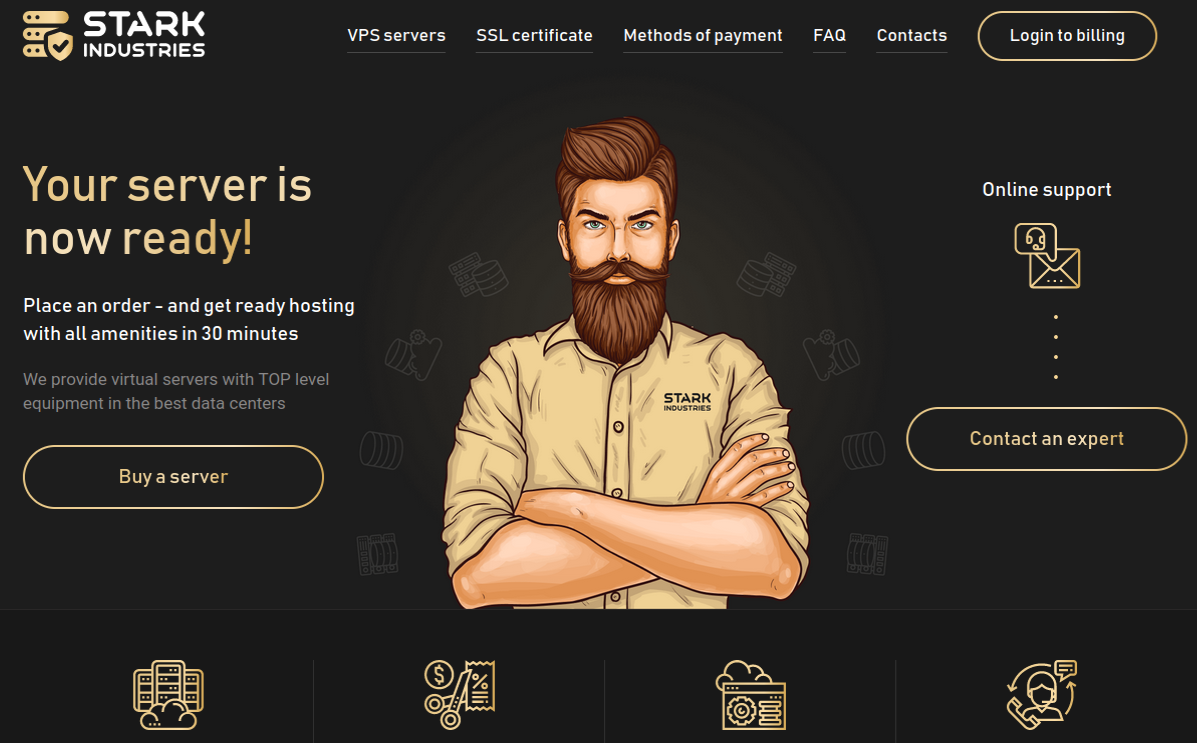
Stark Industries is integrated at a mail drop handle in the UK. UK enterprise data record an Ivan Vladimirovich Neculiti as the corporate’s secretary. Mr. Neculiti additionally is known as because the CEO and founding father of PQ Internet hosting Plus S.R.L. (aka Excellent High quality Internet hosting), a Moldovan firm shaped in 2019 that lists the identical UK mail drop handle as Stark Industries.

Ivan Neculiti, as pictured on LinkedIn.
Reached by way of LinkedIn, Mr. Neculiti mentioned PQ Internet hosting established Stark Industries as a “white label” of its model in order that “resellers might distribute our companies utilizing our IP addresses and their shoppers wouldn’t have any affairs with PQ Internet hosting.”
“PQ Internet hosting is an organization with over 1,000+ of [our] personal bodily servers in 38 international locations and we’ve got over 100,000 shoppers,” he mentioned. “Although we’re not as massive as Hetzner, Amazon and OVH, nonetheless we’re a quick rising firm that gives companies to tens of hundreds of personal prospects and authorized entities.”
Requested in regards to the fixed stream of DDoS assaults whose origins have traced again to Stark Industries over the previous two years, Neculiti maintained Stark hasn’t obtained any official abuse reviews about assaults coming from its networks.
“It was most likely some sort of intelligent assault that we didn’t see, I don’t rule out this truth, as a result of we’ve got a really massive variety of shoppers and our Web channels are fairly massive,” he mentioned. “However, on this state of affairs, sadly, nobody contacted us to report that there was an assault from our addresses; if somebody had contacted us, we’d have undoubtedly blocked the community knowledge.”
DomainTools.com finds Ivan V. Neculiti was the proprietor of battle[.]md, a web site launched in 2008 that chronicled the historical past of a 1990 armed battle in Moldova often called the Transnistria War and the Moldo-Russian battle.
An advert for battle.md, circa 2009.
Transnistria is a breakaway pro-Russian area that declared itself a state in 1990, though it isn’t internationally acknowledged. The copyright on that web site credit the “MercenarieS TeaM,” which was at one time a Moldovan IT agency. Mr. Neculiti confirmed personally registering this area.
DON CHICHO & DFYZ
The information breach monitoring service Constella Intelligence reviews that an Ivan V. Neculiti registered a number of on-line accounts beneath the e-mail handle [email protected]. Cyber intelligence agency Intel 471 exhibits this e mail handle is tied to the username “dfyz” on greater than a half-dozen Russian language cybercrime boards since 2008. The person dfyz on Searchengines[.]ru in 2008 requested different discussion board members to assessment battle.md, and mentioned they had been a part of the MercenarieS TeaM.
Again then, dfyz was promoting “bulletproof servers for any goal,” which means the internet hosting firm would willfully ignore abuse complaints or police inquiries in regards to the exercise of its prospects.
DomainTools reviews there are a minimum of 33 domains registered to [email protected]. A number of of those domains have Ivan Neculiti of their registration data, together with tracker-free[.]cn, which was registered to an Ivan Neculiti at [email protected] and referenced the MercenarieS TeaM in its authentic registration data.
Dfyz additionally used the nickname DonChicho, who likewise offered bulletproof internet hosting companies and entry to hacked Web servers. In 2014, a distinguished member of the Russian language cybercrime neighborhood Antichat filed a grievance towards DonChicho, saying this person scammed them and had used the e-mail handle [email protected].
The grievance mentioned DonChicho registered on Antichat from the Transnistria Web handle 84.234.55[.]29. Looking this handle in Constella reveals it has been used to register simply 5 accounts on-line which were created through the years, together with one at ask.ru, the place the person registered with the e-mail handle [email protected]. Constella additionally returns for that e mail handle a person by the identify “Ivan” at memoraleak.com and 000webhost.com.
Constella finds that the password most continuously utilized by the e-mail handle [email protected] was “filecast,” and that there are greater than 90 e mail addresses related to this password. Amongst them are roughly two dozen addresses with the identify “Neculiti” in them, in addition to the handle help@donservers[.]ru.
Intel 471 says DonChicho posted to a number of Russian cybercrime boards that help@donservers[.]ru was his handle, and that he logged into cybercrime boards virtually completely from Web addresses in Tiraspol, the capital of Transnistria. A assessment of DonChicho’s posts exhibits this individual was banned from a number of boards in 2014 for scamming different customers.
Cached copies of DonChicho’s self-importance area (donchicho[.]ru) present that in 2009 he was a spammer who peddled knockoff prescribed drugs by way of Rx-Promotion, as soon as one of many largest pharmacy spam moneymaking applications for Russian-speaking associates.
Mr. Neculiti informed KrebsOnSecurity he has by no means used the nickname DonChicho.
“I could guarantee you that I’ve no relation to DonChicho nor to his bulletproof servers,” he mentioned.
Beneath is a thoughts map that exhibits the connections between the accounts talked about above.
Earlier this 12 months, NoName started massively hitting authorities and business web sites in Moldova. A new report from Arbor Networks says the assaults started round March 6, when NoName alleged the federal government of Moldova was “longing for Russophobia.”
“Since early March, greater than 50 web sites have been focused, in accordance with posted ‘proof’ by the teams concerned in attacking the nation,” Arbor’s ASERT Group wrote. “Whereas NoName seemingly initiated the ramp of assaults, a bunch of different DDoS hacktivists have joined the fray in claiming credit score for assaults throughout greater than 15 industries.”
CORRECTIV ACTION
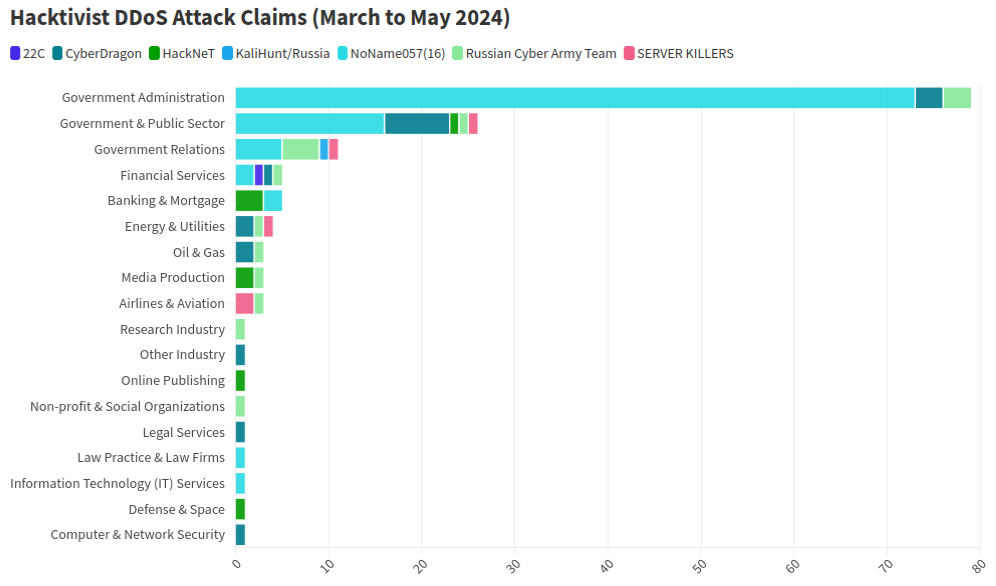
The German unbiased information outlet Correctiv.org final week printed a scathing investigative report on Stark Industries and MIRhosting, which notes that Ivan Neculiti operates his internet hosting corporations with the help of his brother, Yuri.
The report factors out that Stark Industries continues to host a Russian disinformation information outlet referred to as “Current Dependable Information” (RRN) that was sanctioned by the European Union in 2023 for spreading hyperlinks to propaganda blogs and pretend European media and authorities web sites.
“The web site was not operating on computer systems in Moscow or St. Petersburg till lately, however in the course of the EU, within the Netherlands, on the computer systems of the Neculiti brothers,” Correctiv reporters wrote.
“After a request from this editorial crew, a widely known service was put in that hides the precise internet host,” the report continues. “Ivan Neculiti introduced that he had blocked the related entry and server following inside investigations. “We very a lot remorse that we’re solely now discovering out that certainly one of our prospects is a sanctioned portal,” mentioned the corporate boss. Nonetheless, RRN remains to be accessible by way of its servers.”
Correctiv additionally factors to a January 2023 report from the Ukrainian authorities, which discovered servers from Stark Industries Options had been used as a part of a cyber assault on the Ukrainian information company “Ukrinform”. Correctiv notes the infamous hacker group Sandworm — a sophisticated persistent risk (APT) group operated by a cyberwarfare unit of Russia’s army intelligence service — was identified by Ukrainian government authorities as answerable for that assault.
PEACE HOSTING?
Public data point out MIRhosting relies in The Netherlands and is operated by 37-year previous Andrey Nesterenko, whose personal website says he’s an completed live performance pianist who started performing publicly at a younger age.
DomainTools says mirhosting[.]com is registered to Mr. Nesterenko and to Innovation IT Options Corp, which lists addresses in London and in Nesterenko’s acknowledged hometown of Nizhny Novgorod, Russia.
That is attention-grabbing as a result of in accordance with the e book Inside Cyber Warfare by Jeffrey Carr, Innovation IT Options Corp. was answerable for internet hosting StopGeorgia[.]ru, a hacktivist web site for organizing cyberattacks towards Georgia that appeared on the similar time Russian forces invaded the former Soviet nation in 2008. That battle was considered the primary battle ever fought through which a notable cyberattack and an precise army engagement occurred concurrently.
Responding to questions from KrebsOnSecurity, Mr. Nesterenko mentioned he couldn’t say whether or not his community had ever hosted the StopGeorgia web site again in 2008 as a result of his firm didn’t hold data going again that far. However he mentioned Stark Industries Options is certainly certainly one of MIRhsoting’s colocation prospects.
“Our relationship is only provider-customer,” Nesterenko mentioned. “Additionally they make the most of a number of suppliers and knowledge facilities globally, so connecting them on to MIRhosting overlooks their broader community.”
“We take any report of malicious exercise significantly and are at all times open to data that may assist us establish and stop misuse of our infrastructure, whether or not involving Stark Industries or some other buyer,” Nesterenko continued. “In instances the place our companies are exploited for malicious functions, we collaborate totally with Dutch cyber police and different related authorities to analyze and take acceptable measures. Nonetheless, we’ve got but to obtain any actionable data past the article itself, which has not offered us with ample element to establish or block malicious actors.”
In December 2022, safety agency Recorded Future profiled the phishing and credential harvesting infrastructure used for Russia-aligned espionage operations by a gaggle dubbed Blue Charlie (aka TAG-53), which has focused e mail accounts of nongovernmental organizations and suppose tanks, journalists, and authorities and protection officers.
Recorded Future discovered that just about all of the Blue Charlie domains existed in simply ten completely different ISPs, with a major focus positioned in two networks, certainly one of which was MIRhosting. Each Microsoft and the UK government assess that Blue Charlie is linked to the Russian risk exercise teams variously often called Callisto Group, COLDRIVER, and SEABORGIUM.
Mr. Nesterenko took exception to Recorded Future’s report.
“We’ve mentioned its contents with our buyer, Stark Industries,” he mentioned. “We perceive that they’ve initiated authorized proceedings towards the web site in query, as they firmly consider that the claims made are inaccurate.”
Recorded Future mentioned they up to date their story with feedback from Mr. Nesterenko, however that they stand by their reporting.
Mr. Nesterenko’s LinkedIn profile says he was beforehand the international area gross sales supervisor at Serverius-as, a internet hosting firm in The Netherlands that continues to be in the identical knowledge heart as MIRhosting.
In February, the Dutch police took 13 servers offline that had been utilized by the notorious LockBit ransomware group, which had initially bragged on its darknet website that its residence base was in The Netherlands. Sources inform KrebsOnSecurity the servers seized by the Dutch police had been positioned in Serverius’ knowledge heart in Dronten, which can also be shared by MIRhosting.
Serverius-as didn’t reply to requests for remark. Nesterenko mentioned MIRhosting does use certainly one of Serverius’s knowledge facilities for its operations within the Netherlands, alongside two different knowledge facilities, however that the current incident involving the seizure of servers has no connection to MIRhosting.
“We’re legally prohibited by Dutch regulation and police rules from sharing data with third events relating to any communications we could have had,” he mentioned.
A February 2024 report from safety agency ESET found Serverius-as methods had been concerned in a sequence of focused phishing assaults by Russia-aligned teams towards Ukrainian entities all through 2023. ESET noticed that after the spearphishing domains had been not lively, they had been transformed to selling rogue Web pharmacy web sites.
PEERING INTO THE VOID
A assessment of the Web handle ranges lately added to the community operated by Stark Industries Options presents some perception into its buyer base, utilization, and perhaps even true origins. Here is a snapshot (PDF) of all Web handle ranges introduced by Stark Industries to date within the month of Might 2024 (this data was graciously collated by the community observability platform Kentik.com).
These data point out that the most important portion of the IP area utilized by Stark is in The Netherlands, adopted by Germany and the USA. Stark says it’s linked to roughly 4,600 Web addresses that presently record their possession as Comcast Cable Communications.
A assessment of these handle ranges at spur.us exhibits all of them are linked to an entity referred to as Proxyline, which is a sprawling proxy service based mostly in Russia that presently says it has greater than 1.6 million proxies globally which can be obtainable for lease.

Proxyline dot internet.
Reached for remark, Comcast mentioned the Web handle ranges by no means did belong to Comcast, so it’s doubtless that Stark has been fudging the actual location of its routing bulletins in some instances.
Stark reviews that it has greater than 67,000 Web addresses at Santa Clara, Calif.-based EGIhosting. Spur says the Stark addresses involving EGIhosting all map to Proxyline as nicely. EGIhosting didn’t reply to requests for remark.
EGIhosting manages Web addresses for the Cyprus-based internet hosting agency ITHOSTLINE LTD (aka HOSTLINE-LTD), which is represented all through Stark’s introduced Web ranges. Stark says it has greater than 21,000 Web addresses with HOSTLINE. Spur.us finds Proxyline addresses are particularly concentrated within the Stark ranges labeled ITHOSTLINE LTD, HOSTLINE-LTD, and Proline IT.
Stark’s community record contains roughly 21,000 Web addresses at Hockessin, De. based mostly DediPath, which abruptly ceased operations without warning in August 2023. Based on a phishing report launched final 12 months by Interisle Consulting, DediPath was the fourth commonest supply of phishing assaults within the 12 months ending Oct. 2022. Spur.us likewise finds that just about the entire Stark address ranges marked “DediPath LLC” are tied to Proxyline.
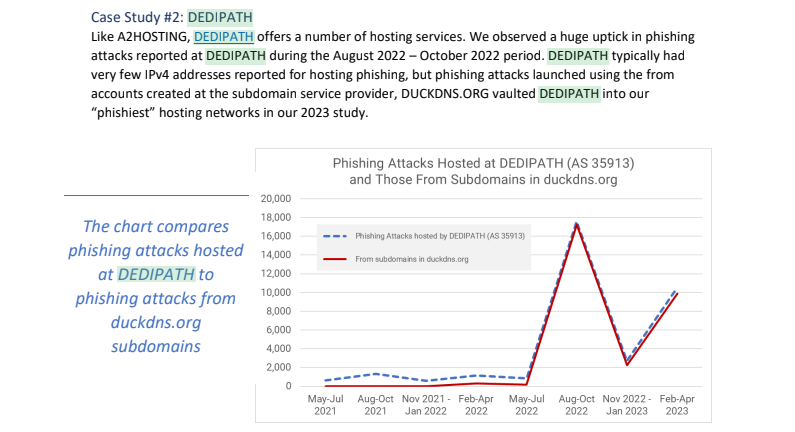
Picture: Interisle Consulting.
A lot of the Web handle ranges introduced by Stark in Might originate in India, and the names which can be self-assigned to many of those networks point out they had been beforehand used to ship massive volumes of spam for natural medicinal merchandise, with names like HerbalFarm, AdsChrome, Nutravo, Herbzoot and Herbalve.
The anti-spam group SpamHaus reports that lots of the Indian IP handle ranges are related to identified “snowshoe spam,” a type of abuse that entails mass e mail campaigns unfold throughout a number of domains and IP addresses to weaken popularity metrics and keep away from spam filters.
It’s not clear how a lot of Stark’s community handle area traces its origins to Russia, however massive chunks of it lately belonged to a few of the oldest entities on the Russian Web (a.ok.a. “Runet”).
For instance, many Stark handle ranges had been most lately assigned to a Russian authorities entity whose full identify is the “Federal State Autonomous Instructional Institution of Extra Skilled Training Heart of Realization of State Instructional Coverage and Informational Applied sciences.”
A assessment of Internet address ranges adjacent to this entity reveals a protracted record of Russian authorities organizations which can be a part of the Federal Guard Service of the Russian Federation. Wikipedia says the Federal Guard Service is a Russian federal authorities company involved with duties associated to safety of a number of high-ranking state officers, together with the President of Russia, in addition to sure federal properties. The company traces its origins to the USSR’s Ninth Directorate of the KGB, and later the presidential safety service.
Stark lately introduced the handle vary 213.159.64.0/20 from April 27 to Might 1, and this vary was beforehand assigned to an historic ISP in St. Petersburg, RU referred to as the Laptop Applied sciences Institute Ltd.
Based on a put up on the Russian language webmaster discussion board searchengines[.]ru, the area for Laptop Applied sciences Institute — ctinet[.]ru — is the seventh-oldest area in your entire historical past of the Runet.
Curiously, Stark additionally lists massive tracts of Web addresses (near 48,000 in whole) assigned to a small ISP in Kharkiv, Ukraine referred to as NetAssist. Reached by way of e mail, the CEO of NetAssist Max Tulyev confirmed his firm offers numerous companies to PQ Internet hosting.
“We colocate their gear in Warsaw, Madrid, Sofia and Thessaloniki, present them IP transit and IPv4 addresses,” Tulyev mentioned. “For his or her measurement, we obtain comparatively low variety of complains to their networks. I by no means seen something about their pro-Russian exercise or help of Russian hackers. It is vitally attention-grabbing for me to see proofs of your accusations.”
Spur.us mapped your entire infrastructure of Proxyline, and located a couple of million proxies throughout a number of suppliers, however by far the largest focus was at Stark Industries Options. The full list of Proxyline address ranges (.CSV) exhibits two different ISPs seem repeatedly all through the record. One is Kharkiv, Ukraine based mostly ITL LLC, often known as Data Expertise Laboratories Group, and Built-in Applied sciences Laboratory.
The second is a associated internet hosting firm in Miami, referred to as Inexperienced Floid LLC. Inexperienced Floid featured in a 2017 scoop by CNN, which profiled the corporate’s proprietor and quizzed him about Russian troll farms utilizing proxy networks on Inexperienced Floid and its guardian agency ITL to masks disinformation efforts tied to the Kremlin’s Internet Research Agency (IRA). On the time, the IRA was utilizing Fb and different social media networks to unfold movies exhibiting police brutality towards African Individuals in an effort to encourage protests throughout the USA.

Doug Madory, director of Web evaluation at Kentik, was capable of see at a excessive stage the highest sources and locations for visitors traversing Stark’s community.
“Primarily based on our mixture NetFlow, we see Iran as the highest vacation spot (35.1%) for visitors emanating from Stark (AS44477),” Madory mentioned. “Particularly, the highest vacation spot is MTN Irancell, whereas the highest supply is Fb. This knowledge helps the speculation that AS44477 homes proxy companies as Fb is blocked in Iran.”