Cyble researchers have found a brand new Android banking trojan that makes use of overlay assaults and different methods to focus on greater than 750 purposes, together with banking, finance, cryptocurrency, cost, social media, and e-commerce purposes.
Dubbed “TsarBot” due to the risk actor’s suspected Russian origin, the malware makes use of overlay assaults to steal credentials and may also file and management the display screen. Different assault methods utilized by the malware embody lock-grabbing, keylogging, and intercepting SMS messages. Abusing Accessibility providers and WebSocket communications helps the malware preserve a low profile.
TsarBot Unfold Via Phishing Websites
TsarBot was noticed spreading by means of a phishing website that impersonates the official Photon Sol token discovery and buying and selling website.
“The phishing website deceptively presents a obtain choice for an software to begin buying and selling, whereas the respectable web site lacks such an choice,” Cyble famous in a blog post detailing the findings.
Three phishing websites deploying TsarBot have been recognized by the researchers, together with solphoton[.]io, solphoton[.]app, and cashraven[.]on-line.
The phishing websites ship a dropper software that shops the TsarBot APK file, implant.apk, within the “res/uncooked” folder, and makes use of a session-based bundle installer to deploy the TsarBot malware on the gadget.
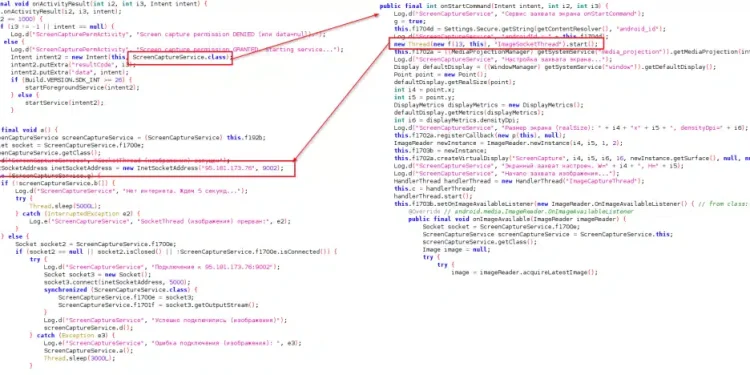
After deployment, TsarBot presents a fake Google Play Service update page that prompts the user to enable Accessibility services, which establishes a socket connection with the command and control (C&C) server using ports 9001, 9002, 9004 and 9030.
“By abusing Accessibility services and WebSocket communication, it enables on-device fraud whereas sustaining a low profile,” the Cyble researchers wrote.
TsarBot Actions Embrace Fraud, Password Theft
Cyble recognized about 30 instructions that TsarBot can obtain from the server, primarily targeted on on-screen management to hold out on-device fraud.
The “REQUEST_CAPTURE” command, for instance, prompts the person to allow display screen seize permissions.
“As soon as granted, the malware initiates the display screen seize service, transmitting the captured display screen content material to the C&C server by way of a WebSocket connection on port 9002,” the researchers wrote. “By capturing display screen content material and executing server-issued display screen management instructions, TsarBot can perform fraudulent transactions on the focused gadget by concealing this fraud exercise with a black overlay display screen.”
TsarBot’s LockTypeDetector function determines the gadget’s lock kind utilizing the Accessibility service. “As soon as recognized, it saves the lock kind standing for future use in lock-grabbing operations,” Cyble mentioned.
When TsarBot receives the “USER_PRESENT” motion for the primary time, it masses a faux lock display screen primarily based on the lock kind and captures the person’s lock password, PIN, or sample.
Mimicking Purposes
TsarBot retrieves a listing of focused software bundle names, most of which belong to regional banking apps from international locations resembling France, Poland, the UK, India, the UAE, and Australia. Different bundle names are related to e-commerce, social media, messaging, cryptocurrency, and different apps.
TsarBot collects the put in purposes on the gadget and compares them towards the bundle names, “sustaining a goal listing for overlay assaults,” Cyble mentioned.
“The injection web page mimics a respectable software, tricking customers into getting into delicate info resembling web banking credentials, log in particulars, and bank card info,” Cyble mentioned. “After transmitting the stolen delicate info, TsarBot removes the focused software’s bundle identify from the listing to forestall the overlay from being triggered once more for a similar app.”
Cyble mentioned the malware drives dwelling the significance of finest practices resembling solely downloading software program from official software shops, such because the Google Play Retailer or the iOS App Retailer; utilizing robust passwords, multi-factor authentication and biometric security; enabling Google Play Shield; and exercising warning whereas opening hyperlinks which were despatched by way of SMS or emails.
The total Cyble blog consists of extra particulars, resembling indicators of compromise (IoC) and MITRE ATT&CK technoques.
Associated
Media Disclaimer: This report is predicated on inner and exterior analysis obtained by means of varied means. The data supplied is for reference functions solely, and customers bear full accountability for his or her reliance on it. The Cyber Express assumes no legal responsibility for the accuracy or penalties of utilizing this info.