A worldwide operation known as Emeraldwhale has focused misconfigured Git configurations, ensuing within the theft of over 15,000 cloud service credentials.
Based on the Sysdig Menace Analysis Staff (TRT), attackers used a mix of personal instruments to use misconfigured net providers, gaining unauthorized entry to cloud credentials, cloning personal repositories and extracting delicate data.
Scale of the Breach
This breach allowed entry to over 10,000 personal repositories, with the stolen information saved in an Amazon S3 bucket linked to a previous sufferer.
The uncovered credentials embody a big selection of providers, together with cloud service suppliers (CSPs) and e mail platforms, with phishing and spam campaigns cited as major motivations for the theft.
Along with direct use, these stolen credentials are helpful on underground marketplaces, the place they might fetch a whole bunch of {dollars} per account.
Instruments and Methods Utilized by Attackers
Preliminary indicators of this breach appeared when Sysdig TRT’s cloud honeypot detected an unauthorized ListBuckets name, resulting in the invention of a compromised S3 bucket containing over a terabyte of delicate information. The investigation revealed instruments able to scraping uncovered Git configuration recordsdata and different net information, together with Laravel .env recordsdata, to reap credentials.
Emeraldwhale’s toolset automates scanning, extracting and validating stolen tokens, permitting attackers to clone private and non-private repositories whereas trying to find extra credentials inside.
In reference to the toolset, a large-scale scanning marketing campaign focused uncovered Git configuration recordsdata throughout 1000’s of servers, enabled by freely out there open-source instruments equivalent to httpx. This operation highlights the safety danger posed by .git directories uncovered attributable to net server misconfigurations, which attackers exploited to retrieve delicate repository data.
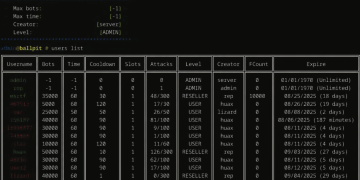
The marketplace for credential-harvesting instruments, together with MZR V2 and Seyzo-v2, is prospering, with these instruments enabling the automation of IP scanning and credential extraction for spam and phishing campaigns.
These instruments are available in underground markets, the place they’re typically bundled with programs on credential theft ways.
“The underground marketplace for credentials is booming, particularly for cloud providers. This assault reveals that secret administration alone is just not sufficient to safe an atmosphere. There are simply too many locations credentials might leak from,” Sysdig warned. “Monitoring the conduct of any identities related to credentials is changing into a requirement to guard in opposition to these threats.”













8vu5gs